Responding to KRACK: What You Need To Know
A new weakness in WPA2 protocol could allow an attacker to read information that was previously assumed to be encrypted, provided the attacker is within the range of the victim.
The weakness was discovered by researchers Mathy Vanhoef and Frank Piessens, from the University of Leuven and has been dubbed KRACK (Key Reinstallation Attack).
Which devices are affected by KRACK?
The KRACK weakness works against all modern, protected Wi-Fi networks. Therefore, if a device supports Wi-Fi, it is most likely affected.
What’s the impact?
The weakness could allow an attacker to decrypt network traffic allowing him/her to steal sensitive information such as credit card numbers, passwords, emails etc. In certain configurations, it could also allow an attacker to inject or forge packets, which could be leveraged to potentially inject malware.
How does it work?
The KRACK weakness affects the Wi-Fi standard itself. This means, the attack works against personal and enterprise Wi-Fi networks as well as older WPA and the latest WPA2 standard, even if the networks only use AES algorithm for encryption.
The vulnerability works by attacking the 4-way handshake of the WPA2 protocol and, in the process, tricking a victim into re-installing a key that’s already in use. Ideally, it should not be possible to reuse a key, but since the WPA2 protocol does not guarantee key reuse, attackers can exploit this weakness by manipulating cryptographic handshakes.
In a typical 4-way handshake, a client will install the key after receiving message 3 of the 4-way handshake. This key is subsequently used to encrypt normal data frames using an encryption protocol. But since messages often get lost/dropped, an access point could resend message 3 multiple times to the client if appropriate acknowledgment was not received. In which case, the client will reinstall the key, and reset the nonces.
If an attacker can reset these nonces at will (which is possible due to this weakness) by collecting and replaying retransmissions of message 3 of the 4-way handshake, the encryption protocol can be attacked resulting in decryption of packets.
Tenable coverage of KRACK
Tenable has released several Nessus® plugins to detect systems affected by the KRACK weakness. The following table summarizes Tenable's coverage.
| Vendor | Plugin ID | Description |
|---|---|---|
|
Microsoft |
Windows 10 Version 1703 October 2017 Cumulative Update (KRACK) |
|
|
Microsoft |
Windows 7 and Windows Server 2008 R2 October 2017 Cumulative Update (KRACK) |
|
|
Microsoft |
Windows 10 Version 1511 October 2017 Cumulative Update (KRACK) |
|
|
Microsoft |
Windows Server 2012 October 2017 Cumulative Update (KRACK) |
|
|
Microsoft |
Windows 10 Version 1607 and Windows Server 2016 October 2017 Cumulative Update (KRACK) |
|
|
Microsoft |
Windows 8.1 and Windows Server 2012 R2 October 2017 Cumulative Update (KRACK) |
|
|
Microsoft |
Windows 2008 October 2017 Multiple Security Updates (KRACK) |
|
|
Cisco |
Cisco ASA FirePOWER Services Multiple Vulnerabilities in Wi-Fi Protected Access and Wi-Fi Protected Access II (KRACK) |
|
|
Aruba |
ArubaOS WPA2 Key Reinstallation Vulnerabilities (KRACK) |
|
|
Mikrotik |
MikroTik RouterOS < 6.39.3 / 6.40.4 / 6.41rc (KRACK) |
|
|
FreeBSD |
FreeBSD : WPA packet number reuse with replayed messages and key reinstallation (d670a953-b2a1-11e7-a633-009c02a2ab30) (KRACK) |
|
|
Ubuntu |
Ubuntu 14.04 LTS / 16.04 LTS / 17.04 : wpa vulnerabilities (USN-3455-1) (KRACK) |
|
|
Debian |
Debian DSA-3999-1 : wpa - security update (KRACK) |
|
|
Intel |
Intel Wireless Driver Wi-Fi Protected Access II (WPA2) Multiple Vulnerabilities (KRACK) |
|
|
Fortinet |
FortiGate < 5.2 / 5.2.x <= 5.2.11 / 5.4.x <= 5.4.5 / 5.6.x <= 5.6.2 Multiple Vulnerabilities (FG-IR-17-196) (KRACK) |
|
|
Ubiquiti Networks |
Ubiquiti Networks UniFi < 3.9.3.7537 (KRACK) |
|
|
CentOS |
CentOS 7 : wpa_supplicant (CESA-2017:2907) (KRACK) |
|
|
Fedora |
Fedora 25 : 1:wpa_supplicant (2017-12e76e8364) (KRACK) |
|
|
Fedora |
Fedora 26 : 1:wpa_supplicant (2017-60bfb576b7) (KRACK) |
|
|
Oracle |
Oracle Linux 7 : wpa_supplicant (ELSA-2017-2907) (KRACK) |
|
|
Redhat |
RHEL 7 : wpa_supplicant (RHSA-2017:2907) (KRACK) |
|
|
SUSE |
SUSE SLES11 Security Update : wpa_supplicant (SUSE-SU-2017:2752-1) (KRACK) |
Protecting your organization from KRACK
As patches become available, you should consider which systems expose the network to the greatest risk (those that use Wi-Fi), define a series of checks and then test patches before rolling them to all systems in the network.
Tenable products can assist in identifying systems in the network that may require patching and ensure that systems for which patches are available are properly updated.Tenable will continue to provide coverage for products as patches are rolled out by vendors.
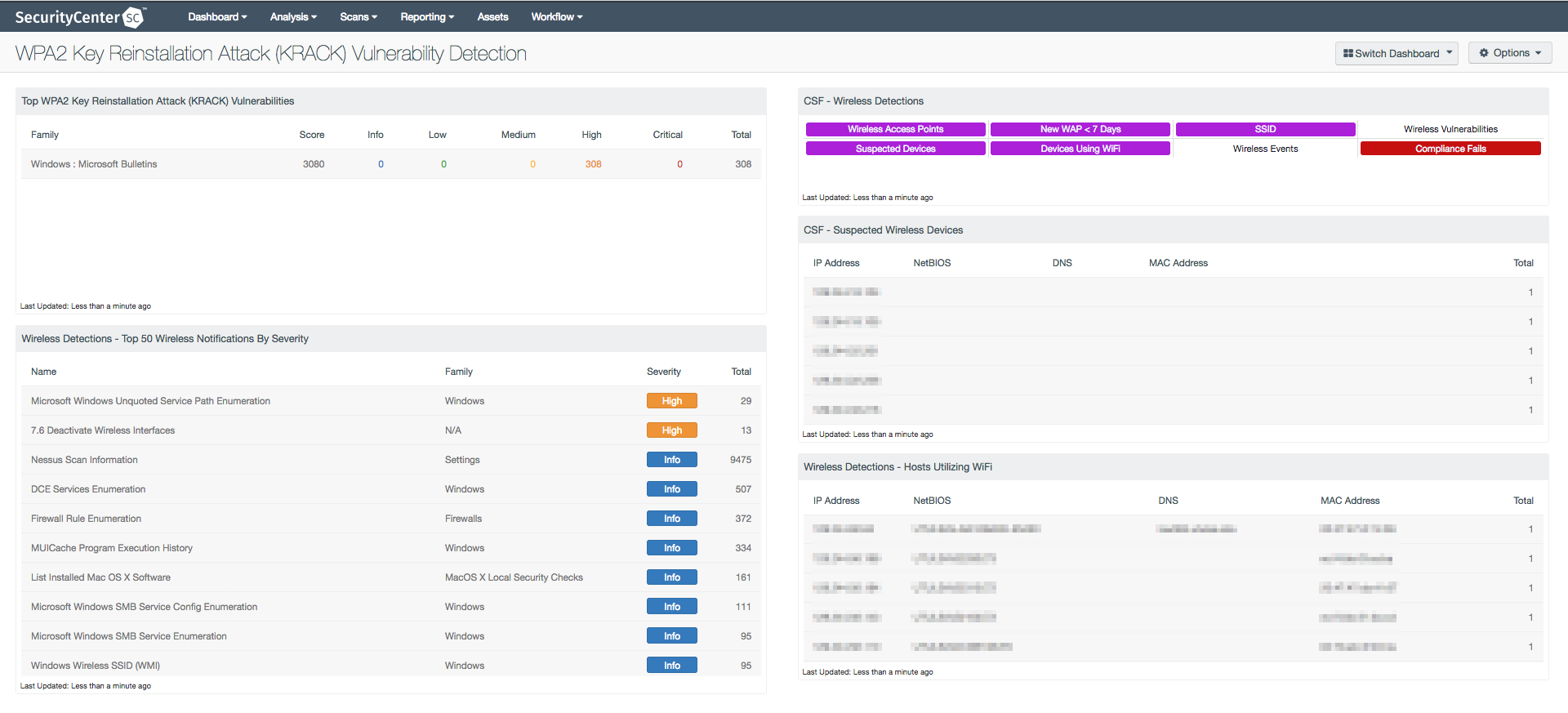
KRACK Dashboard
SecurityCenter® has a new dashboard, WPA2 Key Reinstallation Attack (KRACK) Vulnerability Detection, that focuses specifically on this new weakness. This dashboard provides an analysis of the Wi-Fi infrastructure and the systems that need to be secured against the KRACK vulnerability.
Stay tuned for more updates
Tenable is keeping a close eye on this story as it develops. Our team will release coverage as additional patches from vendors become available and this post will be updated as new plugins are released.
Learn more
- Plugins
- Vulnerability Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success