Cybersecurity Snapshot: 6 Things That Matter Right Now

Topics that are top of mind for the week ending July 1 | Cybersecurity budgeting priorities. All you ever wanted to know about ransomware. CISOs weigh best-of-breed vs. platforms. The epidemic of identity-related breaches. And much more!
1 -- A penny for your thoughts
How time flies! We’re at the year’s midpoint. That’s when the IT budgeting process often starts. So it seemed timely to poll our webinar attendees on their cybersecurity spending priorities. Check out the results of our admittedly ad-hoc, unscientific – yet interesting! – poll.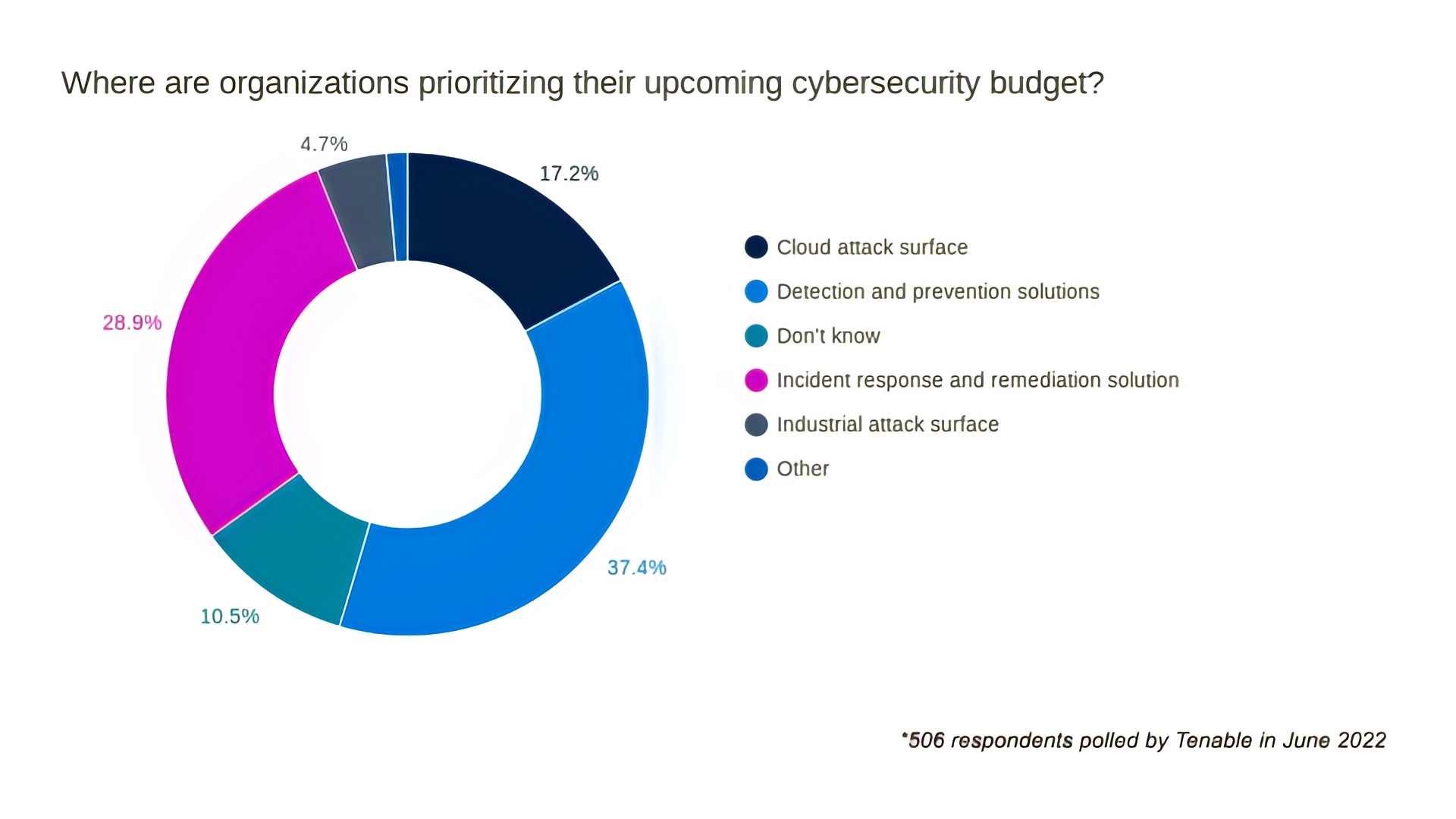
For more on cybersecurity budgeting read:
- “Cybersecurity spending isn't recession-proof. But it's pretty close.” (Protocol)
- “Budgeting for Cybersecurity Requires a New Approach” (CFO.com)
- “2022 Cybersecurity Budgeting: How to Make The Right Requests” (Critical Insight)
- “Smart Cybersecurity Budgeting in the Age of Ransomware” (CPO Magazine)
2 -- Analyst: CISOs shifting from “best of breed” products to platforms
Ah, the age-old debate: best-of-breed (BOB) products versus integrated suites or platforms. Well, this tension is on right now in cybersecurity, as CISOs glance at their security stacks and cringe at this sight: a mishmash of siloed tools from myriad vendors that don’t play well together.
Yes, compiling a BOB stack – long the preferred strategy of cybersecurity teams – is losing its shine, while platforms and integrated products gain favor, according to a study by Enterprise Strategy Group (ESG) and the Information Systems Security Association (ISSA), based on a survey of 280 cybersecurity leaders.
Why are CISOs souring on handpicked, arguably superior – yet disconnected – individual products? A major factor is BOB’s operational overhead, an ESG analyst explains.
Interesting findings:
- 38% now tend to buy integrated security platforms rather than BOB products.
- 86% say it is either critical or important that BOB products are built for integration.
- 21% of organizations are consolidating security vendors; 25% are considering it.
Want more details? Check out this slide presentation from ESG and ISSA.
More resources:
- "Thanks to the economy, cybersecurity consolidation is coming. CISOs are more than ready." (Protocol)
- "Cybersecurity: Best-of-Breed Approach or Single-Vendor Platform?" (BizTech Magazine)
3 -- Everything you always wanted to know about ransomware but were afraid to ask
Ransomware has thrived through constant evolution, becoming a multimillion-dollar, self-sustaining industry and a major cyberthreat to all organizations. That’s why Tenable Research’s new report “The Ransomware Ecosystem” is a must-read. It explores the key players in the ransomware ecosystem and the tactics that have helped it flourish.
You’ll learn:
- How the ecosystem evolved
- Which are the most common attack vectors
- How to prepare and defend against attacks
- What vulnerabilities are likely to be exploited
For more information:
- Read the blog “Understanding the Ransomware Ecosystem”
- Download the full report
- Watch Satnam Narang, Tenable Senior Staff Research Engineer, discuss the report
- Attend the July 13 webinar
4 -- Study: Manual cloud asset management impacts visibility, ups risk
Cloud adoption keeps accelerating, but have organizations automated their inventorying of public cloud assets? Unfortunately, not that much. And that’s not good because it leads to undercounts and to incomplete asset visibility, increasing security risks, a study found.
The study – “Measuring Risk and Risk Governance” from the Cloud Security Alliance and Google – polled 600 security practitioners and 20 executives in companies of all sizes globally and found that internal data classification schemes (55%) and manual methods (50%) are the main ways organizations collect, track and organize cloud assets. Only 21% of respondents use native or automated cloud data classification tools.
Unsurprisingly, organizations using manual estimation methods reported having an average of 124 cloud services, 31% fewer than the average of 163 reported by organizations using automated discovery tools.
For more information about the study, whose main goal was to assess the maturity of public cloud and risk management within the enterprise, read:
- "Risk Disconnect in the Cloud" (Dark Reading)
- "Majority of security teams don’t analyze ongoing risk as cloud services evolve" (SC Magazine)
Interested in cloud security? Check out these resources:
- “The Four Phases of Cloud Security Maturity” (On-demand Tenable webinar)
- “How Security Leaders Can Become Dev and Ops Whisperers” (Tenable blog)
- “A Practical Approach for Shifting Left” (Tenable blog)
5 -- ID-related breaches: They’re rising and wreaking havoc
How prevalent have identity-related breaches become? A whopping 84% of 500 respondents to a recent survey said their organization has experienced one in the last year. Findings from the study “2022 Trends in Securing Digital Identities” by the Identity Defined Security Alliance (IDSA) include:
- Identity growth continues, which makes it a security priority.
- Identity-related attacks are up but can be prevented.
- Risky behavior drops when executives focus on identity security.
More resources on identity access management:
- “Five Ways to Strengthen Active Directory Security for Large Enterprises” (On-demand Tenable webinar)
- “Active Directory Holds the Keys to Your Kingdom, But Is It Secure?” (Frost & Sullivan white paper)
- “Identity Threat Roundup Q1 2022” (Tenable white paper)
6 -- Vulnerabilities to have on your radar screen
These vulnerabilities deserve special attention:
Flaws in Azure Synapse Analytics
56 insecure-by-design OT vulnerabilities discovered by Forescout
Vulnerabilities in Citrix’s Application Delivery Management product
POC published for unauthenticated RCE in Zoho ManageEngine ADAudit Plus
Flaws in Azure Synapse Analytics
Cloud security presents special challenges, as exemplified by Tenable’s recent discovery and analysis of two vulnerabilities in Microsoft Azure. The Tenable Research team found the serious flaws in Azure Synapse Analytics, contacted Microsoft and let’s just say the communication wasn’t particularly smooth. “These flaws and our researchers’ interactions with Microsoft demonstrate the difficulties involved in addressing security-related issues in cloud environments,” the Tenable team wrote.
For more details:
- “Microsoft Azure Synapse Pwnalytics” (Tenable TechBlog)
- “Tenable slams Microsoft over Azure vulnerabilities” (TechTarget)
- “A ‘Pattern of Behavior’ for Microsoft?” (Protocol)
- “Botched and silent patches from Microsoft put customers at risk, critics say” (Ars Technica)
- “Microsoft Criticized For Lack Of Transparency And Speed In Fixing Vulnerabilities” (IT World Canada)
You can also read Tenable CEO Amit Yoran’s LinkedIn post “Microsoft’s Vulnerability Practices Put Customers At Risk” and listen to Tenable CSO Robert Huber’s comments on KBI’s KBKast.
Forescout: 56 insecure-by-design OT vulnerabilities
Forescout’s Vedere Labs published its latest research findings into OT vulnerabilities titled “OT:ICEFALL,” including 56 bugs across multiple vendors’ products. “OT:ICEFALL sought to analyze and understand the prevalence and impact of insecure-by-design vulnerabilities in OT products,” wrote Tenable’s Security Response Team.
For more information:
- Watch Forescout’s Vedere Labs on-demand webinar about its findings
- Read “ICS Vendors Respond to OT:Icefall Vulnerabilities Impacting Critical Infrastructure” (SecurityWeek)
- Read "CISA Releases Security Advisories Related to OT:ICEFALL Report" (CISA)
- Read “Why OT:ICEFALL is a Big Concern for Industry 4.0 Networks” (NetworkComputing)
- Read “Dozens of insecure-by-design flaws found in OT products” (CSO Magazine)
- Read “How Can We Strengthen the Cybersecurity of Critical Infrastructure?” (Tenable blog)
Vulnerabilities in Citrix’s Application Delivery Management product
Citrix disclosed a pair of vulnerabilities in Citrix Application Delivery Management (ADM), a centralized management solution used to monitor a variety of Citrix networking products:
- CVE-2022-27511, an improper access control vulnerability in Citrix ADM
- CVE-2022-27512, a vulnerability in Citrix ADM caused by improper control of a resource through its lifetime
For the details, read Tenable’s blog.
POC published for unauthenticated RCE in Zoho ManageEngine ADAudit Plus
The researchers who recently discovered CVE-2022-28219, a now patched vulnerability in Zoho ManageEngine ADAudit Plus, have shared a proof-of-concept (PoC) script that automates the steps to pivot from an XML external entity (XXE) flaw to remote code execution (RCE).
This vulnerability impacts all versions of ADAudit Plus builds below 7060, so organizations should make sure they're running the fixed or later version of ADAudit Plus, which is a compliance tool for monitoring Active Directory.
For more information, read Tenable's blog.
Learn more
- Asset Management
- Cloud
- Compliance Monitoring
- Cybersecurity Snapshot
- Risk-based Vulnerability Management
- Shadow IT
- Vulnerability Management




Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success