Hot Patches for Log4Shell Introduced Multiple Vulnerabilities in Amazon Web Services

Amazon Web Services has addressed vulnerabilities introduced by the hot patches released in response to the Log4Shell vulnerability in December.
Contexte
On April 19, researchers with Palo Alto’s Unit 42 disclosed four vulnerabilities introduced by the hot patches for Amazon Web Services (AWS) in response to CVE-2021-44228, also known as Log4Shell. While there are four CVEs, CVE-2022-0070 and CVE-2022-0071 were assigned to address incomplete patches for CVE-2021-3100 and CVE-2021-3101 respectively, which were initially disclosed in December 2021.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2021-3100 | Apache Log4j Hot Patch Service Execution with Unnecessary Privileges Vulnerability | 8.8 |
| CVE-2021-3101 | Hotdog Hot Patch Solution Execution with Unnecessary Privileges Vulnerability | 8.8 |
| CVE-2022-0070 | Apache Log4j Hotpatch Service Execution with Unnecessary Privileges Vulnerability | 8.8 |
| CVE-2022-0071 | Hotdog Hot Patch Solution Execution with Unnecessary Privileges Vulnerability (Incomplete Fix) | 8.8 |
Analyse
On December 12, in response to the Log4Shell vulnerability, AWS released open source hot patches — short term solutions to be implemented at scale until a more robust fixed version can be deployed — for several environments. These hot patches detect vulnerable Java applications and patch them “on the fly.”
According to the researchers at Unit 42, the hot patch solutions developed to address Log4Shell for standalone servers, Kubernetes clusters, Elastic Container Service (ECS) clusters and Fargate contained “severe security issues.” These hot patches, though from AWS, can be applied to other cloud and on-prem environments.
These issues can be exploited by “every container in [the hot patched] environment” to achieve container escape and host takeover. The vulnerabilities also allow unprivileged processes to escalate privileges and gain code execution with root privileges. The vulnerabilities are not configuration-dependent, they can be exploited in most AWS environments.
Solution
The following is a summary of the solutions for the hot patches:
| Solution | Fixed Version | Mise en production |
|---|---|---|
| Amazon Linux (AMI) | 1.1-16 | log4j-cve-2021-44228-hotpatch |
| Sécurité | 1.1-16 | kubernetes-log4j-cve-2021-44228-node-agent Daemonset |
| Bottlerocket | 1.02 | hotdog-v1.0.2 |
Identification des systèmes affectés
A list of Tenable plugins to identify these vulnerabilities can be found here.
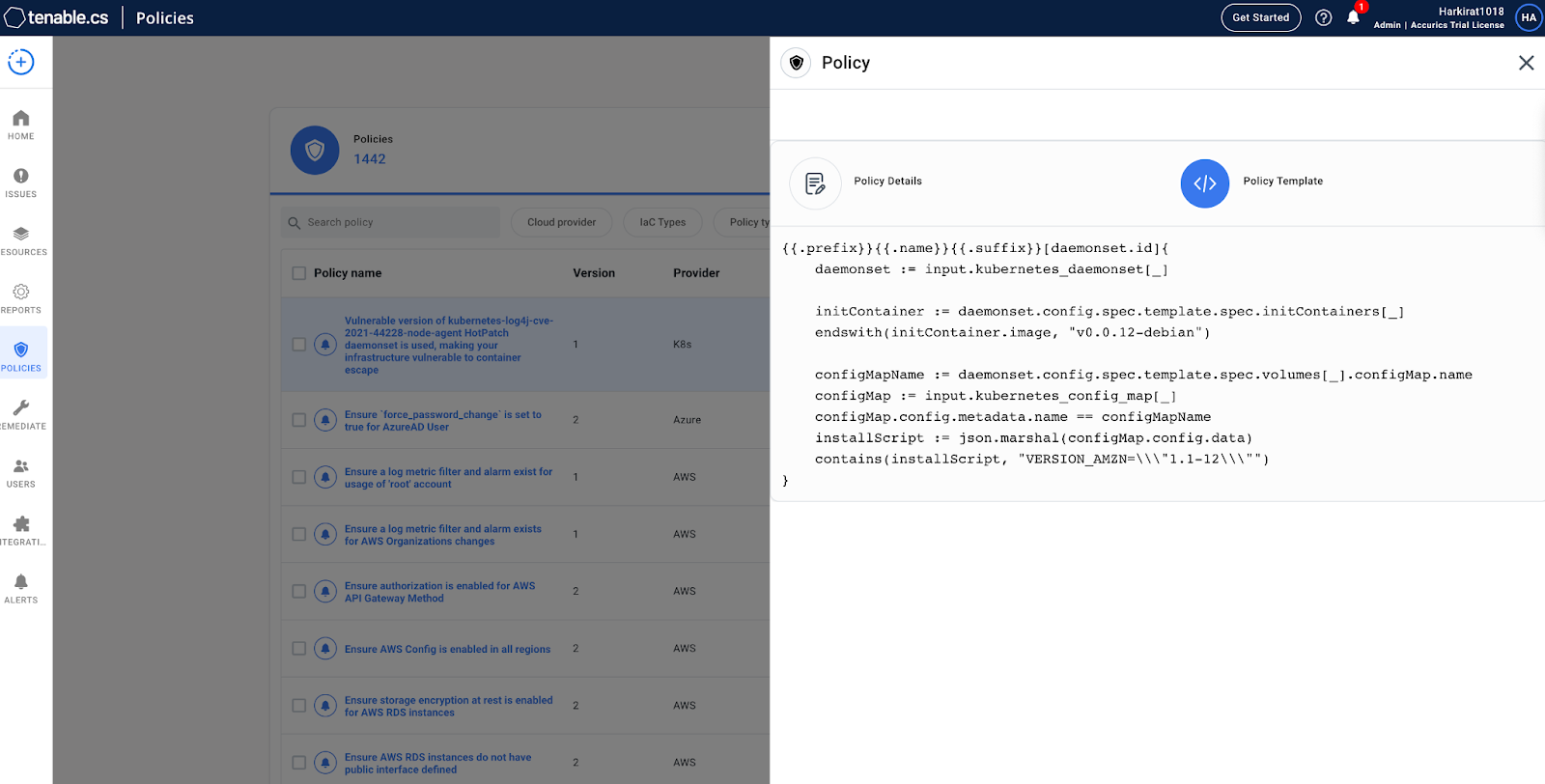
Tenable.cs users can detect vulnerable Kubernetes deployments via the kubernetes-log4j-cve-2021-44228-node-agent hot patch daemonset using open policy agent rego. The rego checks the image version, if it is "v0.0.12-debian" then it finds the corresponding configmap to check the actual package version that the daemonset job will install in the cluster. If Tenable.cs does not detect the fixed version (1.1-16), the product will display an alert.
En savoir plus
- AWS Security Page for CVE-2021-3100, CVE-2021-3101, CVE-2022-0070 and CVE-2022-0071
- Palo Alto’s Unit 42 Blog Post
Rejoignez l'équipe SRT de Tenable sur Tenable Community.
Apprenez-en plus sur Tenable, la première plateforme de Cyber Exposure qui vous permet de gérer votre surface d'attaque moderne de manière globale.
Get a free 30-day trial of Tenable.io Vulnerability Management.

Tenable One
Demandez une démo
La plateforme de gestion de l'exposition alimentée par l'IA leader du secteur
Merci
Nous vous remercions de votre intérêt pour Tenable One.
Un représentant vous contactera prochainement.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success