by Cesar Navas
Organizations that must comply with Canadian regulatory controls need a consistent and structured way to meet compliance requirements. The Communications Security Establishment Canada (CSEC) developed a series of guidelines for security practitioners in managing information technology (IT) security risks for Government of Canada (GC) information systems. The ITSG-33, IT Security Risk Management: A Lifecycle Approach provides a comprehensive set of security controls that will be used to support a wide variety of business requirements. To support interoperability needs, the ITSG-33 guide is consistent with controls published in the U.S. National Institute of Standards and Technology (NIST) Special Publication 800-53. The standard does not explicitly state how to validate these settings in a cohesive and straightforward interface. Analysts within an organization must ensure that the compliance standard is followed, but also ensure the organization is continually compliant. This report covers all the ITSG-33 families currently supported by Tenable audit files, which provide the results of an audit check as one of three severity levels. Analysts are able to see on a continual basis the status of the organization and the posture of being compliant with ITSG-33 controls.
The ITSG-33 families and controls are not a checklist-type compliance standard like HIPAA, PCI, or CSF; rather, they are a catalog of controls that are used in achieving compliance with the aforementioned standards. Analysts are presented with the status of the checks such as an informational severity level which is considered a pass. The pass is achieved when the configuration setting matches the expected result of the audit check. The match can be a defined value or a range of values. The “Nessus Compliance Checks” document, available in the Support Portal, contains details on how to edit the audit files. When an audit check fails, the severity is set to high, indicating that the collected result and the expected result do not match. A mismatch may not mean a failure. Each failure should be reviewed and verified to ensure the expected result is correct. If the expected result is not correct, then the audit file should be modified and the scan should be run again. Results assigned a medium severity must be evaluated by an analyst to determine whether the results are applicable or not.
Tenable provides several solutions for organizations to better understand vulnerability management. Security leaders need to SEE everything, PREDICT what matters most and ACT to address cyber risk and effectively align cybersecurity initiatives with business objectives. Tenable Vulnerability Management (formerly Tenable.io) discovers and analyzes assets continuously to provide an accurate and unified view of an organization's security posture. The requirements for this report are: Tenable Vulnerability Management.
Chapters:
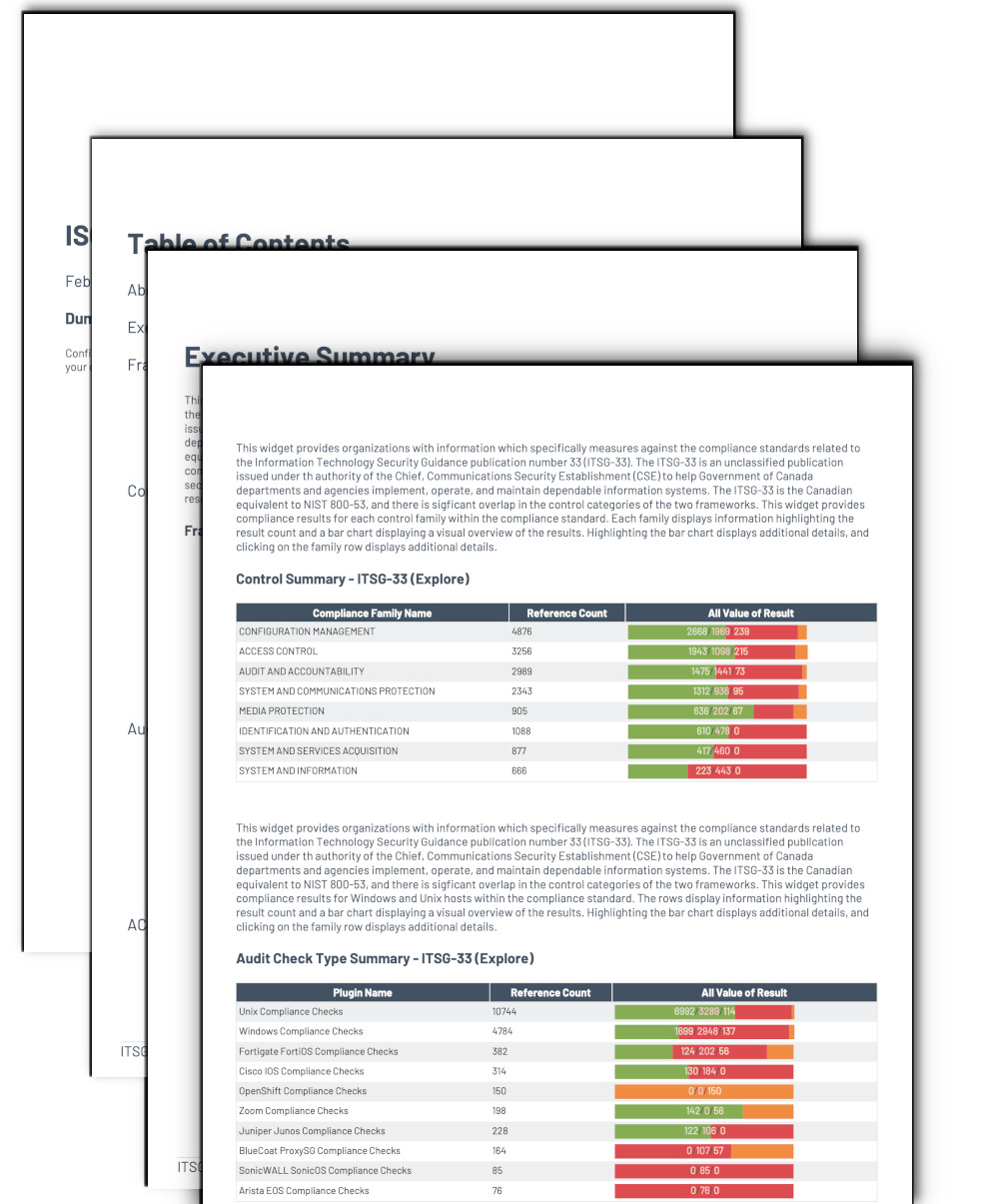
- Executive Summary: This chapter contains three elements which provide a high level overview summarizing results outlined in ITSG-33.
- Framework Result Summary: This chapter summarizes all the families outlined in ITSG-33.
- Control Summary: This chapter summarizes all the families outlined in ITSG-33.
- Audit Check Type Summary: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- ACCESS CONTROL: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- AUDIT AND ACCOUNTABILITY: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- AWARENESS AND TRAINING: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- CONFIGURATION MANAGEMENT: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- CONTINGENCY PLANNING (CONTINUITY PLANNING): This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- IDENTIFICATION AND AUTHENTICATION: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- INCIDENT RESPONSE: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- MAINTENANCE: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- MEDIA PROTECTION: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- RISK ASSESSMENT: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- SECURITY ASSESSMENT AND AUTHORIZATION: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- SYSTEM AND COMMUNICATIONS PROTECTION: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- SYSTEM AND INFORMATION: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
- SYSTEM AND SERVICES ACQUISITION: This chapter provides details on each of the compliance controls for the compliance family group being referenced.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success