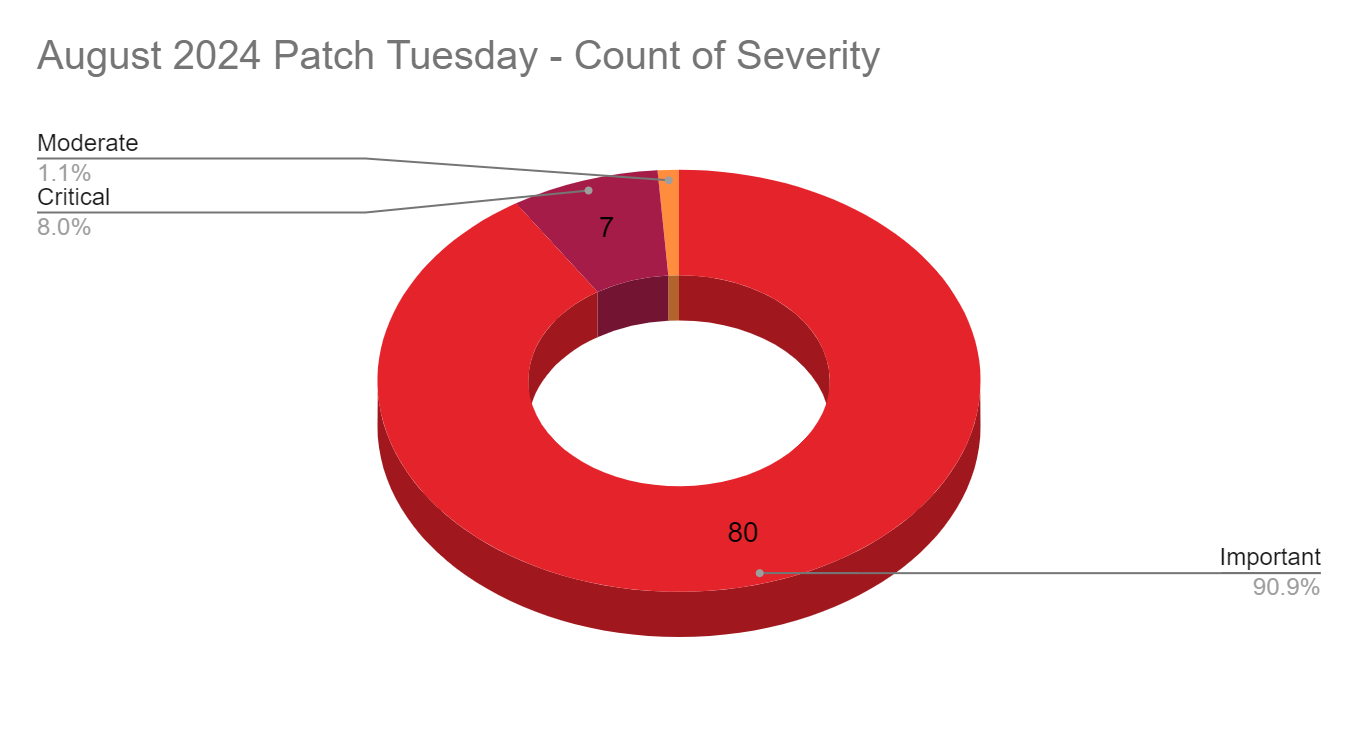
Microsoft’s August 2024 Patch Tuesday Addresses 88 CVEs

- 7Critical
- 80Important
- 1Moderate
- 0Low
Microsoft addresses 88 CVEs with seven critical vulnerabilities and 10 zero-day vulnerabilities, six of which were exploited in the wild.
Microsoft patched 88 CVEs in its August 2024 Patch Tuesday release, with seven rated critical, 80 rated as important, and one rated as moderate.
This month’s update includes patches for:
- .NET and Visual Studio
- Azure Connected Machine Agent
- Azure CycleCloud
- Azure Health Bot
- Azure IoT SDK
- Azure Stack
- Line Printer Daemon Service (LPD)
- Microsoft Bluetooth Driver
- Microsoft Copilot Studio
- Microsoft Dynamics
- Microsoft Edge (Chromium-based)
- Microsoft Local Security Authority Server (lsasrv)
- Microsoft Office
- Microsoft Office Excel
- Microsoft Office Outlook
- Microsoft Office PowerPoint
- Microsoft Office Project
- Microsoft Office Visio
- Microsoft Streaming Service
- Microsoft Teams
- Microsoft WDAC OLE DB provider for SQL
- Microsoft Windows DNS
- Reliable Multicast Transport Driver (RMCAST)
- Windows Ancillary Function Driver for WinSock
- Windows App Installer
- Windows Clipboard Virtual Channel Extension
- Windows Cloud Files Mini Filter Driver
- Windows Common Log File System Driver
- Windows Compressed Folder
- Windows Deployment Services
- Windows DWM Core Library
- Windows Initial Machine Configuration
- Windows IP Routing Management Snapin
- Windows Kerberos
- Windows Kernel
- Windows Kernel-Mode Drivers
- Windows Layer-2 Bridge Network Driver
- Windows Mark of the Web (MOTW)
- Windows Mobile Broadband
- Windows Network Address Translation (NAT)
- Windows Network Virtualization
- Windows NT OS Kernel
- Windows NTFS
- Windows Power Dependency Coordinator
- Windows Print Spooler Components
- Windows Resource Manager
- Windows Routing and Remote Access Service (RRAS)
- Windows Scripting
- Windows Secure Kernel Mode
- Windows Security Center
- Windows SmartScreen
- Windows TCP/IP
- Windows Transport Security Layer (TLS)
- Windows Update Stack
- Windows WLAN Auto Config Service
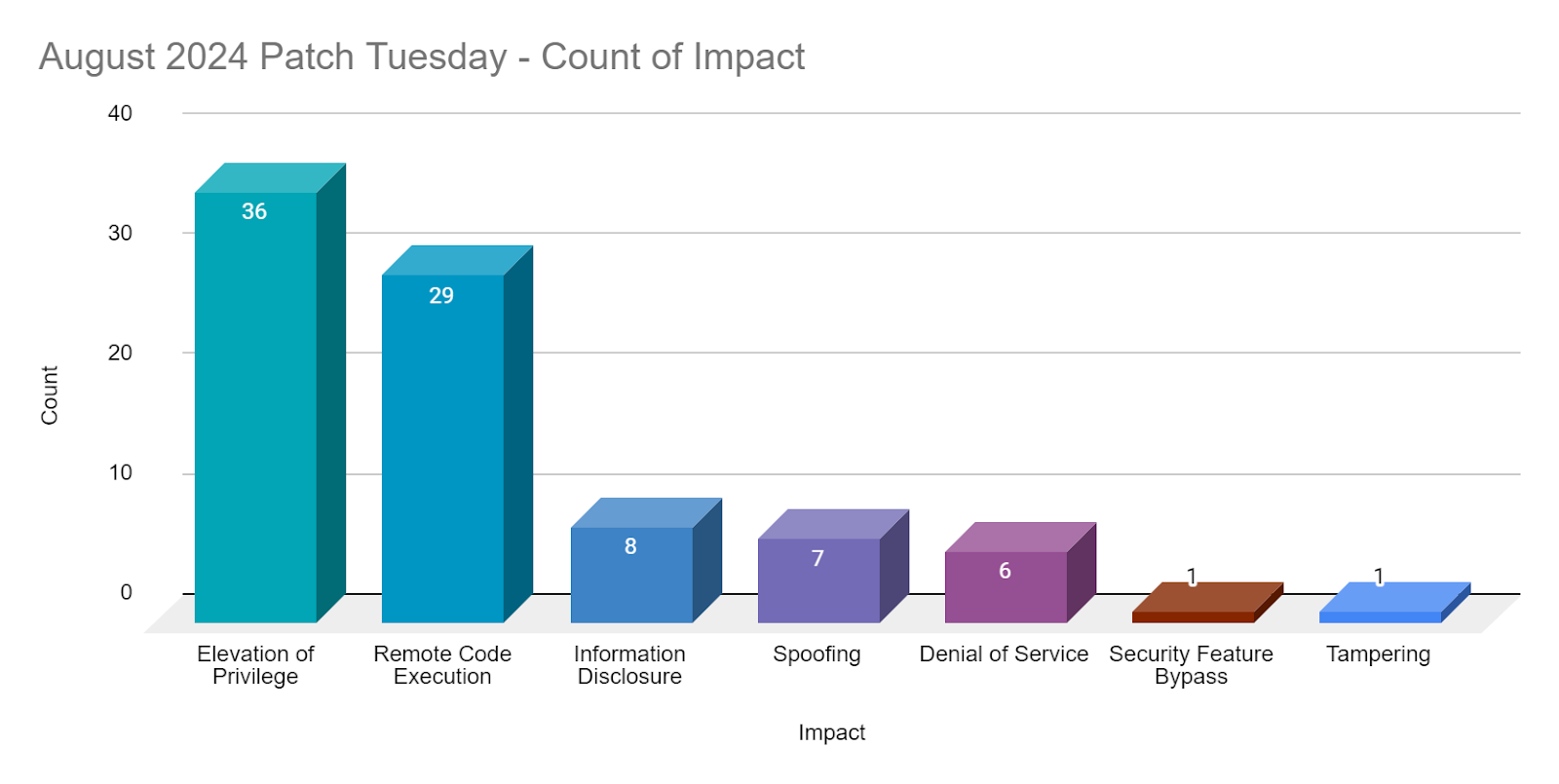
Elevation of Privilege (EoP) vulnerabilities accounted for 41% of the vulnerabilities patched this month, followed by Remote Code Execution (RCE) at 33%.
CVE-2024-38206 | Microsoft Copilot Studio Information Disclosure Vulnerability
CVE-2024-38206 is a critical severity information disclosure vulnerability affecting Microsoft’s Copilot Studio, an AI-powered chatbot. This vulnerability received a CVSSv3 score of 8.5 and could be abused by an authenticated attacker to bypass server-side request forgery (SSRF) protections in order to leak potentially sensitive information. The vulnerability was released by Microsoft on August 6, with the advisory noting that no user action is required as the issue has been patched by Microsoft. This vulnerability was discovered and reported to Microsoft by Tenable researcher Evan Grant.
CVE-2024-38109 | Azure Health Bot Elevation of Privilege Vulnerability
CVE-2024-38109 is a critical severity EoP vulnerability affecting Azure Health Bot. This vulnerability received a CVSSv3 score of 9.1 and is the result of a SSRF vulnerability in Azure Health Bot that can be abused to escalate privileges. This vulnerability was discovered by Tenable researcher Jimi Sebree and responsibly disclosed to Microsoft. The issue has been patched by Microsoft and no action is required for users of the Health Bot service. For more information on this vulnerability, please refer to Tenable Research Advisories TRA-2024-27 and TRA-2024-28, as well as our blog post.
CVE-2024-38106, CVE-2024-38133 and CVE-2024-38153 | Windows Kernel Elevation of Privilege Vulnerability
CVE-2024-38106, CVE-2024-38133 and CVE-2024-38153 are EoP vulnerabilities affecting the Windows Kernel. CVE-2024-38133 and CVE-2024-38153 received CVSSv3 scores of 7.8, while CVE-2024-38106 was scored as a 7. Despite the lower severity and the exploitability requirements of the attacker needing to win a race condition for successful exploitation, CVE-2024-38106 was reportedly exploited in the wild as a zero-day. CVE-2024-38133 and CVE-2024-38153 were not listed as being exploited, however CVE-2024-38133 was rated as “Exploitation More Likely” according to the Microsoft Exploitability Index. Successful exploitation of these vulnerabilities could allow the attacker to elevate privileges to SYSTEM.
CVE-2024-38107 | Windows Power Dependency Coordinator Elevation of Privilege Vulnerability
CVE-2024-38107 is an EoP Vulnerability affecting Windows Power Dependency Coordinator (pdc.sys), a driver responsible for power management on a Windows system. This vulnerability was exploited in the wild as a zero-day, though no specific details about exploitation were available at the time this blog was published. Microsoft provided a CVSSv3 score of 7.8 for this vulnerability and patches are available for all supported versions of Windows and Windows Server.
CVE-2024-38178 | Scripting Engine Memory Corruption Vulnerability
CVE-2024-38178 is a Scripting Engine memory corruption vulnerability in Windows Scripting. This vulnerability was assigned a CVSSv3 score of 7.5 and Microsoft notes that exploitation has been observed. According to Microsoft, an authenticated victim must have Edge in Internet Explorer Mode as a prerequisite for exploitation prior to an unauthenticated attacker convincing the victim to click a specially crafted URL to obtain RCE.
CVE-2024-38189 | Microsoft Project Remote Code Execution Vulnerability
CVE-2024-38189 is a RCE vulnerability affecting Microsoft Project, a project management tool. This vulnerability received a CVSSv3 score of 8.8 and was exploited in the wild. According to the advisory, exploitation requires an unsuspecting victim to open a crafted Microsoft Office Project file. Additionally, the system must be configured to have the “Block macros from running in Office files from the Internet policy” disabled as well as have the VBA Macro Notification Settings disabled in order for a successful attack. Micsoft’s advisory does clarify that the Preview Pane is not an attack vector for this vulnerability and offers mitigation options to protect systems if immediate patching cannot be immediately performed.
CVE-2024-38141 and CVE-2024-38193 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability
CVE-2024-38141 and CVE-2024-38193 are EoP vulnerabilities affecting the Windows Ancillary Function Driver for Winsock (afd.sys). Both of these vulnerabilities were given CVSSv3 scores of 7.8 and can allow an attacker to escalate privileges to SYSTEM. CVE-2024-38141 is rated as “Exploitation More Likely” and CVE-2024-38193 was reported to have been exploited in the wild as a zero-day vulnerability.
CVE-2024-38213 | Windows Mark of the Web Security Feature Bypass Vulnerability
CVE-2024-38213 is a security feature bypass vulnerability with an assigned CVSSv3 score of 6.5. Exploitation of this vulnerability requires a user to open a specially crafted file, which could be hosted on a file server, website or sent via a phishing email. If the attacker is successful in convincing a victim to open this file, they could bypass the Windows SmartScreen user experience. Microsoft has flagged this as “Exploitation Detected” as they are aware of an instance of this vulnerability being exploited.
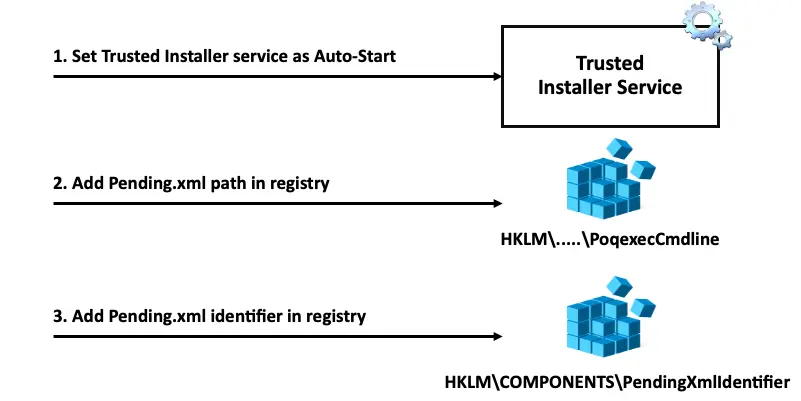
CVE-2024-38163 and CVE-2024-38202 | Windows Update Stack Elevation of Privilege Vulnerability
CVE-2024-38163 and CVE-2024-38202 are both EoP vulnerabilities in Windows Update Stack and were assigned CVSSv3 scores of 7.8 and 7.3 respectively. CVE-2024-38163, if successfully exploited could result in gaining SYSTEM privileges. Microsoft has noted that users don’t need to take any action for this vulnerability as it is only exploitable at run time and the impacted version of WinRE has been superseded by a new version.
CVE-2024-38202 was disclosed and presented at BlackHat USA 2024 and DEF CON 32 by SafeBreach Labs researcher Alon Leviev prior to the August 2024 Patch Tuesday release. The vulnerability which exists in Windows Backup, allows a user with basic privileges to “reintroduce previously mitigated vulnerabilities or circumvent some features of Virtualization Based Security (VBS)”. Leviev identified the vulnerability in the Windows Update mechanism that could allow unauthorized elevation of privileges by enforcing the downgrade of system components. This vulnerability exposes systems to previously patched exploits, making them susceptible to attacks that could leverage these old vulnerabilities. Microsoft has noted that “an attacker attempting to exploit this vulnerability requires additional interaction by a privileged user to be successful.” Microsoft issued an advisory in coordination with this disclosure at Black Hat.
Source: Leviev's SafeBreach Blog
CVE-2024-21302 and CVE-2024-38142 | Windows Secure Kernel Mode Elevation of Privilege Vulnerability
CVE-2024-21302 and CVE-2024-38142 are both elevation of privilege vulnerabilities in Windows Secure Kernel with an exploitability assessment by Microsoft as “Exploitation Less Likely”. CVE-2024-21302 carries a CVSSv3 score of 6.7 and CVE-2024-38142 a score of 7.8 with successful exploitation of either of these vulnerabilities resulting in an attacker gaining SYSTEM privileges.
CVE-2024-21302 was disclosed at Black Hat USA 2024 by the previously mentioned security researcher, Alon Leviev. Leviev demonstrated that CVE-2024-21302 could be chained with CVE-2024-38202 to downgrade or roll back software versions without the need for interaction from a victim with elevated privileges. The result of this chained attack is the target device could be made susceptible to previously patched vulnerabilities, increasing the attack surface of the device. CVE-2024-21302 was also included in the previously mentioned Microsoft advisory released in coordination with the disclosure at Black Hat.
CVE-2024-38199 | Windows Line Printer Daemon (LPD) Service Remote Code Execution Vulnerability
CVE-2024-38199 is a RCE vulnerability in Windows Line Printer Daemon (LPD) Service. The flaw was assigned a CVSSv3 score of 9.8 and rated “Exploitation Less Likely” by Microsoft. A remote attacker could exploit this across a network by dispatching a specially crafted print task to Windows LPD Service, if successful it would result in RCE on the server. Microsoft has also noted that it was publicly disclosed prior to a patch being available.
CVE-2024-38200 | Microsoft Office Spoofing Vulnerability
CVE-2024-38200 is a spoofing vulnerability affecting Microsoft Office with a CVSSv3 score of 6.5 and rated by Microsoft as “Exploitation Less Likely”. An attacker could leverage this vulnerability with a specially crafted file that a victim would need to interact with. This could be achieved by hosting it on a file server or website and convincing the victim to click on the file or similarly it could be included in a phishing email. Successful exploitation of the vulnerability could result in the victim exposing NTLM (New Technology Lan Manager) hashes to a remote attacker.
CVE-2024-38200 was publicly disclosed on August 8 at DEF CON 32 by Jim Rush and Tomais Williamson, both Senior Security Consultants at PrivSec Consulting. Patches for this vulnerability were released today as part of the August 2024 Patch Tuesday released, however on August 10, Microsoft provided mitigations in coordination with this disclosure prior to the patch being released.
CVE-2024-38063 | Windows TCP/IP Remote Code Execution Vulnerability
CVE-2024-38063 is a critical RCE vulnerability affecting Windows TCP/IP. It received a CVSSv3 score of 9.8 and is rated as “Exploitation More Likely.” An attacker could remotely exploit this vulnerability by sending specially crafted IPv6 packets to a host. Microsoft’s mitigation suggestions suggest disabling IPv6 as only IPv6 packets can be abused to exploit this vulnerability. Microsoft has released patches for all supported versions of Windows and Windows Server, including Server Core installations.
Tenable Solutions
A list of all the plugins released for Microsoft’s August 2024 Patch Tuesday update can be found here. As always, we recommend patching systems as soon as possible and regularly scanning your environment to identify those systems yet to be patched.
For more specific guidance on best practices for vulnerability assessments, please refer to our blog post on How to Perform Efficient Vulnerability Assessments with Tenable.
Get more information
- Microsoft's August 2024 Security Updates
- Tenable plugins for Microsoft August 2024 Patch Tuesday Security Updates
Join Tenable's Security Response Team on the Tenable Community.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.
Learn more
- Exposure Management



Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success