Pig Butchering Scam: How Bitcoin, Ethereum, Litecoin and Spot Gold (XAUUSD) Investments Are Used in Romance Scams to Steal Hundreds of Millions
This is the second part of a two-part series based on firsthand research into pig butchering scams from the end of 2022 into early 2024. In this post, we delve into the types of investment scams perpetrated by pig butchers to steal hundreds of millions of dollars from victims, including in the form of cryptocurrency and spot gold.
Tenable researchers Jessie Jamieson and Ziga Cerkovnik assisted this research through compiling and analyzing Ethereum blockchain transaction data associated with the pig butchering scams I encountered firsthand.
Contexte
In February 2024, the U.S. Federal Trade Commission (FTC) released data showing that U.S. consumers reported losses of $10 billion to scams in 2023, up from $8.8 billion lost to scams in 2022. Losses linked to investment scams have steadily increased over the last three years, from $1.7 billion in 2021, $3.8 billion in 2022 and $4.6 billion in 2023. Subsequently, the FBI’s Internet Crime Complaint Center (IC3) reported that investment fraud was the leading cause of complaints for 2022, with losses climbing to over $3.31 billion, a 183% increase from the $2.57 billion recorded in 2021.
Pig butchering, a type of scam that overlaps between romance and investment scams, is a vastly lucrative scheme that has enabled scammers to steal hundreds of millions of dollars over the last few years around the world. However, the true cost of pig butchering scams is difficult to quantify because of many factors: the blurred lines between these two types of fraud; an inability to view and analyze transactions made on attacker-controlled platforms and mobile apps; and lack of reporting from victims of pig butchering scams due to shame and embarrassment.
This is the second part of a two-part blog series that details my firsthand research into these scams from late 2022 to early 2024. The first part was a primer on what pig butchering is and how these pig butchers target users on various online platforms. In this second part, I detail the types of financial fraud the scammers use to steal money from their victims, which includes falsified cryptocurrency investments.
As part of my investigation into these pig butchering scams, I tracked multiple cryptocurrency addresses, a unique identifier tied to a digital wallet containing cryptocurrency tokens, shared with me by scammers operating fake cryptocurrency platforms. Based on my analysis, I can say with high confidence these scams were associated with losses totaling nearly $13 million dollars. That said, I believe this is a conservative estimate and that the true losses incurred during the time I monitored these scams were much higher. That’s because there was a web of cryptocurrency addresses that showed a greater volume of cryptocurrency and stable coins being transferred between cryptocurrency addresses that I couldn’t independently verify.
Sommaire
- What are the methods pig butchers use to steal money from users?
- The pig butchers ask me to buy cryptocurrency from Coinbase, Binance, Crypto.com, Kraken, Gemini, Uniswap, or peer-to-peer payment platforms including Cash App, PayPal and Venmo. Why don’t they want me to use their websites to purchase cryptocurrency?
- Do pig butchers expect me to know about these financial investments like cryptocurrency or spot gold?
- Why do the pig butchers ask me to send them screenshots from the apps?
- How can I spot pig butchering scams and what can I do to help stop them?
- Conclusion
What are the methods pig butchers use to steal money from users?
This list is representative only of the types of scams I encountered during my research, and is accurate as of February 2024. It’s not an exhaustive list.
- Fake investment sites manipulated by the pig butchers
- Fake cryptocurrency investment sites with Bitcoin and Ethereum addresses
- Spot gold trading through MetaTrader application
Fake investment sites manipulated by the pig butchers
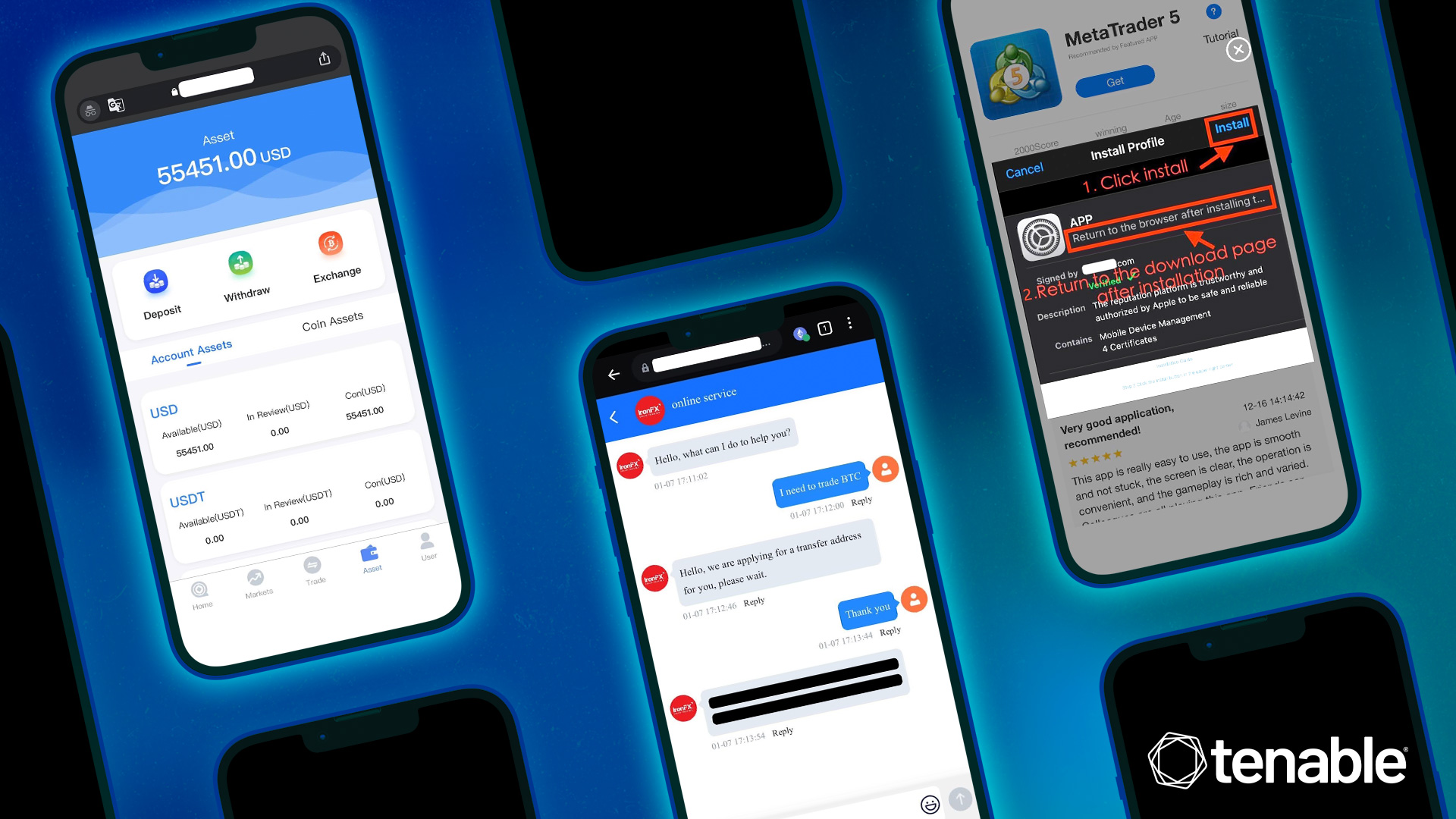
Pig butchers create these fake investment sites to look legitimate by almost identically copying the HTML code from real investment sites. In an example I encountered, they used a fake version of Upbit, a South Korean cryptocurrency exchange.

The sites aren’t a complete dupe, as there are slight variations in the price of cryptocurrencies. My assumption is that this discrepancy could be leveraged by the pig butchers in order to demonstrate fake profits to their victims.
Based on first-hand interaction with these websites, it’s clear the pig butchers are operating the sites and controlling the information presented, including how transactions are processed and what is displayed to the victim on the site.
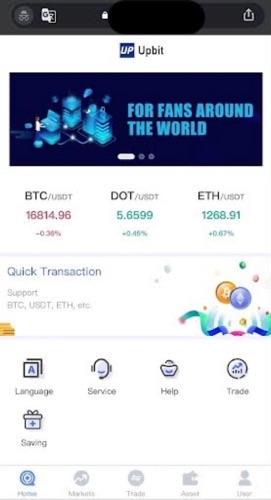
The pig butchers will ask victims/users to log in to these sites on their behalf. Upon logging in, victims will see a large sum of money in the fake account. In this instance, there was supposedly over $55,000 available for “trading” on this platform. I was asked to conduct trades on the pig butcher’s behalf as a way to help them because their “uncle” wasn’t available to assist.

This request to help with conducting trades is designed to help establish trust between the pig butchers and their victims. It also gives the potential victim a sampling of the fake returns promised by the pig butcher if they invested their own money into these attacker-controlled websites.
As a form of enticement, this involves showing fake trades and the resulting fake profits. For instance, I was asked to conduct trades of Litecoin ($LTC) on the fake Upbit cryptocurrency exchange:
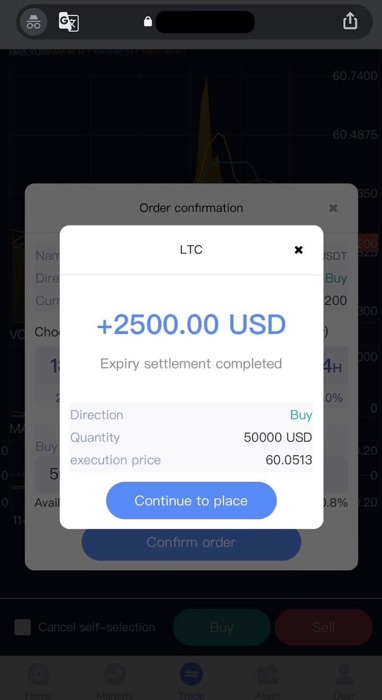
When I showed that I was adept at making these so-called trades, I was praised by the pig butcher. Eventually, they offered to give me an opportunity to invest my money into the fake Upbit exchange and asked me to register for an account.
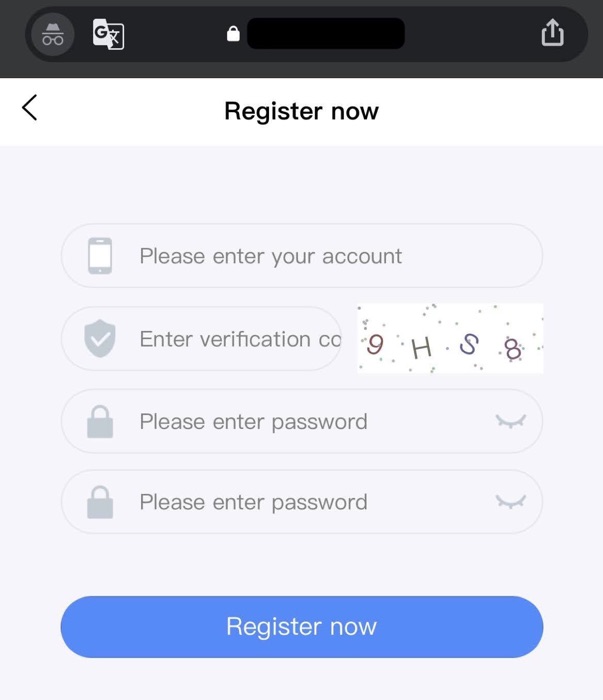
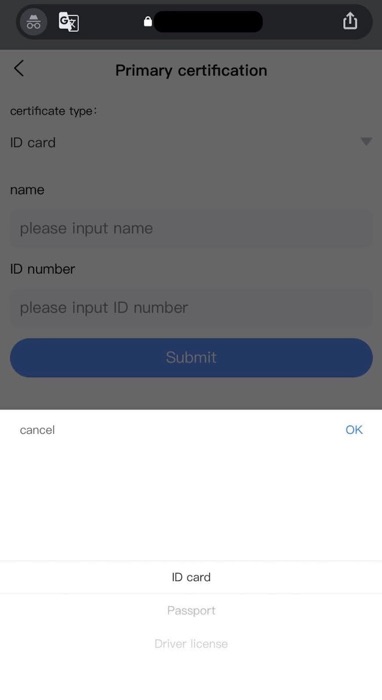
However, as part of the account registration process, they said I needed to provide sensitive information including identification in the form of a driver’s license, passport or an unspecified “ID card.” Unwilling to provide this type of identification, I ceased communication with the pig butcher at this point. If I had gone through with this request, I would have probably then been asked to wire funds to an account in order to fund my balance on this fake cryptocurrency exchange/investment site.
Fake cryptocurrency investment sites with Bitcoin and Ethereum addresses
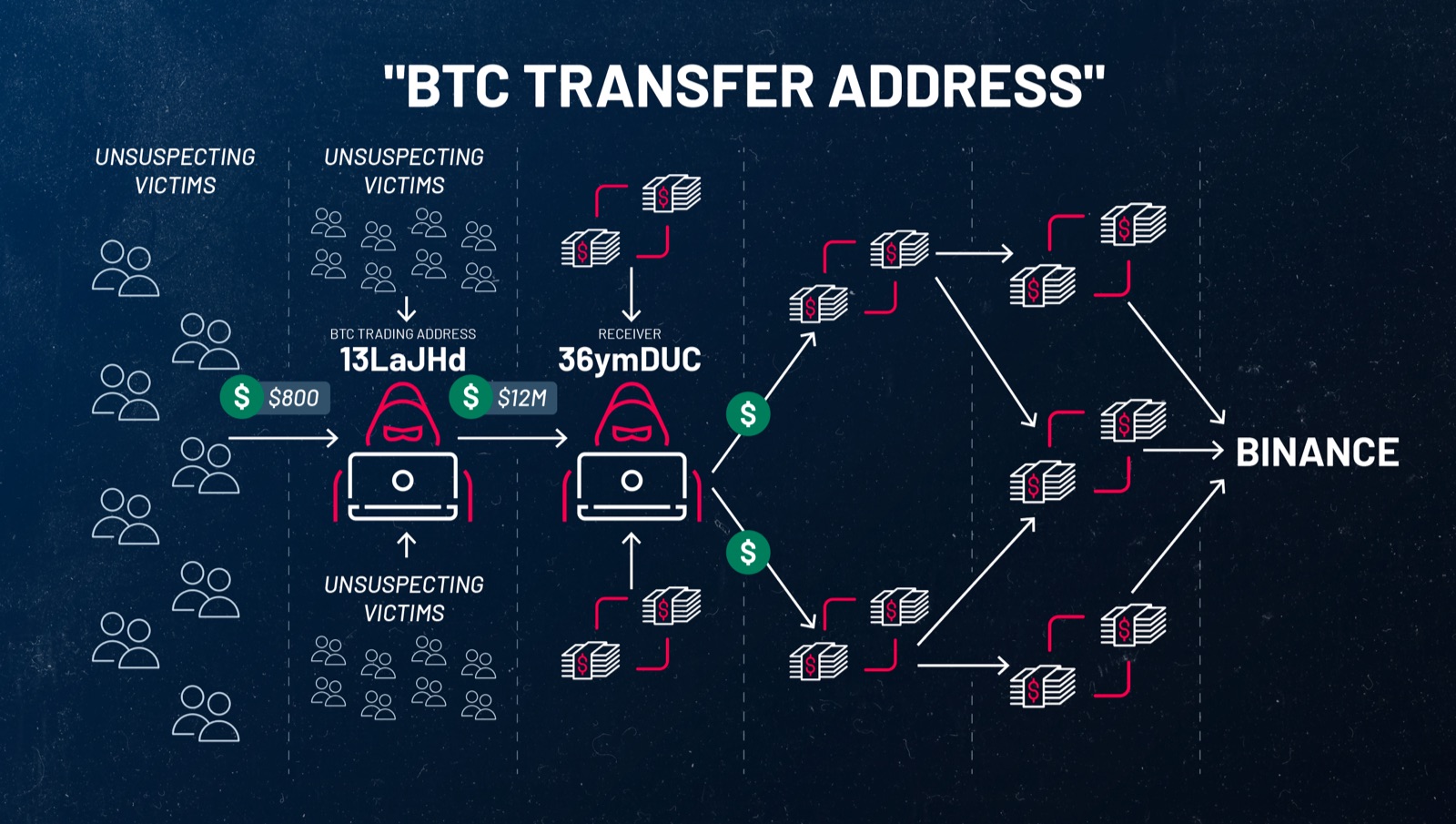
The second type of scam perpetrated by the pig butchers again involves leveraging fake investment sites, but with a twist: victims are instructed to send cryptocurrency directly to cryptocurrency addresses supposedly to fund their trading account. However, this was more of a ruse to directly transfer cryptocurrency to the pig butchers so that they could launder them out through a network of other cryptocurrency wallets. I encountered a few examples of this.
Example #1: Buying Ethereum from Coinbase to transfer to a pig butcher-controlled Ethereum wallet
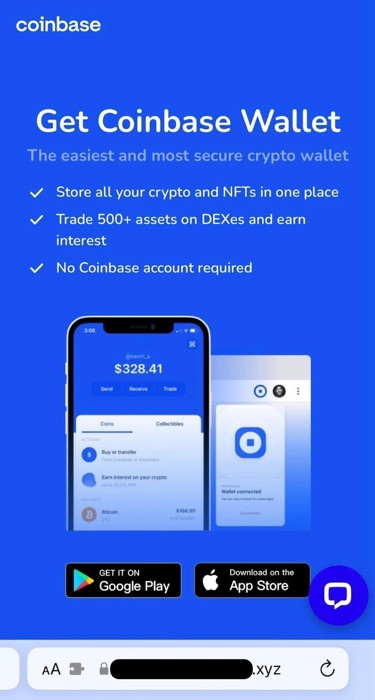
In one example, I was told to download the Coinbase Wallet and purchase Ethereum from Coinbase itself. However, the pig butchers said that transactions would be conducted with a different website, one hosted on the.xyz top level domain that claimed to be Kraken, a popular centralized cryptocurrency exchange (CEX).
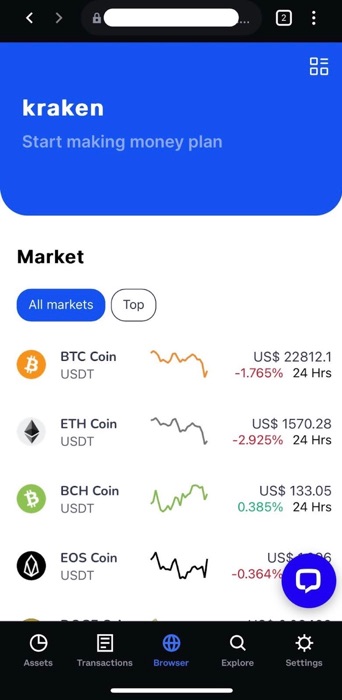
Once there, victims are instructed to visit a “customer support” page and ask for an “ETH link address.”
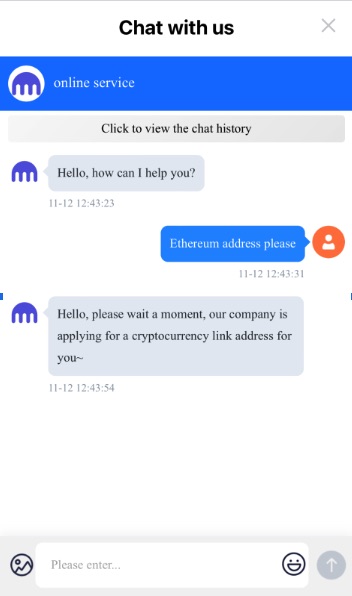
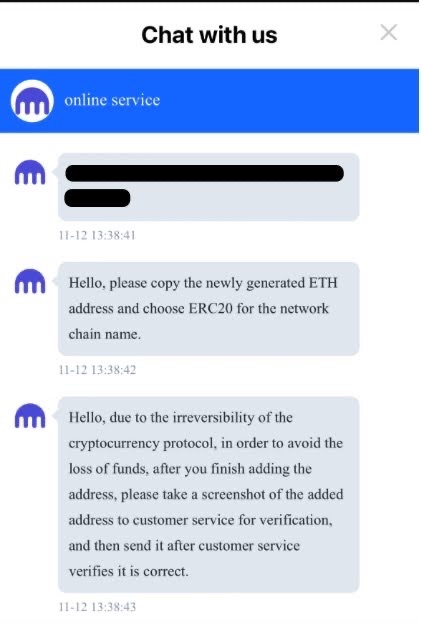
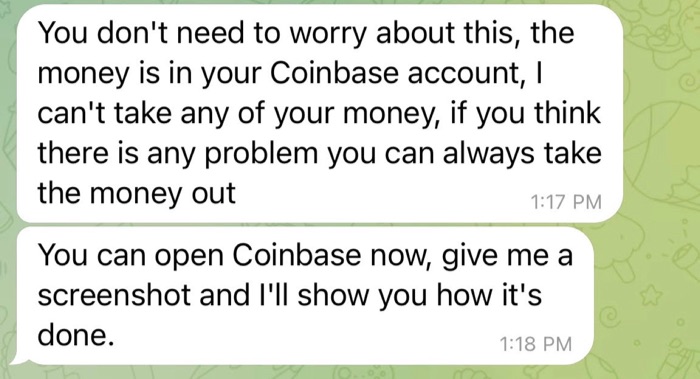
After a user visits this customer support page, they are given an Ethereum wallet address owned by the pig butchers. The “support” person asks for a screenshot of the address being “added” to the user’s cryptocurrency address book so they can verify that funds will be delivered to the right address.
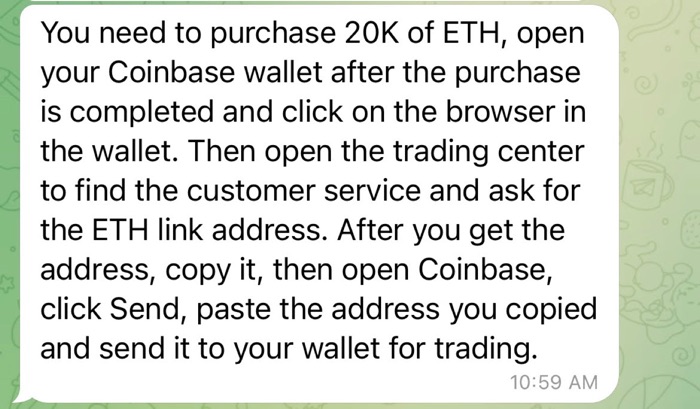
In this instance, I was asked to purchase $20,000 worth of Ethereum (or ETH) and send the ETH to the “address you copied and send it to your wallet for trading.” Such a high dollar amount of Ethereum is likely an effort to steal as many funds as possible.
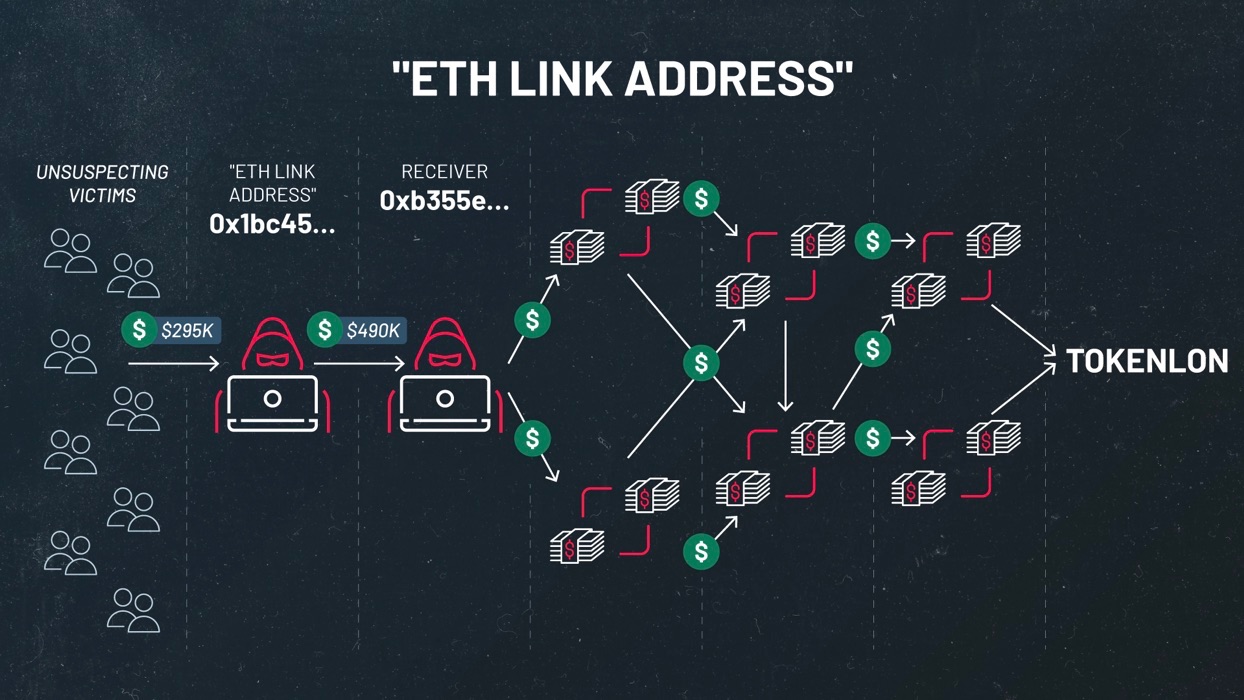
This particular address I was asked to send money to received nearly $500,000 in funds from other cryptocurrency wallets, which I am highly confident are other victims. These funds were then transferred to other cryptocurrency addresses and eventually laundered through a platform called Tokenlon, which appears to be a popular destination for stolen funds tied to pig butchering scams. However, because I cannot say with high confidence all of the funds associated with these other addresses originated from pig butchering victims, I am being conservative in my estimates of the losses.
Example #2: Purchase Bitcoin from Cash App, Transfer to Coinbase Wallet before transferring to pig butcher-controlled Bitcoin wallet
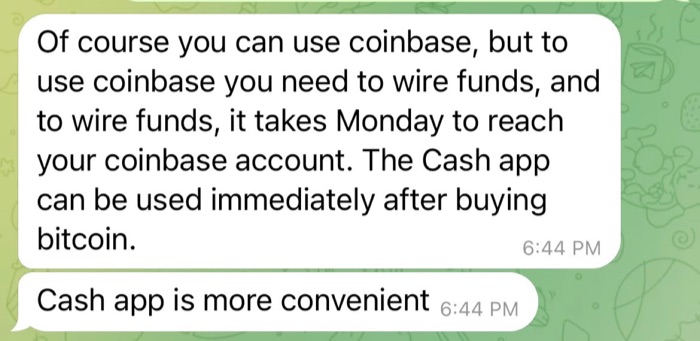
In another example, I was instructed to download Cash App, a popular peer-to-peer payment application that has been targeted by scammers in the past. However, in this scenario, I was told to purchase Bitcoin from Cash App and then download and transfer the funds to Coinbase Wallet.
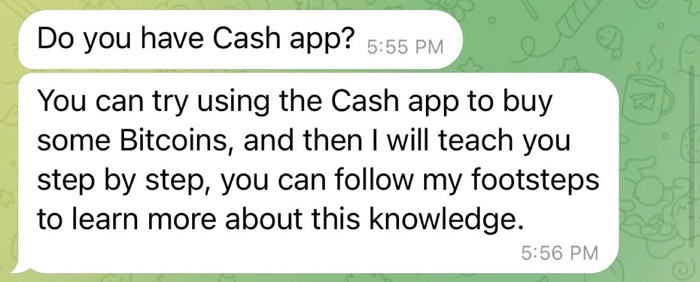
When I asked why I needed to purchase Bitcoin from Cash App rather than buying it straight from Coinbase, the butcher replied that Cash App is “more convenient” because it takes too long for the Bitcoin to reach my account when buying through Coinbase. With Cash App, the Bitcoin would be available for use “immediately.”
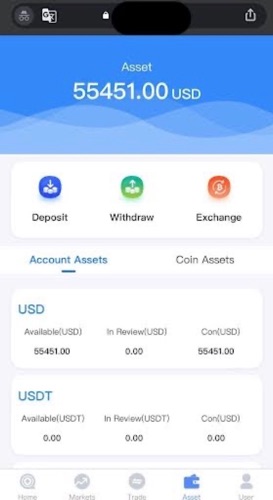
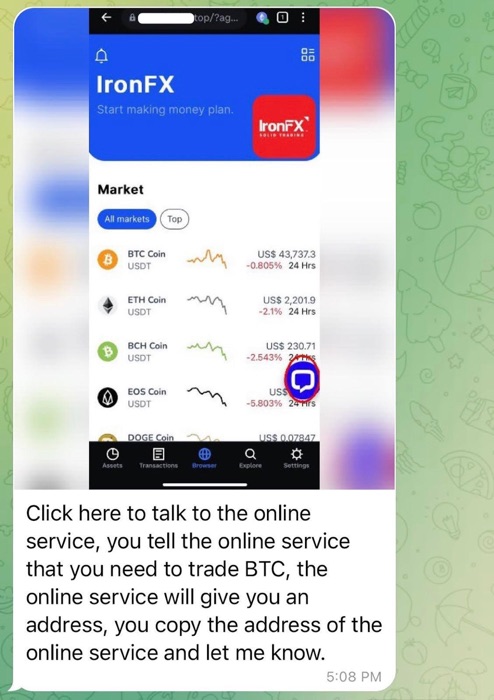
Similar to the previous example with Ethereum, I was instructed to visit a website claiming to be IronFX Online, an online trading platform. The layouts for both the fake IronFX Online website and the fake Kraken website are identical. Just as in the previous example, I was instructed to speak to the “online service” and tell them that I need to trade “BTC,” which is the ticker symbol for Bitcoin. According to the pig butchers, the “online service” will give me a cryptocurrency address that I will need to send the Bitcoin to.
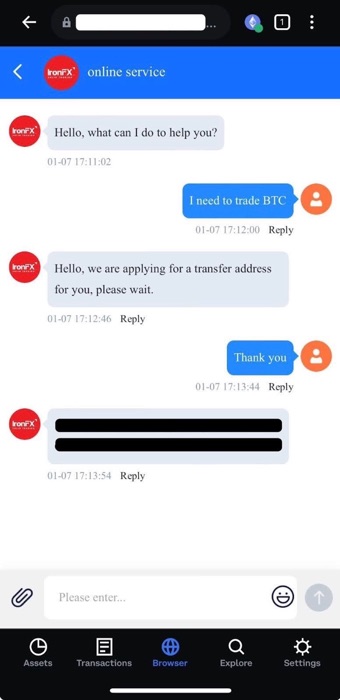
I was initially asked to invest as little as $1,000, but I asked if I could lower the amount and they agreed. I did not end up sending any funds to the address that was given to me, but I was able to see a small sum of money transferred to the address. This address sent those funds directly to another Bitcoin address that had received over 280 bitcoin, which totaled over $12.1 million dollars based on the price of Bitcoin as of February 2024.
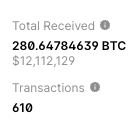
As with the Ethereum address that was given to me, I could see funds transferring through a web of cryptocurrency addresses that ultimately led to the cryptocurrency exchange Binance.
Combined, I conservatively estimate at least $13 million dollars in losses from the scams I encountered firsthand, but as noted before, these are likely underestimating the true cost of losses tied to pig butchering scams.
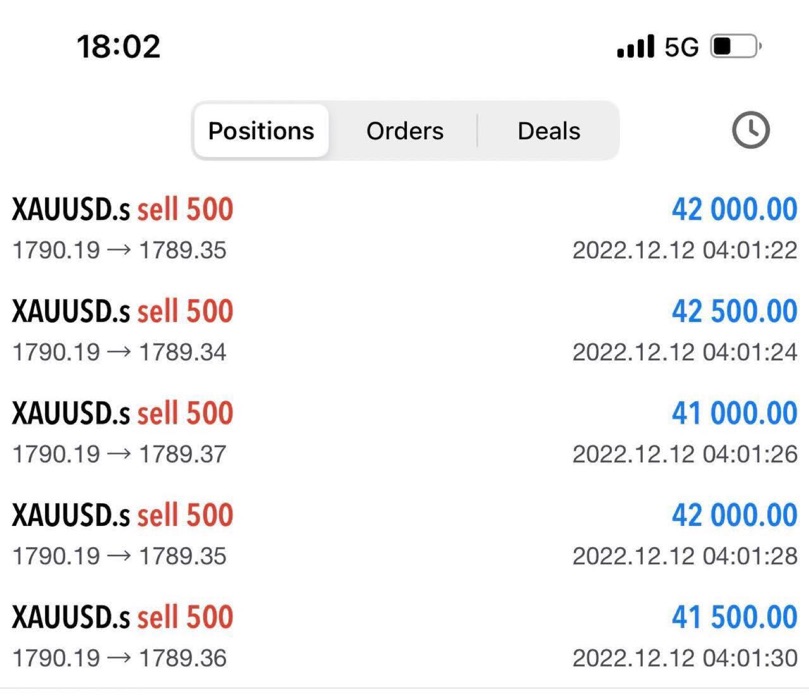
Spot gold trading through MetaTrader application
Another type of scam perpetrated by pig butcherers is the promotion of trading spot gold on a foreign exchange market. Spot gold translates to the current price of gold that can be traded at the present moment. It is often quoted in the U.S. dollar and denoted by the ticker symbol XAUUSD.
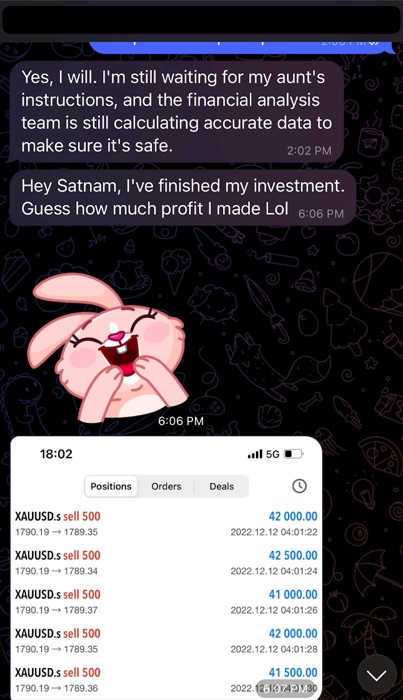
The pig butchers will try to entice their victims by talking up how much profit they’ve made. In the example above, this butcher sent a screenshot of a series of supposed successful trades of spot gold.
If the pig butcher can convince the victim to invest in spot gold, the victim will be instructed to visit a website that purports to be a trading platform. The example site I was told to visit was impersonating a website called Spreadex, a real platform used for sports betting that also allows for the trading of spot gold.

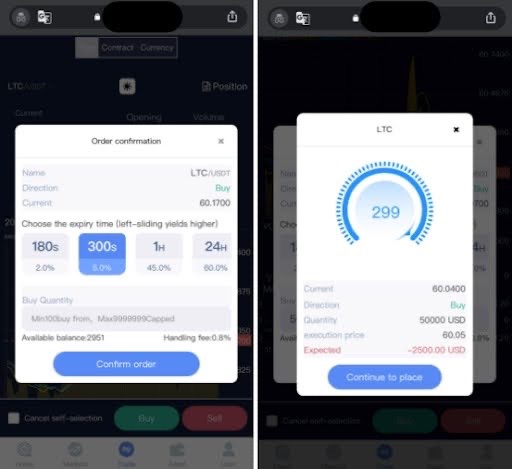
The website will ask users to download an application on their mobile device or personal computer. This page is designed to have the same look and feel as the Apple App Store to create false confidence in the victim that they are downloading an official application. In order to install the application, the website instructs iOS users to first install a profile/configuration onto their mobile device in order to download the MetaTrader 5 application.
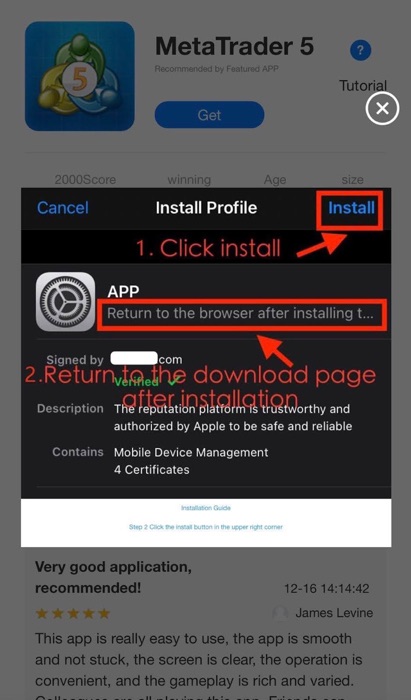
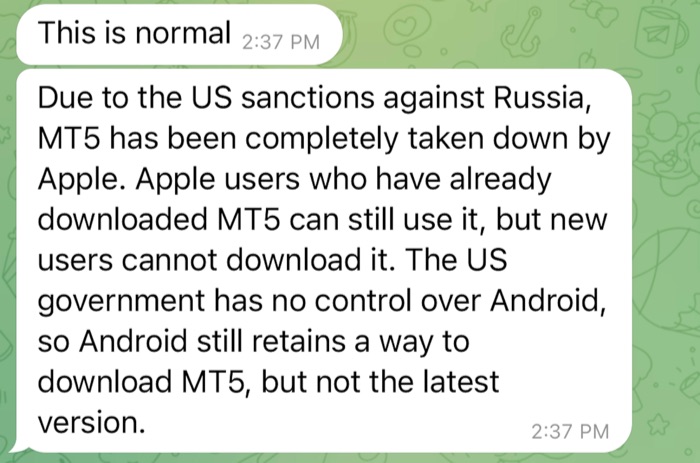
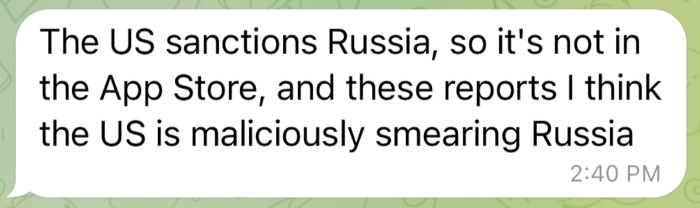
In September 2022, Apple removed the MetaTrader app from the App Store due to its link to crypto scams according to reporting by the Global Anti-Scam Organization (GASO).
When asked why MetaTrader 5 has been banned from the Apple App Store, the butcher had a canned response about it being removed due to “US sanctions against Russia” adding that the U.S. is “maliciously smearing Russia.”
Needless to say, I did not install the app on my device, but I imagine I would have suffered significant losses if I had installed it, like countless other victims.
The pig butchers ask me to buy cryptocurrency from Coinbase, Binance, Crypto.com, Kraken, Gemini, Uniswap, or peer-to-peer payment platforms including Cash App, PayPal and Venmo. Why don’t they want me to use their websites to purchase cryptocurrency?
The scammers operate fake cryptocurrency investment sites that can’t be used to purchase cryptocurrency. Therefore, they want their victims to purchase real cryptocurrency from popular exchanges and platforms and transfer them directly to cryptocurrency addresses the scammers own. They then manipulate the websites they control and operate so they can display fake charts and data to make it seem as though profits are being made, when in reality, the original cryptocurrency has been stolen and cannot be recovered.
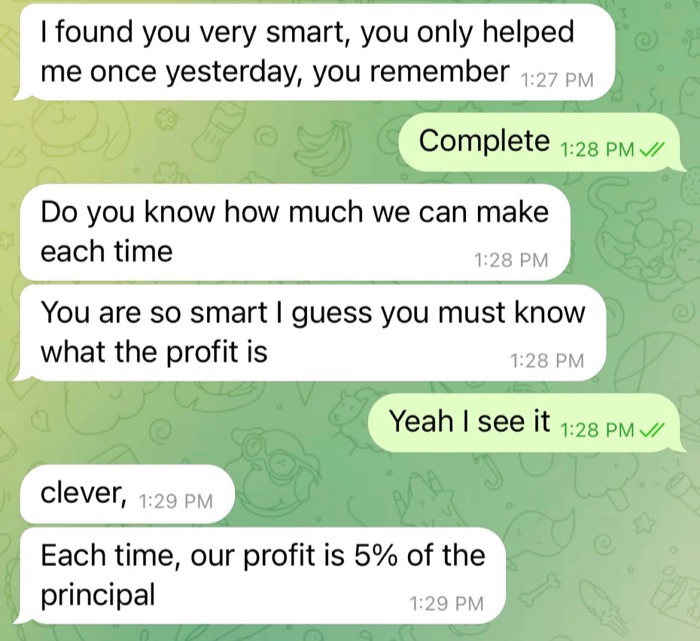
Do pig butchers expect me to know about these financial investments like cryptocurrency or spot gold?
No, they prefer that victims know nothing or very little about them. Victims are treated like novices, as pig butchers will walk users through a step-by-step process on how to buy and trade cryptocurrency or spot gold. If you do show some proficiency, jumping past steps, they will praise you on how smart you are.
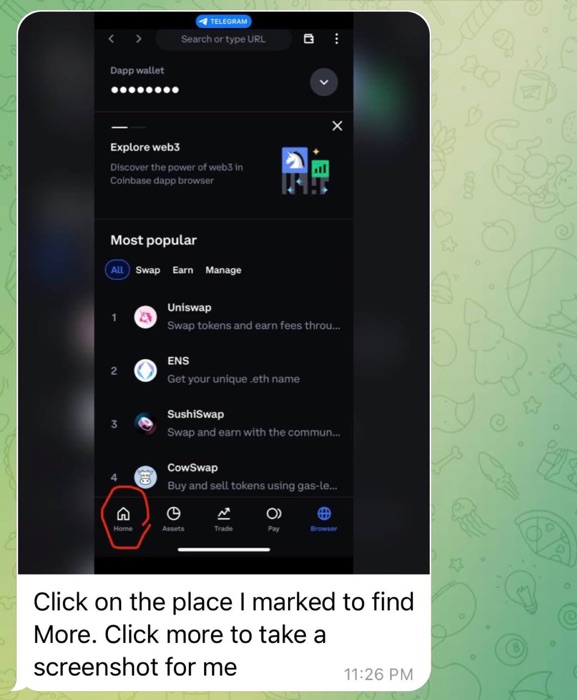
Why do the pig butchers ask me to send them screenshots from the apps?
Pig butchers ask for screenshots to ensure that victims are following their directions and will actually follow through on these fake investments.
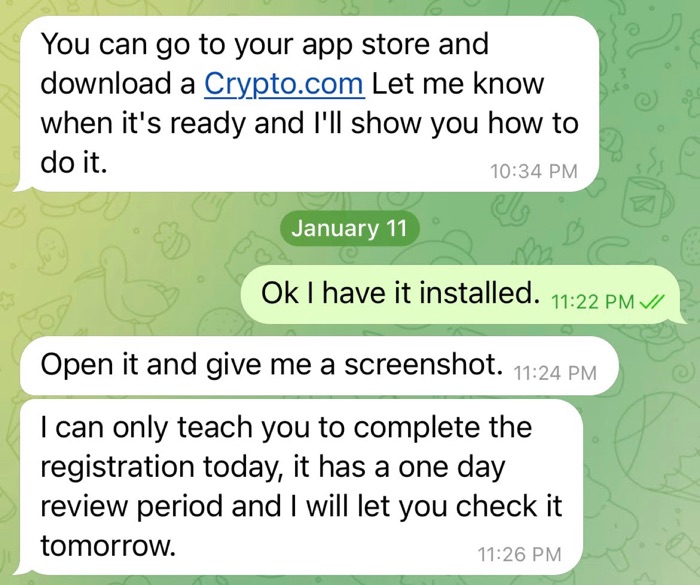
One common thread with pig butchers is that they circle parts of the screenshots sent to them to literally walk the victim through each step.
How can I spot pig butchering scams and what can I do to help stop them?
As of February 2024, these are some ways users can identify pig butchering scams:
- Random, unsolicited messages on WhatsApp, Telegram or SMS are attempts to bait you into responding. If you receive a random, unsolicited message on a messaging application like WhatsApp, Telegram, SMS or iMessage that gets your name wrong or sounds like a fishing expedition, it will ultimately lead to an attempt at pig butchering. If you are able to, report these messages and block the sender.
- Dating app users that quickly ask you to move off platform to WhatsApp, Telegram, SMS, iMessage or some other platform for messaging. A tried and true tactic of various scams is the use of urgency. In this case, pig butchers use urgency to direct users from dating apps to another messaging platform. This is a key indicator that the person on a dating app is operating more like a herder trying to direct you to the actual pig butcher off platform.
- Talking or bragging about investing in cryptocurrencies and other financial instruments. Bragging about or highlighting successful investments in cryptocurrencies and other financial instruments is a big red flag, especially if the pig butchers talk about a family member like a parent or aunt or uncle that helped them with their successful financial investments.
Asking you to purchase cryptocurrencies from legitimate exchanges and offering to show you how to make successful investments. You should stop immediately if you’re asked to purchase cryptocurrency at these places before transferring it elsewhere:
- popular exchanges like Coinbase, Binance, Crypto.com, Kraken and Gemini
- decentralized finance (DeFi) platforms like Uniswap
- peer-to-peer payment apps like CashApp, PayPal or Venmo.
You shouldn’t have to move off these exchanges to trade cryptocurrencies, so if you’re asked to transfer them somewhere else, you’re being scammed.
- Convincing you to download an application on your phone from outside of an app store in order to trade a certain type of financial instrument like spot gold. It’s a red flag if you are told to install an application on your device that requires you to install a special configuration or certificate on it. You shouldn’t have to install an app on your device outside of the app store. Installing this certificate or configuration could give the pig butchers control over your device. The app you install is designed to help fake the so-called profits in trading financial instruments like spot gold.
Conclusion
In this blog post, I detailed various ways pig butchering scammers try to convince their victims to participate in fraudulent investments including through fake cryptocurrency investment sites and by installing risky apps onto their devices in order to trade spot gold.
Knowledge is power, which is why dating applications, social media platforms and messaging services should do more to warn users about the potential risks associated with pig butchering scams on their various platforms. Coffee Meets Bagel, another popular dating app, has displayed pop-up warnings to users about pig butchering scams and has written a blog post with more information about them. This effort is important and they have likely saved some users from becoming victims to these scams.
If you have been a victim of pig butchering, please file a complaint with your local law enforcement or government agency. For instance, in the U.S., contact the Internet Crime Complaint Center (IC3); in the U.K., contact the National Cyber Security Centre (NCSC); and in Australia, contact the Australian Signals Directorate’s Australian Cyber Security Centre (ASD ASC).
This is part two of a series investigating pig butchering scams. For a primer on what pig butchering is and how pig butchering scams start, please refer to our first blog post: Pig Butchering Scam: From Tinder and TikTok to WhatsApp and Telegram, How Scammers Are Stealing Millions in a Long Con
Pour en savoir plus
- Exposure Management
- Reports
- Research Reports


