CVE-2019-11510 :
A proof of concept has been made public for CVE-2019-11510, an arbitrary file disclosure vulnerability found in popular virtual private network software, Pulse Connect Secure.
Background
On April 24, Pulse Secure released a security advisory (later amended to include CVEs on the 25th) and patch for multiple critical and high severity vulnerabilities. The issues were identified in Pulse Connect Secure (PCS), previously known as Juniper SSL Virtual Private Network (VPN), a widely used commercial VPN solution. The issues were found by Orange Tsai and Meh Chang from the DEVCORE research team who shared details on the subject at their Black Hat and DEF CON talks earlier this month in Las Vegas.
Among the most severe issues reported is CVE-2019-11510, an arbitrary file disclosure vulnerability. This flaw could allow an unauthenticated, remote attacker to read the contents of files found on a vulnerable device, including sensitive information such as configuration settings.
Analyse
In order to exploit the issue, an attacker can send a malicious HTTP request containing directory traversal sequences along with a crafted Uniform Resource Identifier (URI) and access any file on the device. This provides the attacker access to sensitive device information, and as the researchers describe in their initial report of the issue, this attack could be chained with other vulnerabilities they discovered.
When a user logs into the admin interface of the VPN, their plain-text password is stored in /data/runtime/mtmp/lmdb/dataa/data.mdb. Using the method described above, the attacker could obtain the file, extract the user’s password, and log into the device. Once logged in, the attacker can take advantage of CVE-2019-11539, a command injection vulnerability in the administrative web interface. Alternatively, with the user’s credentials in hand, the attacker could exploit CVE-2019-11508, a vulnerability in the Network File Share (NFS), which allows an authenticated user to upload a malicious file and write arbitrary files to the host.
This research demonstrates how an attacker can take advantage of a pre-authentication flaw and achieve command execution by chaining multiple vulnerabilities to compromise a vulnerable device. What is most concerning about these chained exploits is that PCS is used to restrict external access to an environment, and by achieving command execution on the device, an attacker could use this access to weaponize the device and use it for malicious purposes such as data exfiltration.
If the attacker is not able to find cached credentials, they can access the file /data/runtime/mtmp/system to gather a list of users and hashed passwords. With enough time, effort, and processing power, an attacker could crack the hashes, giving them the ability to log in with the stolen credentials.
Adding to the concern over the potential to exploit these flaws, a Shodan search lists more than 42,000 devices that may be affected if proper patches have not yet been applied.
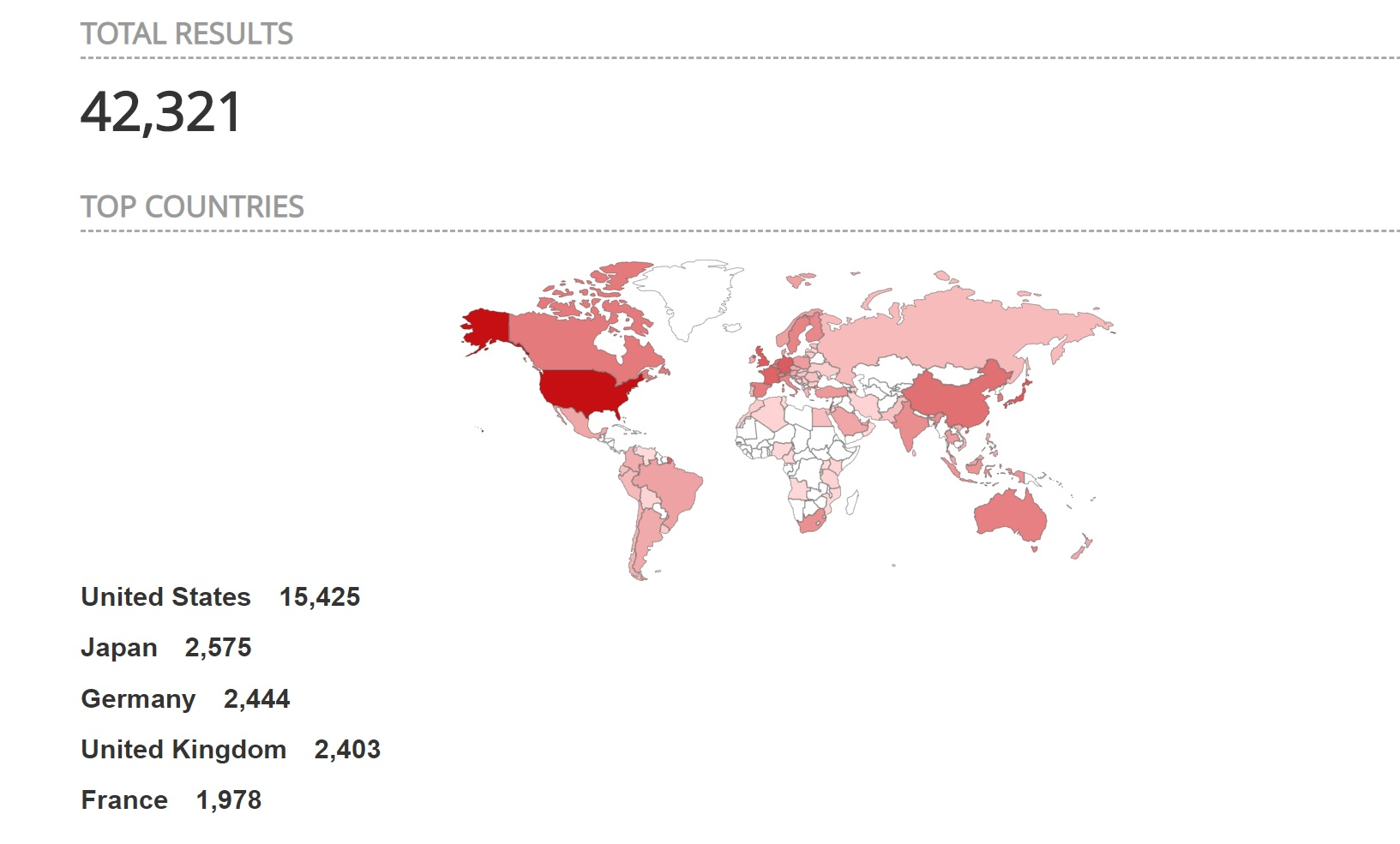
Image source: https://www.shodan.io
A breakdown of the CVEs and the PCS versions affected are outlined below:
| CVE | CVSSv3 (Vendor Assigned) | NVD CVSSv3 Score | Tenable VPR | Versions of Pulse Connect Secure Affected |
|---|---|---|---|---|
| CVE-2019-11510 | 10 (AV:N/AC:L/PR:N/UI:N/S:C/C:H/I:N/A:N) | 8.8 (AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) | 9.9 | 9.0RX, 8.3RX, 8.2RX Note: 8.1RX and below are not directly impacted |
| CVE-2019-11508 | 9.9 (AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:H) | 7.2 (AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) | 5.9 | 9.0RX, 8.3RX, 8.2RX, 8.1RX |
| CVE-2019-11540 | 8.3 (AV:N/AC:H/PR:N/UI:R/S:C/C:H/I:H/A:H) | 9.8 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H) | 6.7 | 9.0RX, 8.3RX |
| CVE-2019-11543 | 8.3 (AV:N/AC:H/PR:N/UI:R/S:C/C:H/I:H/A:H) | 6.1 (AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N | 3 | 9.0RX, 8.3RX, 8.1RX |
| CVE-2019-11541 | 8.3 (AV:N/AC:L/PR:N/UI:N/S:C/C:L/I:L/A:L) | 7.5 (AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:N/A:N) | 3.6 | 9.0RX, 8.3RX, 8.2RX |
| CVE-2019-11542 | 8.0 (AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:H/A:H) | 7.2 (AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) | 5.9 | 9.0RX, 8.3RX, 8.2RX, 8.1RX |
| CVE-2019-11539 | 8.0 (AV:N/AC:H/PR:H/UI:N/S:C/C:H/I:H/A:H) | 7.2 (AV:N/AC:L/PR:H/UI:N/S:U/C:H/I:H/A:H) | 8.4 | 9.0RX, 8.3RX, 8.2RX, 8.1RX |
| CVE-2019-11538 | 7.7 (AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:N/A:N) | 7.7 (AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:N/A:N) | 4.4 | 9.0RX 8.3RX 8.2RX 8.1RX |
| CVE-2019-11509 | 6.4 (AV:N/AC:H/PR:H/UI:R/S:U/C:H/I:H/A:H) | 8.8 (AV:N/AC:L/PR:L/UI:N/S:U/C:H/I:H/A:H) | 5.9 | 9.0RX 8.3RX 8.2RX 8.1RX |
| CVE-2019-11507 | 5.8 (AV:N/AC:H/PR:N/UI:R/S:C/C:L/I:L/A:L) | 6.1 (AV:N/AC:L/PR:N/UI:R/S:C/C:L/I:L/A:N) | 3 | 9.0RX 8.3RX |
* Please note Tenable VPR scores are calculated nightly. This blog was updated on August 29 to reflect current VPR scores.
Démonstration de faisabilité (PoC)
A proof of concept (PoC) was published to the Exploit Database on August 20 as an exploit module written by Alyssa Herrera and Justin Wagner.
Solution
Pulse Secure has published a security advisory with information on each of the CVEs reported. Patching solutions are listed below:
| Version installed | Fixed release |
|---|---|
| Pulse Connect Secure 9.0RX | Pulse Connect Secure 9.0R3.4 & 9.0R4 |
| Pulse Connect Secure 8.3RX | Pulse Connect Secure 8.3R7.1 |
| Pulse Connect Secure 8.2RX | Pulse Connect Secure 8.2R12.1 |
| Pulse Connect Secure 8.1RX | Pulse Connect Secure 8.1R15.1 |
Identifying affected systems
A list of Tenable plugins to identify these vulnerabilities is listed here including a direct exploit check for CVE-2019-11510 (Plugin ID 127897).
En savoir plus
Rejoignez l'équipe SRT de Tenable sur Tenable Community.
Apprenez-en plus sur Tenable, la première plateforme de Cyber Exposure qui vous permet de gérer votre surface d'attaque moderne de manière globale. Get a free 60-day trial of Tenable.io.
