by Cesar Navas
December 16, 2016
Organizations that must comply with Canadian regulatory controls need a consistent and structured way to meet compliance requirements. The Communications Security Establishment Canada (CSEC) developed a series of guidelines for security practitioners in managing information technology (IT) security risks for Government of Canada (GC) information systems. The ITSG-33, IT Security Risk Management: A Lifecycle Approach provides a comprehensive set of security controls that will be used to support a wide variety of business requirements. To support interoperability needs, the ITSG-33 guide is consistent with controls published in the U.S. National Institute of Standards and Technology (NIST) Special Publication 800-53. The standard does not explicitly state how to validate these settings in a cohesive and straightforward interface. Analysts within an organization must ensure that the compliance standard is followed, but also ensure the organization is continually compliant.
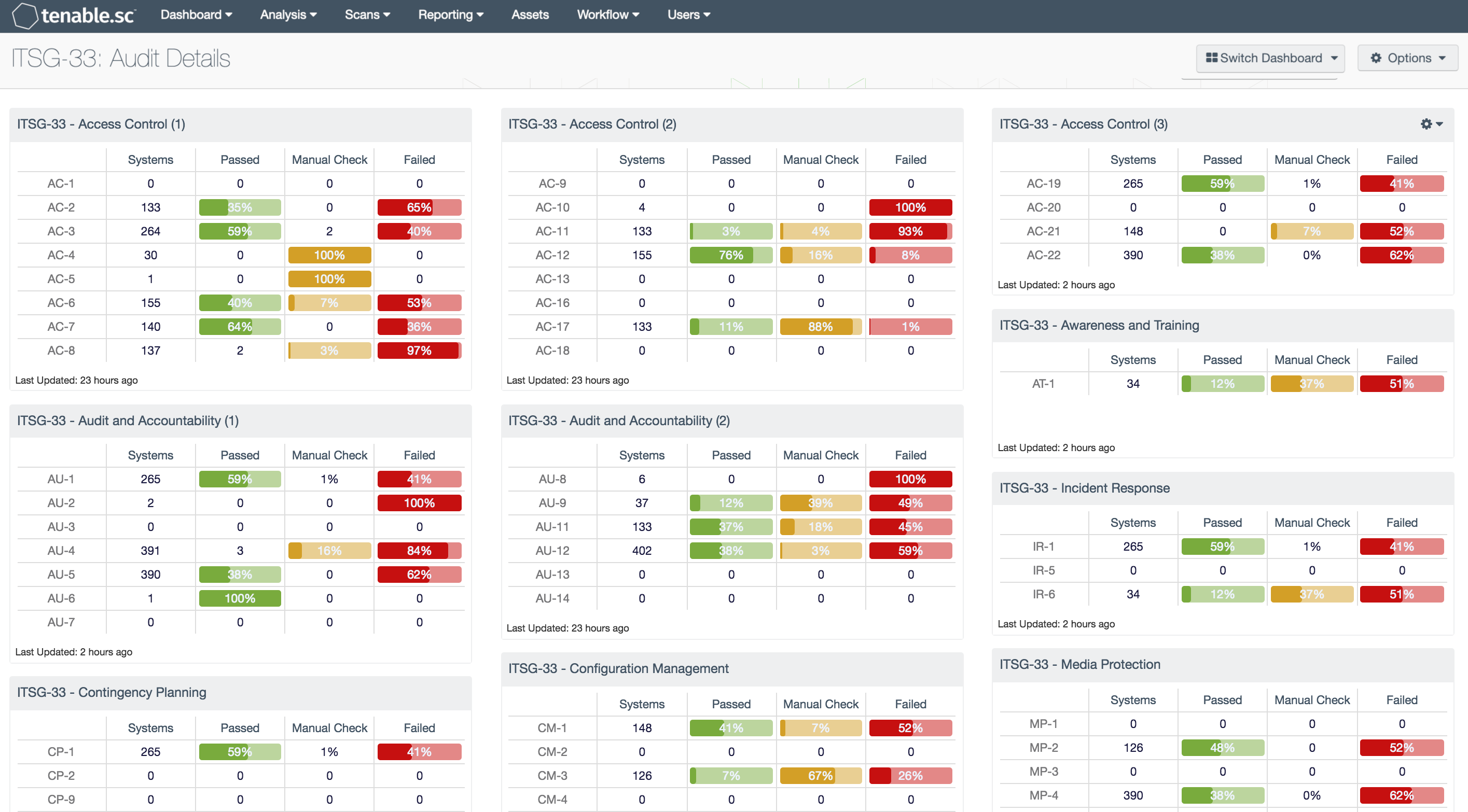
This dashboard covers all the ITSG-33 families currently supported by Tenable audit files, which provide the results of an audit check as one of three severity levels. Analysts are able to see on a continual basis the status of the organization and the posture of being compliant with ITSG-33 controls. The ITSG-33 families and controls are not a checklist-type compliance standard like HIPAA, PCI, or CSF; rather, they are a catalog of controls that are used in achieving compliance with the aforementioned standards. Analysts are presented with concise information of the status of the checks such as an informational severity level is considered a pass. The pass is achieved when the configuration setting matches the expected result of the audit check. The match can be a defined value or a range of values. The “Nessus Compliance Checks” document, available in the Support Portal, contains details on how to edit the audit files. When an audit check fails, the severity is set to high, indicating that the collected result and the expected result do not match. A mismatch may not mean a failure. Each failure should be reviewed and verified to ensure the expected result is correct. If the expected result is not correct, then the audit file should be modified and the scan should be run again. Results assigned a medium severity must be evaluated by an analyst to determine whether the results are applicable or not.
The components in this dashboard use audit files (released after 1 July 2013), which incorporate the reference tag that maps many audit checks to a respective standard. In the case of this dashboard, the audit files must contain a string similar to 'ITSG-33|IA-5' on the reference line of the applicable audit check. Where multiple components are required, a number in parentheses will be displayed. Analysts can use this method to search with cross references in the “Analysis” feature in Tenable.sc to further research specific compliance plugins and see their results.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, ARC, and assets. The dashboard can be easily located in the Tenable.sc Feed by selecting category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.4.2
- Nessus 8.5.1
- NNM 5.9.0
- LCE 6.0.0
- Audit Files containing ITSG-33 references
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and assists in securing an organization’s internal network. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and regulatory compliance framework such as ITSG-33. Active scanning periodically examines systems to detect vulnerabilities within operating systems, software applications, and hardware. Agent scanning enables scanning and detection of vulnerabilities on transient and isolated devices. Passive listening provides real-time discovery of vulnerabilities on operating systems, protocols, network services, wireless devices, web applications, and critical infrastructure. Host data and data from other security products is analyzed to monitor activity from patch management solutions and services. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to fully understand the impact of vulnerabilities on the network.
The ITSG-33 controls within the components in this dashboard include:
- Access Control (1): This component monitors the following ITSG-33 audit controls: AC-1, AC-2, AC-3, AC-4, AC-5, AC-6, AC-7, and AC-8
- Access Control (2): This component monitors the following ITSG-33 audit controls: AC-9, AC-10, AC-11, AC-12, C-13, C-16, AC-17, and AC-18
- Access Control (3): This component monitors the following ITSG-33 audit controls: AC-19, AC-20, AC-21, and AC-22
- Audit and Accountability (1): This component monitors the following ITSG-33 audit controls: AU-1, AU-2, AU-3, AU-4, AU-5, AU-6, and AU-7
- Audit and Accountability (2): This component monitors the following ITSG-33 audit controls: AU-8, AU-9, AU-11, AU-12, AU-13, and AU-14
- Awareness and Training: This component monitors the following ITSG-33 audit control: AT-1
- Configuration Management: This component monitors the following ITSG-33 audit controls: CM-1, CM-2, CM-3, CM-4, CM-5, CM-6, CM-7, CM-8, CM-9, and CM-11
- Contingency Planning: This component monitors the following ITSG-33 audit controls: CP-1, CP-2, CP-9, and CP-10
- Identification and Authentication: This component monitors the following ITSG-33 audit controls: IA-1, IA-2, IA-3, IA-4, IA-5, IA-6, IA-7, IA-8 and IA-11
- Incident Response: This component monitors the following ITSG-33 audit controls: IR-1, IR-5, and IR-6
- Maintenance: This component monitors the following ITSG-33 audit controls: MA-1, MA-5, and MA-6
- Media Protection: This component monitors the following ITSG-33 audit controls: MP-1, MP-2, MP-3, MP-4, MP-6, MP-7, and MP-8
- Personnel Security: This component monitors the following ITSG-33 audit controls: PS-1, PS-4, PS-5, PS-6, and PS-7
- Physical and Environmental Protection: This component monitors the following ITSG-33 audit controls: PE-1, PE-3, PE-5, PE-16 and PE-19
- Planning: This component monitors the following ITSG-33 audit controls: PL-1, PL-2, PL-5, and PL-8
- Program Management (1): This component monitors the following ITSG-33 audit controls: PM-1, PM-2, PM-4, PM-5, PM-6, and PM-7
- Program Management (2): This component monitors the following ITSG-33 audit controls: PM-8, PM-9, PM-10, PM-11, and PM-14
- Risk Assessment: This component monitors the following ITSG-33 audit controls: RA-1, RA-2, RA-3, and RA-5
- Security Assessment and Authorization: This component monitors the following ITSG-33 audit controls: CA-1, CA-2, CA-3, CA-5, CA-6, and CA-7
- System and Communications Protection Family (1): This component monitors the following ITSG-33 audit controls: SC-1, SC-2, SC-3, SC-4, SC-5, SC-7, SC-8, and SC-9
- System and Communications Protection Family (2): This component monitors the following ITSG-33 audit controls: SC-10, SC-12, SC-13, SC-15, SC-16, SC-17, SC-18, and SC-20
- System and Communications Protection Family (3): This component monitors the following ITSG-33 audit controls: SC-22, SC-23, SC-26, SC-28, and SC-39
- System and Information Integrity (1): This component monitors the following ITSG-33 audit controls: SI-1, SI-2, SI-3, SI-4, SI-5, SI-6, and SI-7
- System and Information Integrity (2): This component monitors the following ITSG-33 audit controls: SI-8, SI-9, SI-10, SI-11, and SI-12.
- System and Services Acquisition: This component monitors the following ITSG-33 audit controls: SA-1, SA-4, SA-6, SA-7, SA-8, SA-10, SA-12, and SA-13