by Stephanie Dunn
May 25, 2016
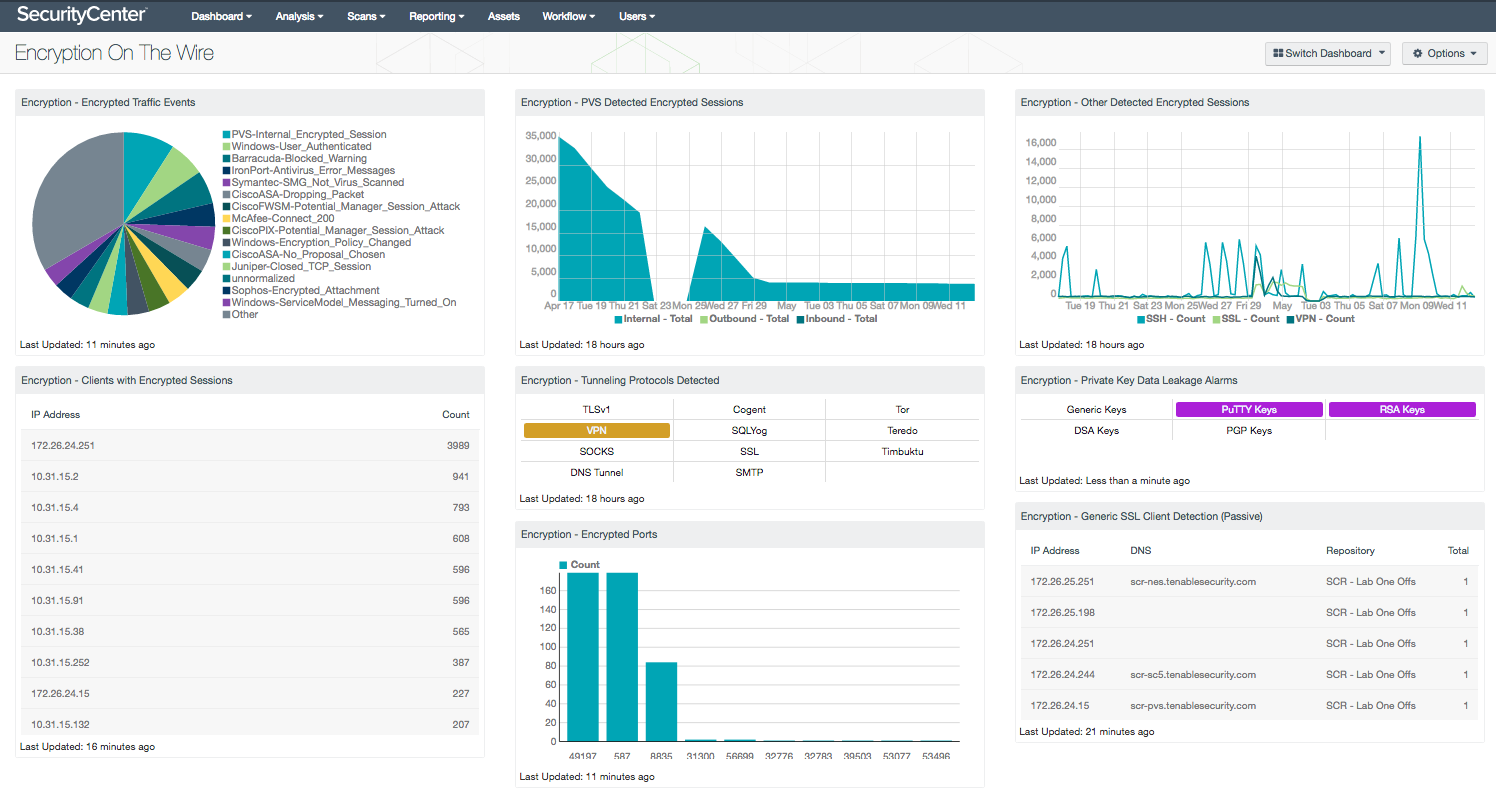
As organizations continue to employ web applications, file storage, and cloud services for business purposes, establishing strong encryption controls can help protect critical data in-transit. Given the rise of these services, malware often utilizes encryption traffic to conceal malicious command and control (C2) activity on the network. This dashboard provides a summary of encrypted communications, which can be useful in identifying malware on compromised hosts, as well as other types of unusual activity on the network.
Modern encryption plays an important role in ensuring data confidentially and integrity. Unfortunately, many organizations use encryption algorithms with weak cryptographic ciphers that can leave critical systems vulnerable to attack or exploitation. Establishing sound encryption policies and knowing what devices, folders, or files need to be encrypted can serve as a great starting point for organizations. Compliance requirements can also play a factor in establishing encryption policies. Some examples include the National Institute of Standards and Technology (NIST) SP 800-52 Rev. 1, and the PCI DSS v3.2 that require the use of strong cryptography using current TLS versions, as earlier versions of TLS and SSL are highly insecure. Most compliance frameworks today provide guidance on how to best establish and implement encryption within the enterprise. Monitoring and employing strong encryption controls can help to ensure that all organizational data remains secure.
This dashboard will provide insight into encrypted network traffic and ports in use. Encrypted traffic logs are normalized and correlated by the Tenable Log Correlation Engine (LCE) from network devices and applications, and provide insight into services processing encrypted traffic. The Tenable Passive Vulnerability Scanner (PVS) has the ability to monitor encrypted traffic on the wire from protocols such as SSH, HTTPS, and other services that encrypt network traffic. Information on both source and destination traffic can be useful in detecting common encryption ports being used by malware. Several components monitor authorized remote access events, as well as any suspicious encrypted sessions, tunneling protocols in use, and unencrypted private keys traversing the network.
This dashboard is available in the SecurityCenter Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the SecurityCenter Feed under the category Discovery & Detection. The dashboard requirements are:
- SecurityCenter 5.3.2
- Nessus 6.6.2
- PVS 5.0.0
- LCE 4.8.0
Tenable provides organizations with proactive continuous monitoring from our unique sensors. Active scanning periodically examines hosts to determine the level of risk posed to the organization. Intelligent connectors leverage other security investments in the environment to integrate security data in order to improve context and analysis. Agent scanning enables organizations to rapidly assess hosts without the need for credentials. Passive listening detects hosts that were offline during active scans, and provides real-time monitoring to collect information about each host, and how the hosts are communicating on the network. Host data is analyzed and monitored to correlate real-time events, and identify malicious activity and anomalous behavior from users, operating systems, network devices, and other critical infrastructure. Each sensor delivers continuous visibility and critical context, enabling decisive action that transforms your security program from reactive to proactive.
The following components are included in this dashboard:
- Encryption – Encrypted Traffic Events: The Encrypted Traffic Events chart presents an overview of encrypted session activity within the last seven days. Encrypted events and activity within the syslog will highlight devices or applications processing encrypted traffic. Information presented within this component can alert the analyst to encrypted network traffic, encrypted email attachments, anti-virus events, and more. This component can be modified to include additional or specific events based on organizational requirements.
- Encryption – Clients with Encrypted Sessions: This component utilizes the IP Summary Tool and the encrypted search term to display encrypted sessions. Hosts found in the event database for the last 25 day timeframe are displayed.
- Encryption – PVS Detected Encrypted Sessions: The PVS Detected Encrypted Sessions component utilizes PVS to present a graphical representation of encrypted sessions on the wire. Three categories are represented: Internal encrypted sessions detected, Outbound encrypted sessions detected, Inbound encrypted sessions detected
- Encryption – Tunneling Protocols Detected: This indicator matrix alert utilizes several passive plugins to determine if any tunneling protocols are detected on the network. While not all protocols are malicious, this indicator provides analysts with the ability to rapidly identify when data that may be of interest is being encapsulated.
- Encryption – Encrypted Ports: The Encrypted Ports chart presents a port summary for detected encrypted sessions within the last seven days. Analysts can use this information to quickly identify any malicious command and control (C2) traffic utilizing encrypted ports. Encrypted traffic logs are normalized and correlated by LCE from network devices and applications, and provide insight into services processing encrypted traffic. In addition, authorized services and applications can be tracked using this component.
- Encryption – Other Detected Encrypted Sessions: This component trends detected SSH, SSL and VPN connections over the last 25 days. This provides a graphical representation of the number of sessions that have occurred from these various types.
- Encryption – Private Key Data Alarms: This component utilizes a series of passive plugins to detect that the remote host has just passed an encryption private key via plaintext on the network. This is a risk in that private keys should only reside on a local system and if they must be passed, they should be encrypted in transit.
- Encryption – Generic SSL Client Detection (Passive): This component utilizes the IP Summary Tool and three passive plugins to display SSL client information contained in the vulnerability database. The plugins utilized are: 5938 and 5977: SSL Client Detection (Passive) and 801050: OpenSSL Detection (LCE)