by Cody Dumont
Many organizations have a difficult time keeping software completely up to date with patches due to the frequency in which they are released. Outstanding vulnerabilities can be exploited by attackers, which can result in business outages or loss of revenue. This report provides a summary of the most prevalent vulnerabilities published more than a year ago.
Despite best intentions, not all vulnerabilities are patched on a constant basis throughout the organization. For example, analysts may find vulnerabilities through active scanning, but may not have the immediate resources or time to address the issues found. Vulnerabilities increase risk to the organization and may cause business outages, data leakage, or loss of revenue if the issues are not remediated. Risk managers can use this report to find vulnerabilities published more than 1 year ago and pose great risk to their organization. The hosts displayed most likely exist outside of a regular patch cycle and indicate missed mitigation efforts.
This report provides a summary of vulnerabilities and affected hosts, helping to optimize prioritization efforts for remediation. Analysts can quickly see the vulnerabilities that are long standing and have a high CVSS rating, or are affecting a large number of hosts. Resources can be better utilized when they are effectively remediating hosts in the organization by using a risk-focused approach.
The data shown in these tables is based on "vulnerability publication date," not to be confused with the "plugin publication date." The vulnerability publication date is when the vulnerability became known and assigned a CVSS score by the National Vulnerability Database (NVD). Both dates are visible on the plugin details. The report supports filters from the Nessus user interface, which are reflected in the output report. In the Nessus user interface, the analyst can use filters either by host or vulnerability. For example, by setting a filter for hosts that contain “192.168.0.”, the output of the report will be limited to the specified network. This allows risk managers to identify risks based on subnet or other data attributed collected by Nessus. This report template is available for Nessus Professional PDF or HTML reports.
Tenable built the most innovative vulnerability scanner, Nessus, which is the world's most widely deployed vulnerability assessment scanner. Powerful and flexible to adapt to the unique requirements of today's modern networks. Nessus provides visibility into a wide range of assets on many computing platforms. The data in this report provides insight into user account and group membership information.
This report contains the following chapters:
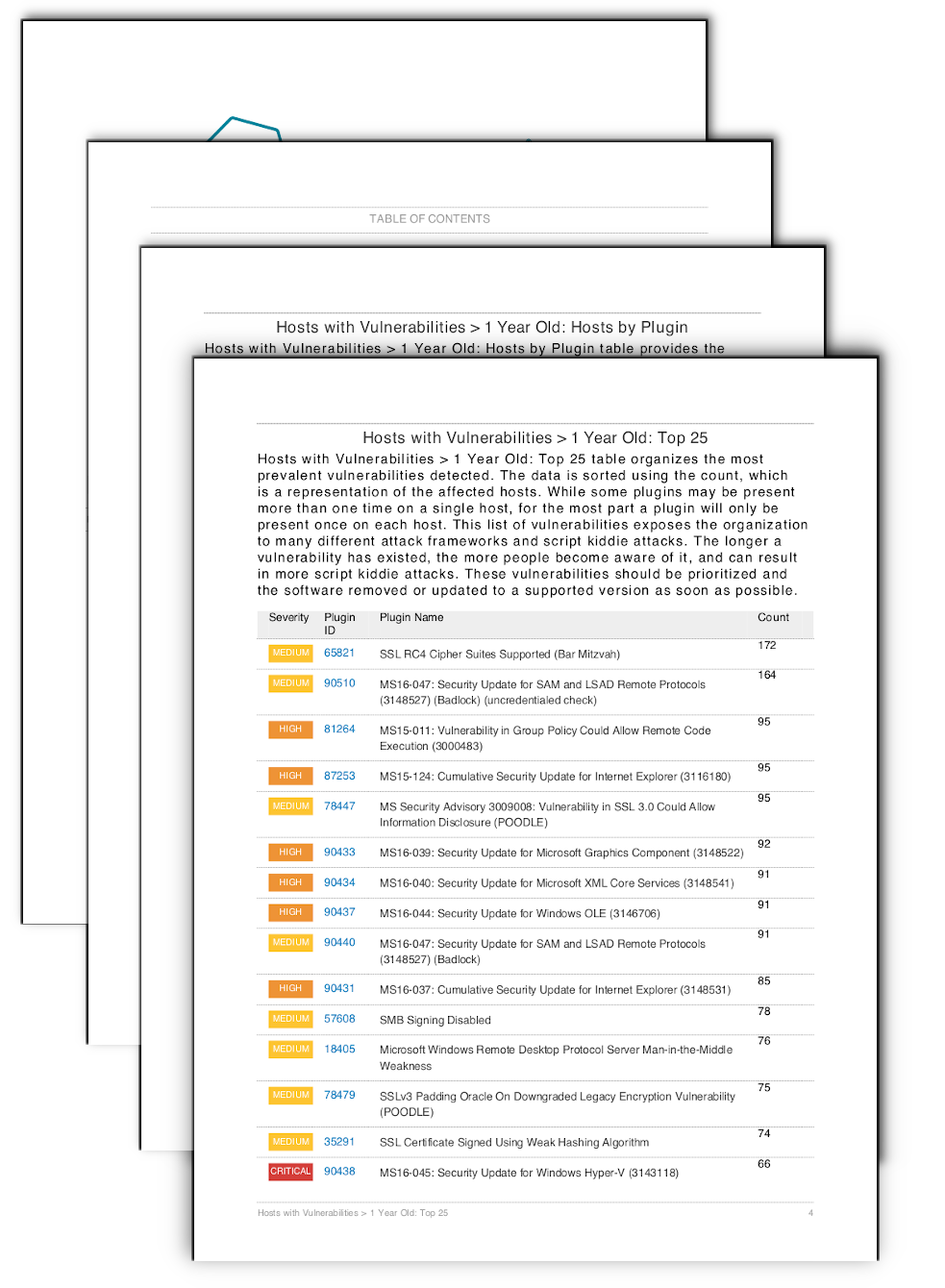
Hosts with Vulnerabilities > 1 Year Old: Top 25 - Hosts with Vulnerabilities > 1 Year Old: Top 25 table organizes the most prevalent vulnerabilities detected. The data is sorted using the count, which is a representation of the affected hosts. While some plugins may be present more than one time on a single host, a plugin is usually only present once on each host. This list of vulnerabilities exposes the organization to many different attack frameworks and script kiddie attacks. The longer a vulnerability has existed, the more time adversaries have to develop exploits, which can result in more script kiddie attacks. These vulnerabilities should be prioritized and the software removed or updated to a supported version as soon as possible.
Hosts with Vulnerabilities > 1 Year Old: Hosts by Plugin - Hosts with Vulnerabilities > 1 Year Old: Hosts by Plugin table provides the IT operations team with an action plan and the identified hosts for each vulnerability. IT managers can use this information to plan patch deployments and work with the information security team in risk mitigation efforts. The table provides all detected vulnerabilities and sorts the scan results using severity, then plugin ID. The entries in the "Hosts" column are then sorted in ascending order.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success