Cybersecurity Snapshot: CISA Pinpoints Vulnerabilities in Critical Infrastructure Orgs that Ransomware Groups Could Exploit

Learn about CISA’s new program to help critical infrastructure organizations stamp out vulnerabilities associated with ransomware attacks. Plus, a U.S. government advisory with the latest on LockBit 3.0. Also, find out why the U.K.’s cyber agency is warning users about ChatGPT. Et bien plus encore !
Dive into six things that are top of mind for the week ending March 17.
1 - CISA program helps critical infrastructure orgs fend off ransomware attackers
LeCybersecurity and Infrastructure Security Agency (CISA) is intensifying its efforts to help reduce ransomware attacks against critical infrastructure.
With its new Ransomware Vulnerability Warning Pilot (RVWP) program, CISA probes internet-facing assets from critical infrastructure organizations and alerts them when it detects vulnerabilities that ransomware gangs commonly compromise.
The agency identifies vulnerable assets by using “existing services, data sources, technologies, and authorities,” CISA said this week in its announcement of the program.

In its first round of RVWP notifications earlier this year, CISA alerted 93 critical infrastructure organizations that they had Microsoft Exchange instances with the ProxyNotShell vulnerability. CISA’s RVWP notifications are made via email and phone, and the critical infrastructure organizations receiving them aren’t required to act on them.
“The RVWP will allow CISA to provide timely and actionable information that will directly reduce the prevalence of damaging ransomware incidents affecting American organizations,” said Eric Goldstein, CISA’s executive assistant director for cybersecurity.
A few weeks ago, a CISA red team launched a simulated attack against a large, critical infrastructure organization in the U.S. with a “mature cyber posture” and successfully breached its network using a variety of methods, including spear-phishing emails.
For more information, check out CISA’s description of the RVWP program, as well as coverage from The Record, CyberScoop, GCN, SC Magazine and NextGov.
VIDEOS
Tenable.ot Security Spotlight - Episode 1: The Ransomware Ecosystem (Tenable)
How the Nation’s Energy Organizations Can Stand Up to Ransomware Threats (CISA)
2 - FBI shines light on ransomware threat to critical infrastructure
And continuing with this topic, we’re also learning from the U.S. Federal Bureau of Investigation that ransomware attacks impacted almost all 16 critical infrastructure sectors in 2022, with healthcare/public health and critical manufacturing the most affected.
That’s according to the FBI’s new “Internet Crime Report” for 2022, which is based on cyber incidents reported to its Internet Crime Complaint Center (IC3).
Infrastructure Sectors Victimized by Ransomware
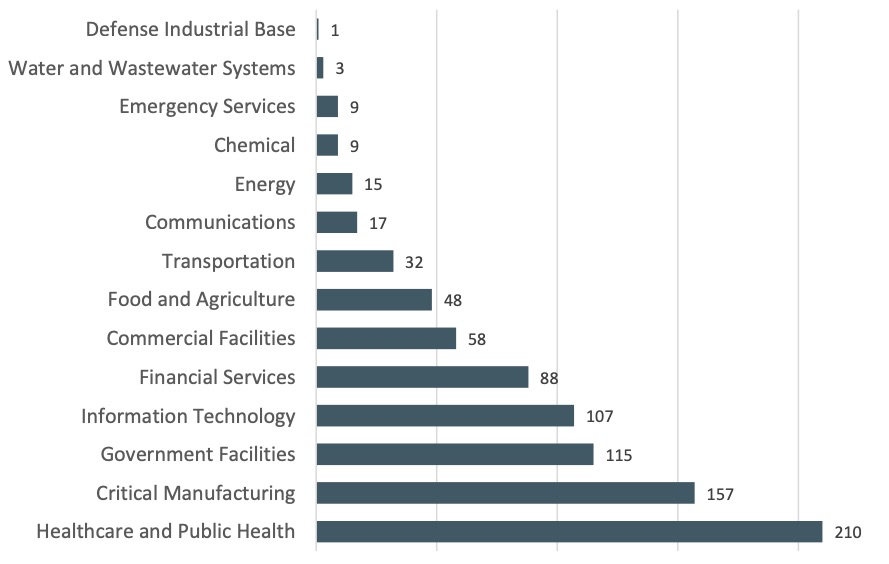
(Source : FBI’s “Internet Crime Report” for 2022, March 2023)
The top ransomware variants attackers used against critical infrastructure organizations were LockBit, ALPHV/BlackCat and Hive.
In terms of overall ransomware complaints, the IC3 received almost 2,400 in 2022 leading to adjusted losses of about $34 million, a drop compared with 2021. However, the number of ransomware incidents and their financial impact were likely much higher. Many attacks go unreported and, when reported, victims often don’t attach a monetary loss estimate to them, according to the FBI.
“As such, we assess ransomware remains a serious threat to the public and to our economy,” the report reads.
To reduce ransomware risk, common sense recommendations in the report include:
- Updating operating systems and software in general
- Conducting user training and phishing exercises
- Securing and monitoring Remote Desktop Protocol (RDP)
- Having an offline backup of your data
Other findings from the report include:
- Overall, internet crime complaints dropped 5% to little over 800,000 in 2022, but the potential total loss ballooned from $6.9 billion in 2021 to $10.3 billion.
- Investment fraud topped the monetary loss category, costing some 30,500 victims $3.3 billion, up 127% from 2021. Cryptocurrency investment fraud accounted for most of these losses: $2.57 billion, up 183%.
- Business email compromise (BEC) came in second, with about $2.7 billion in adjusted losses and about 22,000 victims.
- In terms of crime types, phishing was the runaway winner with just over 300,000 victims, followed by personal data breach with almost 59,000.
Complaints and Losses Over the Last Five Years
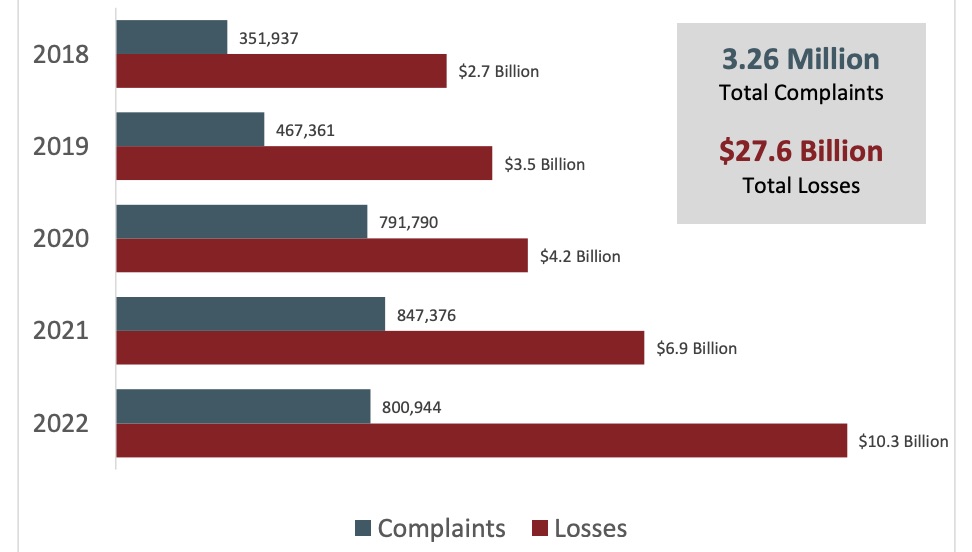
(Source : FBI’s “Internet Crime Report” for 2022, March 2023)
For more information, read the full report and a special FBI warning about crypto investment schemes, as well as coverage from Help Net Security, SC Magazine, The Wall Street Journal and Bank Info Security.
3 - CISA: Get hip to LockBit 3.0
Staying on the ransomware topic, CISA, the FBI and the Multi-State Information Sharing & Analysis Center (MS-ISAC) this week issued a joint advisory about the indicators of compromise (IOCs) and techniques, tactics and procedures (TTPs) of LockBit 3.0, which is “more modular and evasive” than its earlier versions.

LockBit 3.0’s operations use the ransomware-as-a-service (RaaS) model and represent a threat to “a wide range of businesses and critical infrastructure organizations,” says the advisory, which goes into granular technical details about this latest version of the ransomware and offers detailed mitigation recommendations.
For more information about ransomware, check out these Tenable resources:
- “2022 Threat Landscape Report”
- “FBI and CISA Release Cybersecurity Advisory on Royal Ransomware Group” (blog)
- “The Ransomware Ecosystem” (report)
- “Understanding the Ransomware Ecosystem” (blog)
- “Tenable’s Ransomware Ecosystem Report” (on-demand webinar)
- “The Ransomware Ecosystem: In Pursuit of Fame and Fortune” (blog)
4 - Google survey: Cyber pros think cloud helps boost security
Although moving to the cloud involves complexity and risk, it creates opportunities for cyber teams to significantly improve security.
That’s the main finding from a recent Google report for which 400 security leaders and security ops practitioners in North America were polled.
Specifically, more respondents said that cloud security is harder (37%) and riskier (48%) than on-prem security. However, a majority said that the cloud offers greater opportunities to strengthen security, thanks to factors such as richer telemetry and more automation possibilities.
Reasons Cloud vs. On-prem Differ
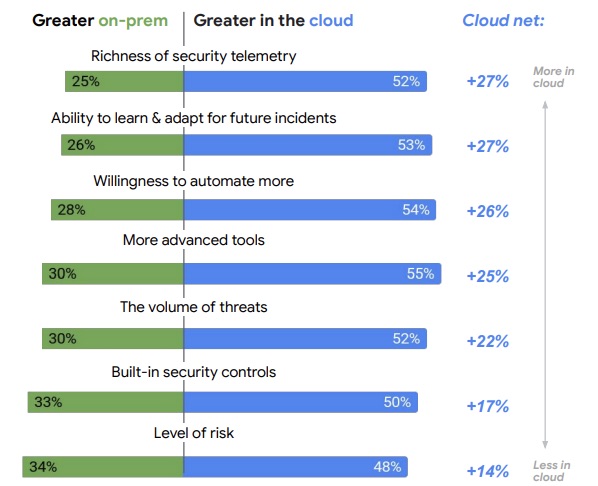
(Source : Google’s “State of Cloud Threat Detection and Response Report,” March 2023)
The report also found that there’s a need to beef up cloud computing expertise among cyber pros. While 63% of respondents said their SecOps teams are well staffed, 82% feel their organization must boost its public cloud skills.
The report, from Google’s Cybersecurity Action Team, offers recommendations for secure cloud migrations, including:
- Take inventory of what will need securing in the cloud, including virtual servers, containers and APIs
- Make sure you get identity and access management (IAM) right, as detecting access anomalies in the cloud is key.
- Ponder how cloud processes and technologies offer new opportunities to rethink how to achieve your security goals.
For more information, you can read the full “State of Cloud Threat Detection and Response Report,” and a blog about it.
VIDEOS
What is Cloud Security and Why Do You Need It? (TechTarget)
Top Cloud Threats of 2022 - Tenable Cloud Security Coffee Break (Tenable)
5 - U.K. cyber agency: Tread carefully when feeding data to ChatGPT
Users shouldn’t put sensitive or confidential information about themselves or their employer into public generative AI chatbots like ChatGPT.
That’s one of the warnings that the U.K. National Cyber Security Centre (NCSC) issued this week about generative AI chatbots in its blog “ChatGPT and large language models: what's the risk?”
Information entered into generative AI chatbots via their prompts is collected by and visible to the chatbots’ owners – and could be used to further develop the product in the future. Plus, this private data could become public if a chatbot’s systems aren’t properly secured and it gets hacked or inadvertently exposes the information, the NCSC warned.

The agency recommends carefully reading the terms of use and the privacy policy of generative AI chatbots, whether they’re publicly available like ChatGPT or “private” ones that cloud vendors offer commercially.
The latter – cloud-provided AI chatbots – will likely be better suited than public ones for queries involving sensitive information, assuming users do a thorough due diligence in assessing their terms of use, privacy policy and data-protection safeguards, according to the NCSC.
Questions customers should ask a cloud-provided generative AI operator include:
- How does it manage the data that users enter into query prompts?
- Is this data available to its researchers or partners – and if so, in what form?
- Can its employees view user queries – and if so, under what circumstances?
Of course, organizations would have the most control over self-hosted generative AI chatbots, but those cost a lot to set up and maintain, and are thus out of the reach of most businesses right now.
For more information about security concerns around generative AI chatbots, check out this Ticker Insight interview with Tenable’s Senior Principal Security Advocate Nathan Wenzler, as well as these recent Tenable blogs:
- “A ChatGPT Special Edition About What Matters Most to Cyber Pros”
- “Check Out Our No-Holds-Barred Interview with ChatGPT”
- “As ChatGPT Fire Rages, NIST Issues AI Security Guidance”
- “ChatGPT gets jailbroken … and heartbroken?”
VIDEOS
ChatGPT: Artificial Intelligence, chatbots and a world of unknowns (60 Minutes)
What You Need to Know About OpenAI's New ChatGPT Bot and How It Affects Security (SANS Institute)
6 - Rinse and repeat: Fix critical known vulnerabilities
And here’s an incident post-mortem that serves as the latest and umpteenth reminder to remediate known vulnerabilities for which patches have been available for months or years.
In an advisory this week, CISA details how multiple attackers breached the web server of an unnamed U.S. federal agency by exploiting known, years-old vulnerabilities. The suspicious activity was detected between November 2022 and January 2023, but the breach apparently happened as far back as August 2021.
Specifically, the attackers exploited a .NET deserialization vulnerability (CVE-2019-18935) in Progress’ Telerik UI for ASP.NET AJAX located in the agency’s Microsoft Internet Information Services (IIS) web server. CISA believes the vulnerability was exploited in conjunction with at least one of several even older vulnerabilities present in the version of the product in question: 2013.2.717. Telerik patched the vulnerability starting with version 2020.1.114.
To do a deep dive into the importance of fixing known, critical vulnerabilities on a timely basis, check out the newly-released “2022 Threat Landscape Report” from Tenable’s Security Response Team (SRT).
“We cannot stress this enough: Threat actors continue to find success with known and proven exploitable vulnerabilities that organizations have failed to patch or remediate successfully,” the Tenable report reads.
To get more details, you can check out the full “Threat Landscape Report,” read an SRT blog post and watch an on-demand webinar.
En savoir plus
- Cloud
- Cybersecurity Snapshot
- Exposure Management
- OT Security
- Public Policy
- Risk-based Vulnerability Management
- Vulnerability Management




Tenable One
Demandez une démo
La plateforme de gestion de l'exposition alimentée par l'IA leader du secteur
Merci
Nous vous remercions de votre intérêt pour Tenable One.
Un représentant vous contactera prochainement.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success