by Cody Dumont
The Cybersecurity Maturity Model Certification (CMMC) was developed to create a framework to assess an organization's implementation of cybersecurity practices evenly across the defense industrial base. Using NIST 800-53 and NIST 800-171 as the baseline, the primary objective of CMMC is to consolidate the two security catalogs into a single measurable framework. Over the next 5 years, starting in June 2020, organizations that create Government off-the-shelf (GOTS) products, handle Federal Contract Information (FCI), or Controlled Unclassified Information (CUI) will need to show compliance at 1 of the 5 levels. Only Cyber 3rd Party Accreditation Organizations (C3PAO) will be able to certify an organization as compliant or not. Tenable.sc provides on-prem solutions for assessing Cyber Exposure practices and maps these practices to known assessment regulations such as NIST, CSF, and others. This report provides the executive leadership teams with high level understanding of the current state of the network.
The first step in achieving any level of compliance with CMMC begins with an understanding of the current environment. The CISO must be able to understand the current state of patch management, systems hardening, and different methods of system classification. This report focuses on a few key domains in CMMC, they are: Risk Management (RM), Security Assessment (CA), Media Protection (MP), and Configuration Management (CM). Each of these domains are starting points into other domains, for example the CM domain is a requirement before assessments into Identification & Authentication (IA) & System & Information Integrity (SI). The CM domain is the basis for hardening standards that are outlined by Defense Information Systems Agency (DISA) Security Technical Implementation Guides (STIGs) or the Center for Internet Security (CIS) Benchmarks. Both sets of hardening guidelines are auditable using the Tenable Audit files, and provide the foundation for good system configuration and hardening. Once these standards are widely deployed in the network, the risk managers can begin to evaluate other CMMC domains such as the aforementioned IS or SI. For example, the IA domain requires "Enforce a minimum password complexity and change of characters when new passwords are created." While CM requires organizations to "establish and enforce security configuration settings for information technology products employed in organizational systems." These two controls work together and provide the CISO with tools needed to measure and discuss the current status of risk with other contributors.
This report starts by providing the overall status of vulnerability and compliance data collected using Tenable.sc. This trending data is collected using nightly snapshots of cumulative data stored in Tenable.sc. Over time the CISO can begin to understand the historic performance of the IT Operations team in risk mitigation tasks. There are also comparative matrices that provide counts and percentages of vulnerabilities that have been mitigated along with the risks that remain outstanding.
The CISO and risk manager work together to identify and create migration strategies. A key aspect to mitigating risk is to understand the current likelihood of a vulnerability being exploited by adversaries. Tenable created the Vulnerability Priority Rating (VPR) to help add current threat intelligence to the risk analysis process. At the heart of VPR is a series of machine learning models working together to forecast threats. Specifically, the threat forecast seeks to answer the question: What is the appropriate level of near-term threat for a vulnerability based on the latest available data? This report brings VPR into the conversation by tracking the top 25 most critical hosts based on VPR scores.
The CISO and IT managers also work together to establish the hardening standards that are appropriate for the organization. These configuration settings will most likely be different for each organization, and Tenable provides audit files for a majority of the CIS Benchmarks and DISA STIGs. In both cases Tenable.sc uses a field called Cross Reference to connect the NIST 800-53, to NIST 800-171, to other standards such as the Cybersecurity Framework. The CMMC cross links all these widely accepted standards together and provides organizations with a well-established baseline to begin reducing risk. The CMMC maturity levels are achieved the more mature the security practices become. This report helps to pull this configuration data together in a summarized view to aid in the improvement of security practices.
The report is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The report can be easily located in the Tenable.sc Feed under the category Executive. The report requirements are:
- Tenable.sc 5.14.1
- Nessus 8.10.1
- Tenable Audit Files
Tenable.sc Continuous View (CV) is the market-defining On-Prem Cyber Exposure Platform. Tenable.sc CV provides the ability to continuously Assess the implementation of cybersecurity practices and institutionalization of cybersecurity processes. Regardless of the maturity model the organization is measuring against, Tenable.sc provides the essential information to report accurate and reliable metrics.
Chapters
Executive Summary: The Executive Summary chapter provides the leadership team with a high-level understanding of the current and past status of data collected related to CMMC. The Vulnerability & Compliance Trending (25 Day) chart provides 5 lines for each of the data statuses overall that show progress and implementation of cyber security practices. There are two primary data types, the compliance data and vulnerability data. The compliance data is displayed using the passed, failed, and manual check lines. The passed line shows checks that have passed the audit check, and failed is the checks that are not within the parameters of the audit check. The executives should be able to see a trend over time by moving numbers into the passed vs failed line. Manual checks are configurations that require a user to evaluate and determine the proper status. The vulnerability data is displayed with new vulnerabilities or the re-surfaced vulnerabilities. The re-surfaced vulnerabilities are issues that at some point in time were believed to be fixed, but have returned. If this number is very high, then the vulnerability scanning program is not being utilized effectively and needs to be re-evaluated.
Risk Management: This chapter uses several matrices to track the mitigation progress. Tenable.sc records when vulnerabilities are discovered, when patches are issued, and when vulnerabilities are mitigated. A vulnerability is moved to the mitigated database when the vulnerability is no longer detected by a rescan; the vulnerability is assumed to be remediated. Unmitigated vulnerabilities are the current vulnerabilities that are not yet remediated and are stored in the cumulative database. Using the Exploitable and Patch Available attributes, the risk managers can better understand the current effectiveness of risk mitigation efforts.
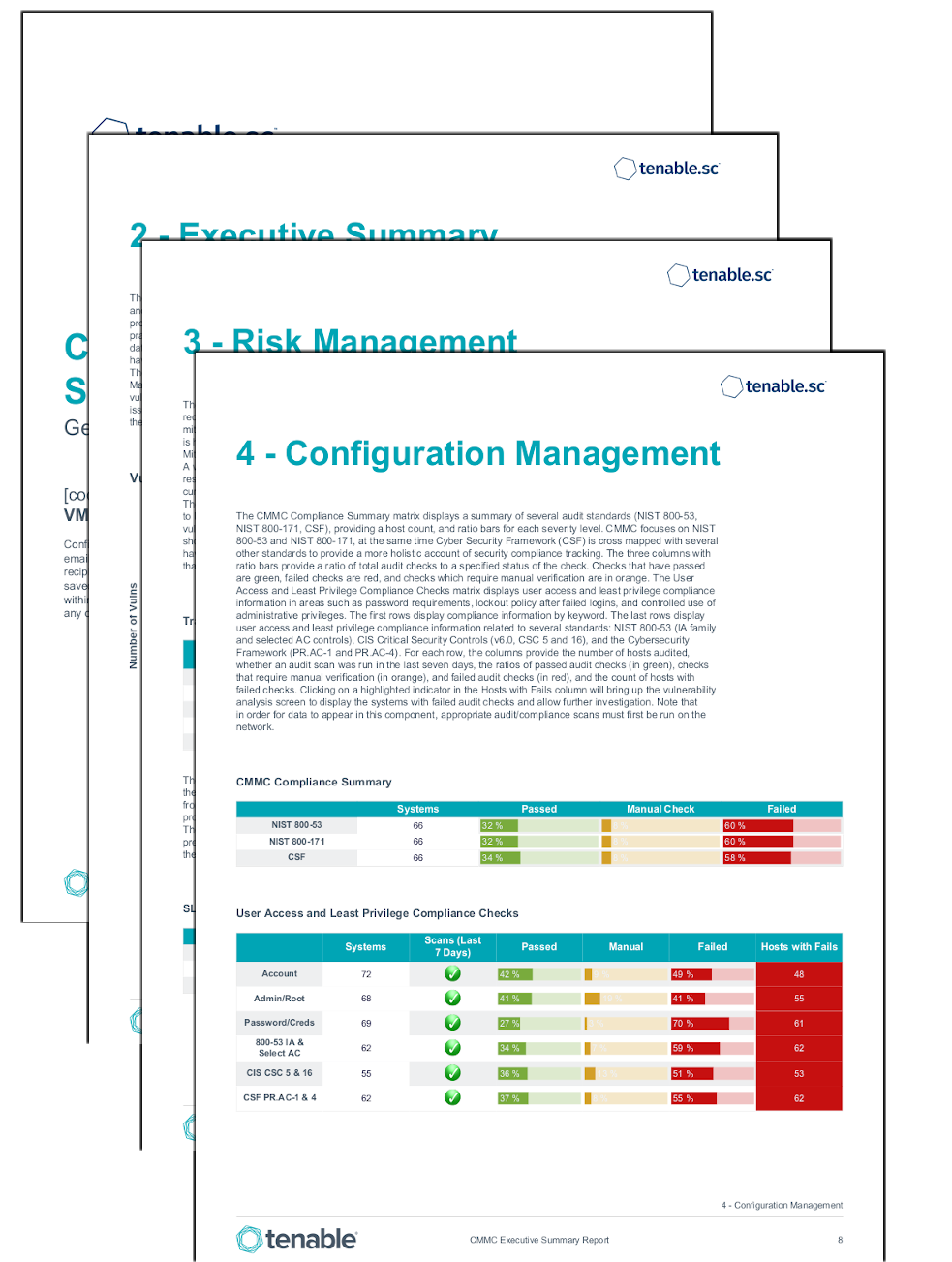
Configuration Management: This chapter provides summary information about Anti-Virus deployments, system hardening, and device type detections. The Anti-Virus (AV) Status matrix displays the percentage of total systems that have AV installed and working properly. The CMMC Compliance Summary matrix displays a summary of several audit standards (NIST 800-53, NIST 800-171, CSF), providing a host count, and ratio bars for each severity level. The two Breakdown of Devices Detected on Network matrices use the device type plugin and breaks out all the detectable device types. The Removable Compliance Summary provides insight into CMMC requirements to monitor how removable media access is controlled.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success