by Cesar Navas
October 14, 2016
Network attacks typically target servers and perimeter devices in an attempt to infiltrate the network. However, attacks against internal network systems and portable devices are on the rise. Attackers now frequently target vulnerabilities within web browsers due to the popularity and prevalence of these applications within the workplace. Failure to properly secure internal systems can allow attackers to exploit existing vulnerabilities to install malware or exfiltrate confidential data. Systems must be hardened and security policies must be enforced to ensure that a uniform level of security is applied across all network systems. Doing this will increase the overall security of the network and reduce the organization’s overall attack surface, helping to protect data and prevent unauthorized access.
The French Network and Information Security Agency (Agence nationale de sécurité des systèmes d’information or ANSSI) developed the "40 Essential Measures for a Healthy Network" to assist organizations in safeguarding the security of information systems within a network. Following these measures, or rules, for a healthy network will provide basic protection for an organization's critical data. ANSSI states that the majority of IT attacks that have involved ANSSI stepping in could have been prevented had the IT measures set out in the guide been applied.
This dashboard aligns with Section V of the ANSSI 40 Essential Measures for a Healthy Network: Secure Computer Terminals. This section contains six rules:
- Rule 14 focuses on applying a uniform level of security across all systems in the enterprise. Basic measures such as disabling unnecessary services and restricting user account privileges are vital in preventing unauthorized access to or misuse of critical systems.
- Rule 15 addresses the use of portable media as a vector for malware propagation and data exfiltration. Appropriate security restrictions should be implemented to prevent unauthorized media access and the ability to run programs from portable media.
- Rule 16 highlights the use of management tools to ensure that all systems on the network are monitored and updated properly. These tools provide the ability to deploy security policies and updates to devices.
- Rule 17 emphasizes applying strong security policies on portable devices. Due to the environments in which portable devices are used, additional security features such as enhanced authentication may be warranted.
- Rule 18 advises prohibiting remote connections to client machines whenever possible. This rule references the “Security recommendations for remote assistance” (Recommandations de sécurité relatives à la téléassistance) document, which provides recommendations on securing remote access using Remote Desktop Protocol (RDP) and Virtual Network Computing (VNC).
- Rule 19 addresses encrypting sensitive data, especially on mobile devices. Loss or theft of an unencrypted mobile or portable device can be devastating for an organization. Using full disk encryption provides an effective method to ensure data security and integrity.
This dashboard will enable organizations to better monitor their network system hardening practices and their security policy enforcement. Using this dashboard, an organization will be able to obtain information about configuration compliance failures and other policy-related concerns such as remote access and the use of portable devices and removable media. This information will assist the organization in securing their computer terminals and ultimately safeguarding critical assets and data.
Several components within this dashboard display compliance concerns, in order to assist analysts in identifying misconfigurations and weak settings on internal hosts. Indicators will alert analysts to removable devices that have been detected on the network. Information on policy events will highlight policy changes and concerns. Remote access activity is presented, which can help to ensure that access is restricted and secured properly. Additional indicators highlight exploitable vulnerabilities in operating systems, web applications and technologies, open source software, and other areas. This dashboard provides visibility into network system compliance concerns and vulnerabilities, which can help organizations secure their network systems more effectively.
This dashboard is available in the Tenable.sc Feed, a comprehensive collection of dashboards, reports, Assurance Report Cards, and assets. The dashboard can be easily located in the Tenable.sc Feed under the category Compliance & Configuration Assessment. The dashboard requirements are:
- Tenable.sc 5.3.2
- Nessus 8.5.1
- LCE 6.0.0
- NNM 5.9.1
- Compliance data
The dashboard contains the following components:
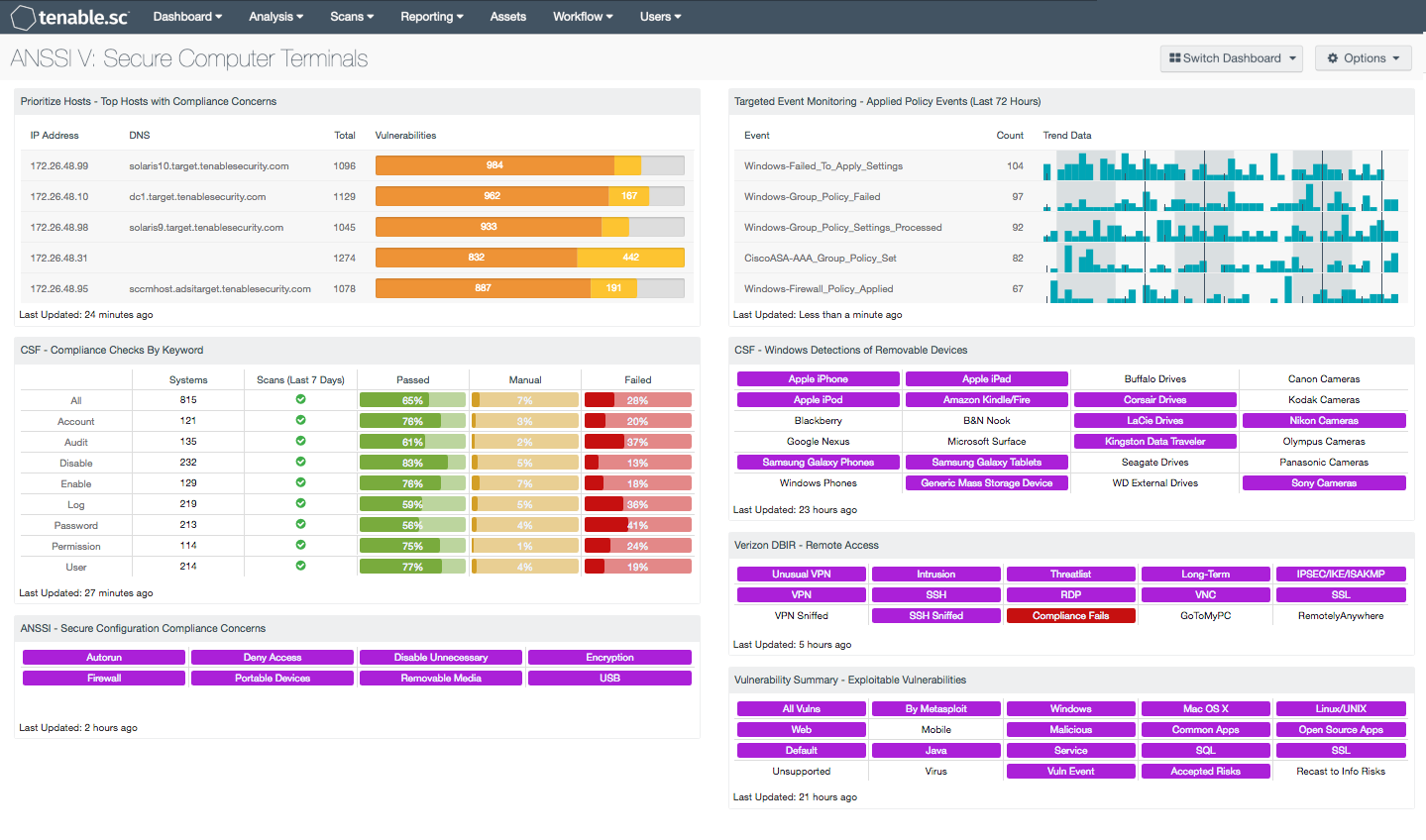
- Prioritize Hosts - Top Hosts with Compliance Concerns - This table displays the top hosts on the network that have either compliance failures or compliance checks that must be performed manually.
- CSF - Compliance Checks By Keyword - The Compliance Checks by Keyword component uses results from the compliance audit to trigger on specific plugin keywords.
- ANSSI - Secure Configuration Compliance Concerns - This component presents compliance concerns pertaining to secure system configuration.
- Targeted Event Monitoring - Applied Policy Events (Last 72 Hours) - This component presents policy events detected over the last 72 hours.
- CSF - Windows Detections of Removable Devices - This component presents a matrix of Windows detections of removable storage devices.
- Verizon DBIR - Remote Access - The Verizon DBIR notes that it is important to restrict remote access to systems. This matrix assists the organization in monitoring its remote access.
- Vulnerability Summary - Exploitable Vulnerabilities - This matrix displays warning indicators for exploitable vulnerabilities actively and passively detected on the network.
Tenable's Tenable.sc Continuous View (CV) is the market-defining continuous network monitoring solution, and can assist an organization in securing computer terminals. Tenable.sc CV is continuously updated with information about advanced threats, zero-day vulnerabilities, and new regulatory compliance data. Active scanning periodically examines systems to find vulnerabilities, and can also make use of audit files to assess compliance. Passive listening provides real-time monitoring to collect information about systems and vulnerabilities. Host data and data from other security devices is analyzed to monitor policy and configuration settings activity. Tenable.sc CV provides an organization with the most comprehensive view of the network and the intelligence needed to secure systems and safeguard critical assets and information.