Applications built today are more complex and have more internal architecture than applications built 10 years ago. Commonly coupled with applications is additional software such as self-updating mechanisms to keep the main application up to date. The secondary updater application can keep the main application up to date on anti-virus definitions, application files that help render a page, or even completely update the main application to a new version. Decoupling the updating mechanism from the main application allows developers to hone the abilities within the main application. Loosely connected features in one application can introduce more problems than developers try to solve and make maintenance of the application more unwieldy.
Analysts need to know where software resides in an organization, regardless of the function. Almost every piece of software has or will have vulnerabilities require identification and attention. Examples of software identified in this report include Oracle Java Auto Updater, Adobe Update Manager, and Symantec Live Update. These applications are essential to making sure the respective applications they support are kept up to date. While the updater software may be perceived as an application with low risk to the organization, this type of software can instrument and change software that organizations rely upon. The updater software can be vulnerable with common software risks, such as the SQL injections shown in this advisory by Symantec for their LiveUpdate Administrator software.
The Common Platform Enumeration (CPE) filter is used to identify the software programs referenced in this report. According to NIST, the CPE is a structured naming scheme for information technology systems, software, and packages. Based upon the generic syntax for Uniform Resource Identifiers (URI), CPE includes a formal name format, a method for checking names against a system, and a description format for binding text and tests to a name. Tenable assigns CPEs to plugins where appropriate. This allows analysts to search for common CPE strings such as cpe:/a:adobe:adobe_update, cpe:/a:oracle:java_auto_updater, and cpe:/a:symantec:live. These particular CPE strings used in this report can be found in the CPE database by searching for the product names for the corresponding CPE string. Associating CPE strings with vulnerabilities allow the analysts a greater view into separating operating system vulnerabilities from application vulnerabilities, and adds to the level of vulnerability detail provided to the organization.
Within this report, analysts are provided information on where software updater software exists in the organization. Depending on the policies of the organization, a vendor’s client-side software updater may not be allowed. This report shows what hosts have this type of software from vendors such as Adobe, Apple, HP, Symantec, and Oracle to keep systems compliant with organizational policies. If organizations do choose to allow and use a vendor’s solution for application updates, analysts can see vulnerabilities associated with the software over time and by severity. Analysts expect to fix Adobe and Microsoft software on a monthly basis, but may not consider that the software updating software may also need attention. Organizations can be aware of vulnerabilities with this software and identify where in the organization these applications reside with Tenable Nessus.
This report is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the SecurityCenter Feed under the category Threat Detection & Vulnerability Assessments. The report requirements are:
- SecurityCenter 5.4
- Nessus 6.8.1
Tenable SecurityCenter provides continuous network monitoring, vulnerability identification, and security monitoring. SecurityCenter is continuously updated with information about advanced threats and zero-day vulnerabilities, and new types of regulatory compliance configuration audit files. Tenable constantly analyzes information from our unique sensors, delivering continuous visibility and critical context, enabling decisive action that transforms your security program from reactive to proactive. Active scanning examines the updater software applications on the systems, running processes and services, detection of vulnerable software applications, configuration settings, and additional vulnerabilities. With this information, analysts have greater insight to determine if supported and up-to-date updater software applications are operating within the organization. Tenable enables powerful, yet non-disruptive, continuous monitoring of the organization to ensure vulnerabilities are available to analysts.
This report contains the following chapters:
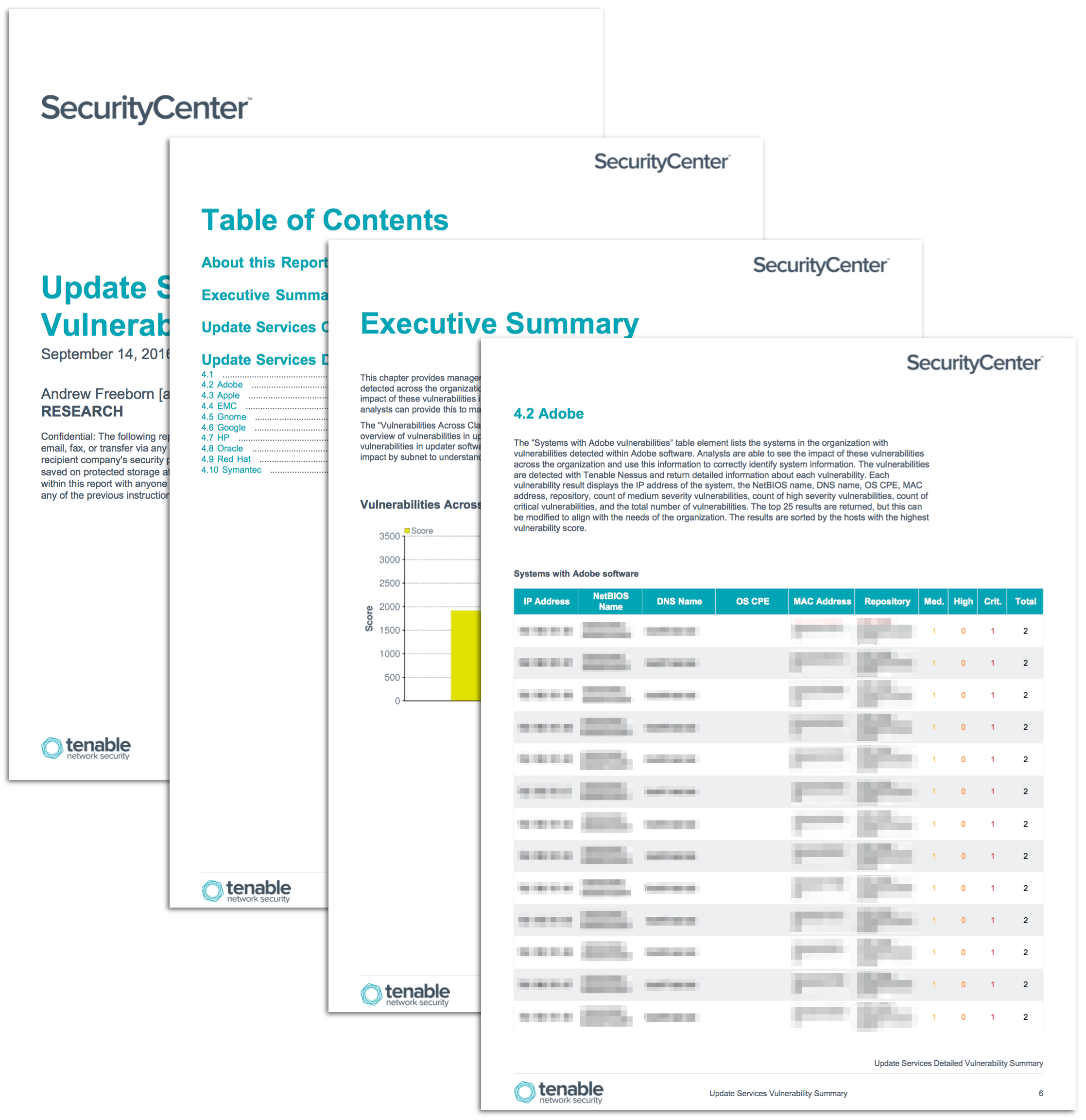
- Executive Summary: This chapter provides management and analysts an overview of vulnerabilities within updater software detected across the organization
- Update Services Critical Vulnerability Information: This chapter lists the detected critical vulnerabilities in updater software found within the organization
- Update Services Detailed Vulnerability Summary: This chapter breaks out vulnerabilities in updater software with an in-depth look at the vulnerabilities by vendor
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success