by Ryan Seguin
A series of Microsoft Exchange server zero-day exploits were discovered in December of 2020 by a Taiwanese organization called DEVCORE. The flaw, a server-side request forgery vulnerability, gives and attacker the ability to bypass authentication and gain elevated privileges. This vulnerability resulted in the issuance of CVE-2021-26855. An attack chain can be created by combining this vulnerability with an insecure deserialization vulnerability within the Exchange Unified Messaging Service (CVE-2021-26857), and multiple post authentication vulnerabilities (CVE-2021-26858 and CVE-2021-27065). A successful attack can lead to remote code execution, backdoors, and data theft, resulting in further potential compromise.
On March 2, 2021 Microsoft released critical security updates for four zero-day Microsoft Exchange server vulnerabilities. At that time, Microsoft also reported that these vulnerabilities were actively being exploited by threat actors. Within a single week upwards of 60,000 organizations world-wide may have fallen victim to the exploit. Attacks are expanding rapidly and are no longer being conducted by a few groups, nor are they isolated to a few countries.
This focus of this report is to provide organizations with tools to identify MS Exchange Server vulnerabilities and potential indicators of compromise (IOC) of the ProxyLogon/Hafnium exploits. Organizations benefit from having vulnerability information that not only determines if patches are missing from normal credentialed scanning, but also from uncredentialed scanning. This report displays vulnerability findings for authentication bypass vulnerabilities to determine if the organizations Microsoft Exchange servers are vulnerable to this attack via direct check plugins. Direct check plugins are unique as they are designed to determine if the system is vulnerable to the exploit. This plugin can be used in uncredentialed scanning to determine if the Exchange Server is vulnerable to the exploit itself.
The report also provides information on potential compromise. Plugins detect the potential presence of a web shell in selected directories on the Microsoft Exchange server. The presence of this shell can be indicative that the host may have been targeted in the Hafnium campaign, or by other threat actors. Organizations should verify findings and take appropriate remediation actions for these hosts. In addition to checking for this IOC, organizations are strongly encouraged to apply available patches by Microsoft as soon as possible.
More information on this exploit and the plugins that have been released can be found on the following Tenable Blog Posts:
- Finding Proxylogon and Related Microsoft Exchange Vulnerabilities: How Tenable Can Help
- CVE-2021-26855, CVE-2021-26857, CVE-2021-26858, CVE-2021-27065: Four Zero-Day Vulnerabilities in Microsoft Exchange Server Exploited in the Wild.
- Microsoft Exchange Server ProxyLogon/Hafnium Detection Dashboard
This report contains:
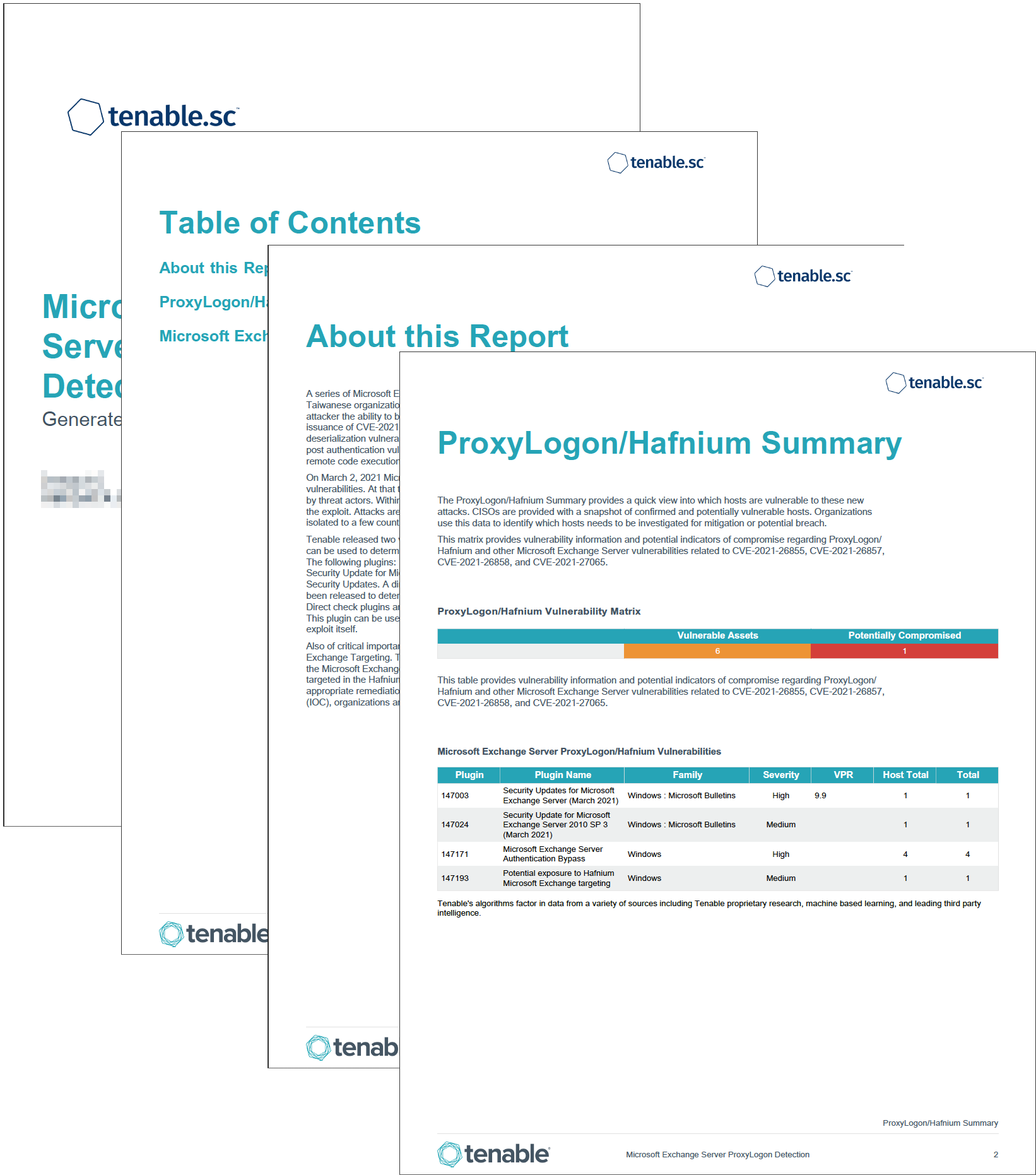
ProxyLogon/Hafnium Summary: The ProxyLogon/Hafnium Summary provides a quick view into which hosts are vulnerable to these new attacks. Administrators are provided with a snapshot of confirmed and potentially vulnerable hosts. Organizations use this data to identify which hosts needs to be investigated for mitigation or potential breach.
Microsoft Exchange Detection and other Vulnerabilities: This Section displays a which hosts have Microsoft Exchange Server installed, and which Exchange servers are missing Microsoft security updates. Organizations are also provided with a trend graph that illustrates Exchange security update detection over time. IT Teams use this data to identify which Exchange Servers require additional security updates and attention in order to minimize extra time spent mitigating risk on those assets.
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess an organization's adherence to best practice configuration baselines. Tenable.sc provides customers with a complete Cyber Exposure platform for completing effective cybersecurity practices
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success