Mr. Robot Season 2 Unmasked

In the season 2 premiere of Mr. Robot, our protagonist, Elliot, struggles with an internal battle involving the memory of his father and the ramifications of the last hack in season 1. In this episode we see several challenges that all information security professionals face on a daily basis, from the hacking tools our adversaries use to the internal struggle we often experience assessing technology-based risks at our organizations.
Tracking actions on the network
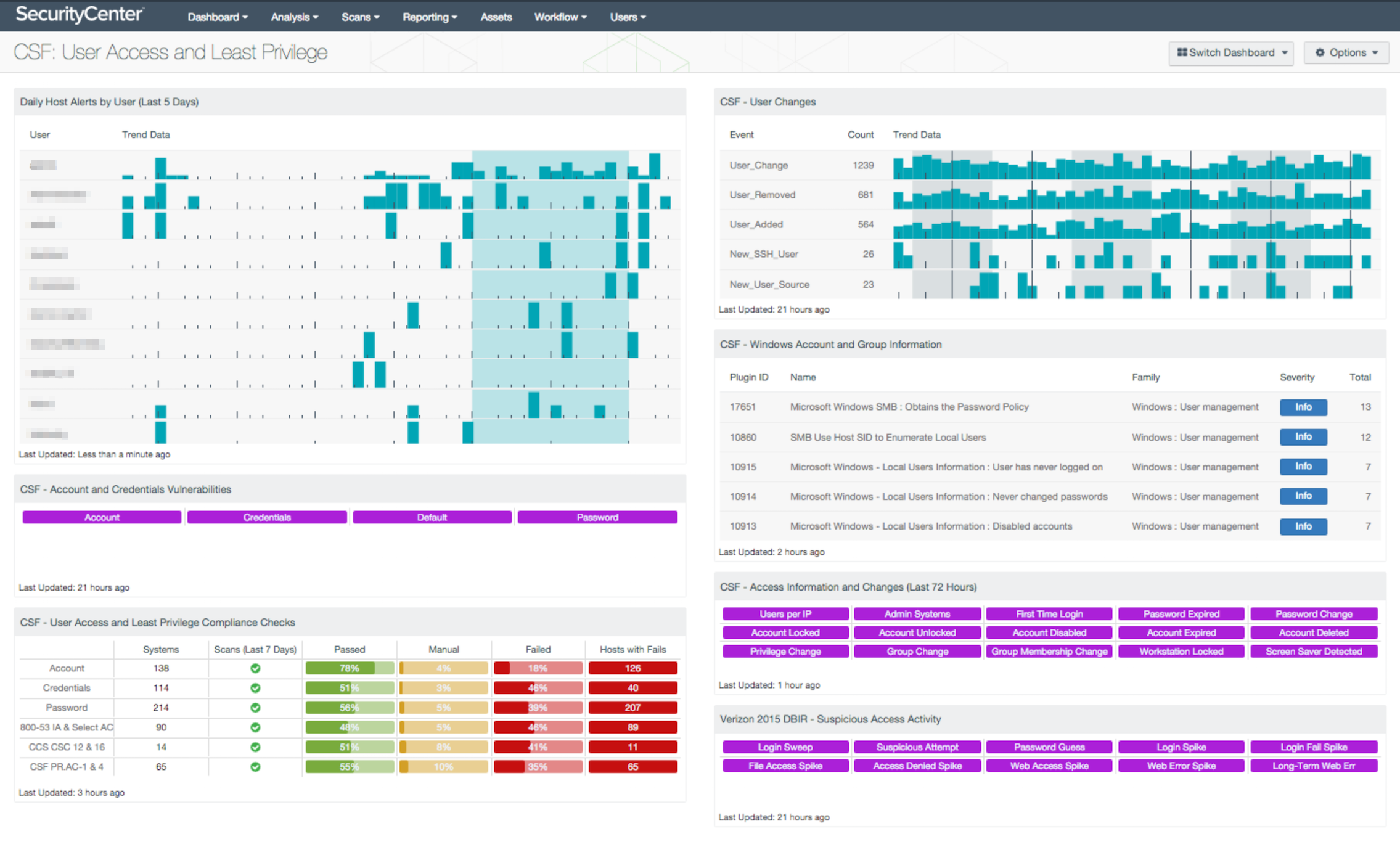
In one of the early scenes, Gideon talks to Elliot about how the FBI thinks Gideon is behind the hack or is somehow complicit. He then talks about giving over all evidence. Gideon believes the FBI is hacking his email; he knows someone is looking at his email. SecurityCenter Continuous View™ (SecurityCenter CV™) provides a full solution for monitoring events such as password changes, login and logoff events, and many of the concerns Gideon is worried about. The strength in the SecurityCenter CV system is the combination of data from several sources using Nessus® to actively scan and interrogate systems for vulnerabilities and configuration issues, passively monitoring the same systems looking for vulnerabilities and behaviors that are malicious in nature, and collecting logs from network devices and host operating systems. To further support the security team in identifying risk, SecurityCenter CV has a feed of reports, assurance report cards (ARC), and dashboards to monitor such changes. For example:
- ISO/IEC27000: User Access Management
- CSF PROTECT.Access Control (PR.AC)
- CSF: User Access and Least Privilege
The exploit and post-exploitation
Later in the episode, Darlene uses the Social Engineer Toolkit (SET), written by Dave Kennedy at TrustedSec, to run her third party module which created an executable file called “cryptowall.exe” on a USB thumb drive. She gives this drive to Mobley, her right hand man, to plug into a workstation at E-Corp. Cryptowalls are a relatively new family of malware that acts as a form of ransomware, the most famous being CryptoLocker. The malware encrypts files on the operating system and requires payment to decrypt them.
Ransomware is quickly becoming the most prevalent malware grabbing headlines. While not typically used by penetration testers, the malware infection method used in this episode is a real and serious threat to our security. Training users on the authorized use of systems, and monitoring the use of privileged users is paramount to an organization's security. A USB drive and an unhappy employee can often circumvent the best security solutions.
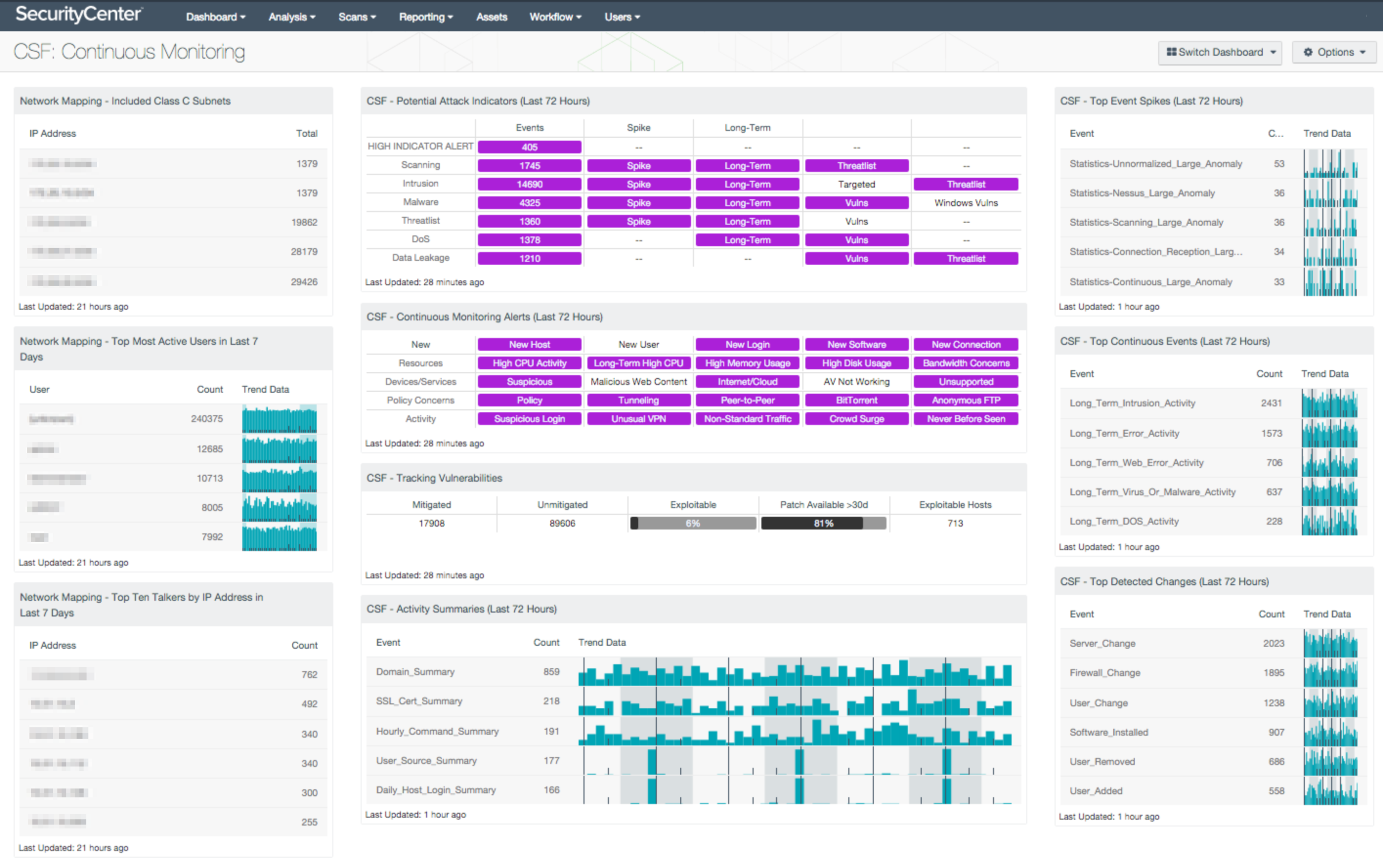
However, tracking USB insertions is not the only issue plaguing E-Corp. They are also not properly securing the edge of the network, by using proxy servers and egress filters. If you follow the commands used by Darlene in the SET program, she is setting the call home server to 192.251.68.254. This IP is actually a public accessible IP address that is owned by NBC, but seems to be a C2 address with some interesting base64 encoded text. The SET tool is also pointing to port 80, which is used for HTTP. While HTTP is a difficult port to filter or block, by using a proxy server, the egress points in the network can be set up in such a manner to block port 80 from all systems except the proxy server. Had this been configured, and then using Tenable NetFlow Monitor and Tenable Network Monitor collectors, evidence of the call home might have been blocked or, at the very least, tracked more efficiently. SecurityCenter CV has the ability to identify traffic flows using port and IP combinations. With the advanced correlation abilities found in Log Correlation Engine™ (LCE®), anomalies and first time events can easily be identified. Here are a few SecurityCenter CV dashboards that are helpful when analyzing traffic patterns:
The regime
This first episode focuses on Elliot’s regime-maintaining control of his mind by maintaining control of information. This is an illusion many organizations have with respect to their security posture, as they may do the same thing day after day. They only scan the safe IPs and never truly scrutinize the network. By practicing continuous monitoring, and looking in the far reaches of your network, you can begin to see the true environment and assess the true risk. Tenable SecurityCenter CV offers five sensors - active scanning, intelligent connectors, agent scanning, passive listening, and host data - to deliver comprehensive intelligence that protects your organization. SecurityCenter CV can help security professionals expand their daily regime to include continuous visibility and context that facilitates decisive action.
Thanks to Matt Hand for his contributions to this article.
Learn more
- LCE
- Malware
- Nessus Network Monitor
- SecurityCenter
- Vulnerability Management

Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success