Microsoft’s July 2021 Patch Tuesday Includes 116 CVEs (CVE-2021-31979, CVE-2021-33771)
Microsoft highlights 116 CVEs including two which were addressed by April patches.
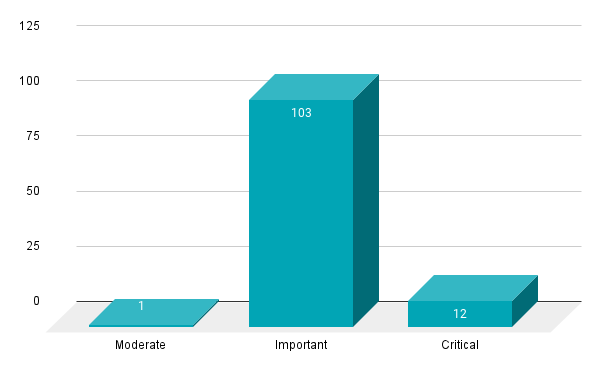
- 12Critical
- 103Important
- 1Moderate
- 0Low
Microsoft patched 116 CVEs in the July 2021 Patch Tuesday release, including 12 CVEs rated as critical, 103 rated as important and one rated as moderate. It’s only the second time in 2021 that Microsoft has included more than 100 vulnerabilities in Patch Tuesday, while it passed that milestone eight times in 2020.
This month's Patch Tuesday release includes fixes for:
- Common Internet File System
- Dynamics Business Central Control
- Microsoft Bing
- Microsoft Dynamics
- Microsoft Exchange Server
- Microsoft Graphics Component
- Microsoft Office
- Microsoft Office Excel
- Microsoft Office SharePoint
- Microsoft Scripting Engine
- Microsoft Windows Codecs Library
- Microsoft Windows DNS
- Microsoft Windows Media Foundation
- OpenEnclave
- Power BI
- Role: DNS Server
- Role: Hyper-V
- Visual Studio Code
- Visual Studio Code - .NET Runtime
- Visual Studio Code - Maven for Java Extension
- Windows Active Directory
- Windows Address Book
- Windows AF_UNIX Socket Provider
- Windows AppContainer
- Windows AppX Deployment Extensions
- Windows Authenticode
- Windows Cloud Files Mini Filter Driver
- Windows Console Driver
- Windows Defender
- Windows Desktop Bridge
- Windows Event Tracing
- Windows File History Service
- Windows Hello
- Windows HTML Platform
- Windows Installer
- Windows Kernel
- Windows Key Distribution Center
- Windows Local Security Authority Subsystem Service
- Windows MSHTML Platform
- Windows Partition Management Driver
- Windows PFX Encryption
- Windows Print Spooler Components
- Windows Projected File System, Windows Remote Access Connection Manager
- Windows Remote Assistance
- Windows Secure Kernel Mode
- Windows Security Account Manager
- Windows Shell
- Windows SMB
- Windows Storage Spaces Controller
- Windows TCP/IP
- Windows Win32K
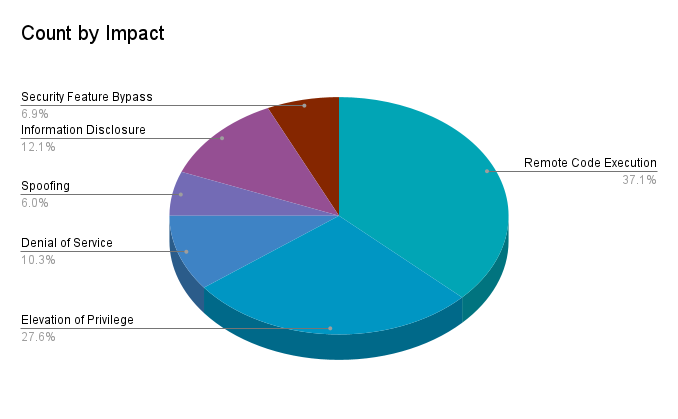
Remote code execution (RCE) vulnerabilities accounted for 37.1% of the vulnerabilities patched this month, followed by Elevation of Privilege (EoP) at 27.6%.
CVE-2021-31979 and CVE-2021-33771 | Windows Kernel Elevation of Privilege Vulnerability
CVE-2021-31979 and CVE-2021-33771 are EoP vulnerabilities in the Windows kernel. Both vulnerabilities received a CVSSv3 score of 7.8 and have been exploited in the wild as zero-days, according to Microsoft’s Threat Intelligence Center and Security Response Center. A local, authenticated attacker could exploit these vulnerabilities to run processes with elevated permissions. Similar zero-day vulnerabilities were patched in April 2020, which were observed under active exploitation by Google Project Zero.
CVE-2021-31196, CVE-2021-31206 and CVE-2021-34473 | Microsoft Exchange Server Remote Code Execution Vulnerability
CVE-2021-31196, CVE-2021-31206 and CVE-2021-34473 are RCE vulnerabilities in Microsoft Exchange Server. CVE-2021-34473 is the highest rated, receiving a CVSSv3 score of 9.1 and is more likely to be exploited according to Microsoft’s Exploitability Index. It was also patched as part of the April 2021 Patch Tuesday release, though Microsoft says the CVE was “inadvertently omitted” from the security update guide despite being patched. Exchange Server has become a very popular target since March, when Microsoft patched four zero-day vulnerabilities, including CVE-2021-26855 (ProxyLogon) in an out-of-band release. In fact, CVE-2021-31196 was disclosed to Microsoft by Orange Tsai of the DEVCORE team, who was also responsible for disclosing ProxyLogon and other Exchange Server vulnerabilities earlier this year. For organizations that run Exchange Server on-prem, it is important to apply available patches sooner rather than later, especially with the increased targeting of vulnerable servers.
CVE-2021-33768, CVE-2021-34470 and CVE-2021-34523 | Microsoft Exchange Server Elevation of Privilege Vulnerability
CVE-2021-33768, CVE-2021-34470 and CVE-2021-34523 are EoP vulnerabilities in Microsoft Exchange Server. CVE-2021-34523 is the highest rated Exchange Server EoP, receiving a CVSSv3 score of 9.0, though it is less likely to be exploited according to Microsoft’s Exploitability Index, as an attacker would need to have already established a presence on the vulnerable Exchange Server first before they could elevate privileges. Just like CVE-2021-34473, CVE-2021-34523 was patched as part of the April 2021 Patch Tuesday release and is another vulnerability that Microsoft says was omitted from its release notes inadvertently. CVE-2021-33768 was also disclosed to Microsoft by Orange Tsai. For organizations that run Exchange Server on-prem, it is important to apply available patches sooner rather than later, especially with the increased targeting of vulnerable servers.
CVE-2021-33746, CVE-2021-33754, CVE-2021-33780, CVE-2021-34494 and CVE-2021-34525 | Windows DNS Server Remote Code Execution Vulnerability
CVE-2021-33746, CVE-2021-33754, CVE-2021-33780, CVE-2021-34494 and CVE-2021-34525 are RCE vulnerabilities found in Windows DNS Server. While CVE-2021-33746 and CVE-2021-33754 were given CVSSv3 scores of 8.0, the remainder were scored as 8.8 because user interaction is not required. Based on the scores provided, exploitation of these flaws would require a low privileged account, presumably with the ability to send crafted DNS requests across the network, to target an affected DNS Server. Microsoft specifically calls out in the advisories for CVE-2021-33780 and CVE-2021-34494 that a host is only affected if it is configured as a DNS server, though the remaining CVEs do not provide this clarity. Even without the clarification on these CVEs, we recommend applying the necessary cumulative patches to all applicable hosts.
CVE-2021-34450 | Windows Hyper-V Remote Code Execution Vulnerability
CVE-2021-34450 is an RCE vulnerability in Windows Hyper-V, which would allow an attacker who is authenticated to a guest virtual machine (VM) to send crafted requests to execute arbitrary code on the host machine. While Microsoft rates this as “Exploitation Less Likely,” it is important to consider that malware variants commonly look to escape VMs and infect the host machine, so patching this flaw should remain a priority despite Microsoft’s risk assessment.
CVE-2021-34464 and CVE-2021-34522 | Microsoft Defender Remote Code Execution Vulnerability
CVE-2021-34464 and CVE-2021-34522 are RCE vulnerabilities in the Microsoft Malware Protection Engine. Both of these vulnerabilities received CVSSv3 scores of 7.8 and are rated as “Exploitation Less Likely,” but we chose to highlight them due to in-the-wild exploitation of a similar flaw, CVE-2021-1647, in January. While CVE-2021-1647 was a zero-day, the ubiquity of Microsoft Defender makes this a noteworthy vulnerability. Fortunately, Microsoft Defender automatically updates in most configurations, limiting the impact of this vulnerability. Microsoft does recommend, and provide guidance for, confirming that automatic updates are working.
CVE-2021-34448 | Scripting Engine Memory Corruption Vulnerability
CVE-2021-34448 is a memory corruption vulnerability in the Microsoft Scripting Engine which has been exploited in the wild as a zero-day, according to Microsoft. An attacker would need to entice a victim into visiting a malicious website in order to successfully exploit this vulnerability. Because exploitation requires user interaction, this vulnerability only received a CVSSv3 score of 6.8.
Tenable solutions
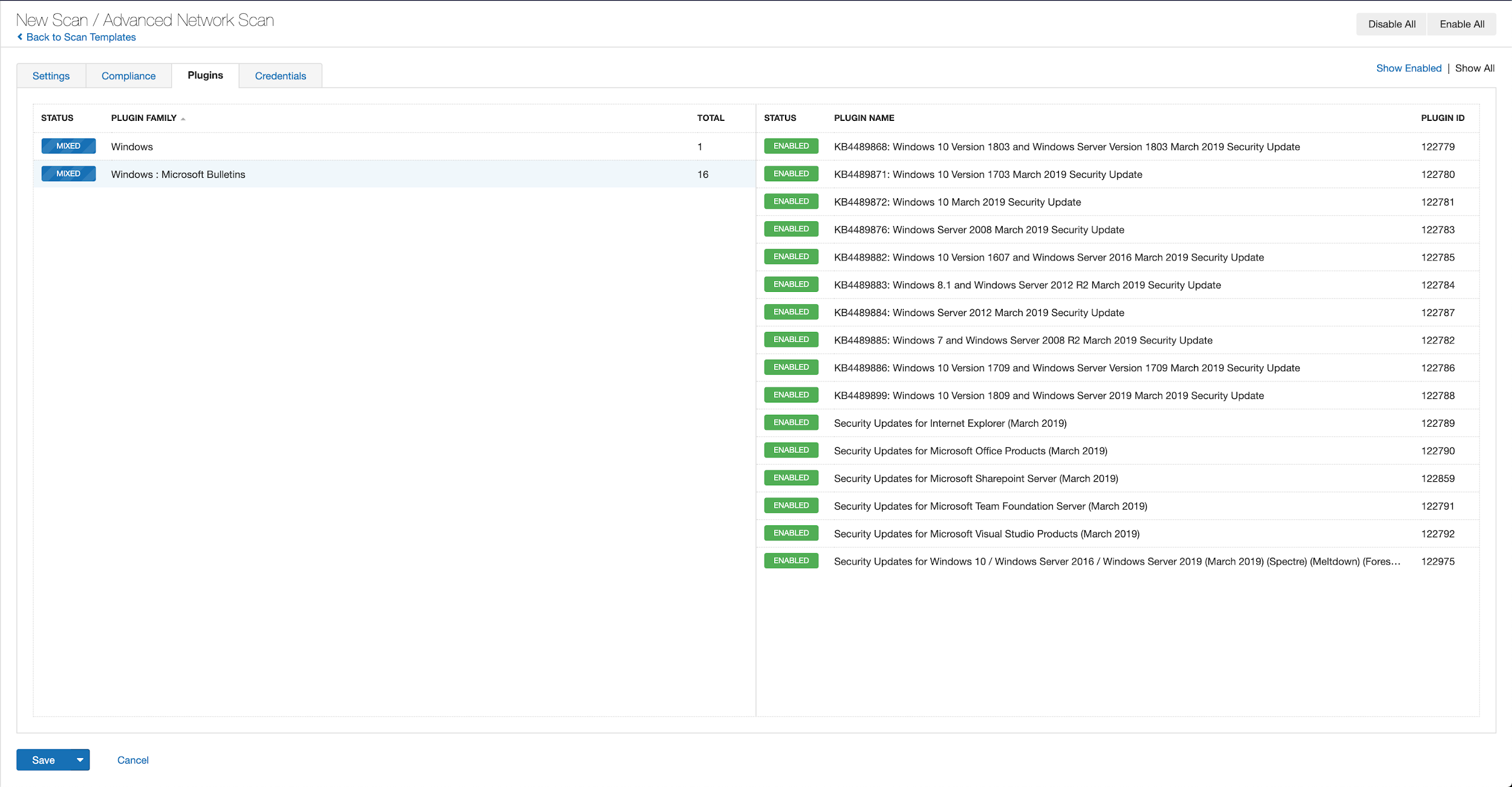
Users can create scans that focus specifically on our Patch Tuesday plugins. From a new advanced scan, in the plugins tab, set an advanced filter for Plugin Name contains July 2021.
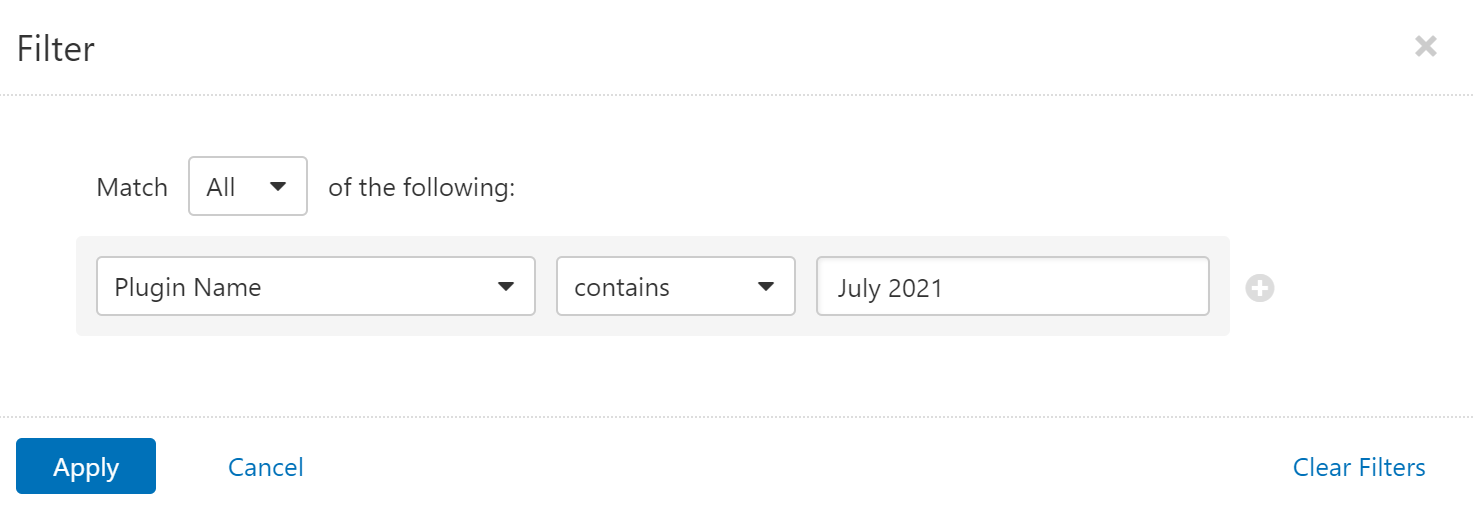
With that filter set, click the plugin families to the left and enable each plugin that appears on the right side. Note: If your families on the left say Enabled, then all the plugins in that family are set. Disable the whole family before selecting the individual plugins for this scan. Here’s an example from Tenable.io:
A list of all the plugins released for Tenable’s July 2021 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
Get more information
- Microsoft's July 2021 Security Updates
- Tenable plugins for Microsoft April 2021 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable, the first Cyber Exposure platform for holistic management of your modern attack surface.
Get a free 30-day trial of Tenable.io Vulnerability Management.
- Vulnerability Management

