by Cesar Navas
Tenable Research delivers world class exposure intelligence, data science insights, zero day research and security advisories. Our Security Response Team (SRT) in Tenable Research tracks threat and vulnerability intelligence feeds to make sure our research teams can deliver sensor coverage to our products as quickly as possible. The SRT also works to dig into technical details and author white papers, blogs, and additional communications to ensure stakeholders are fully informed of the latest cyber risks and threats. The SRT provides breakdowns for the latest critical vulnerabilities on the Tenable blog.
When security events rise to the level of taking immediate action, Tenable - leveraging SRT intelligence - notifies customers proactively to provide exposure information, current threat details and how to use Tenable products and capabilities to accelerate remediation.
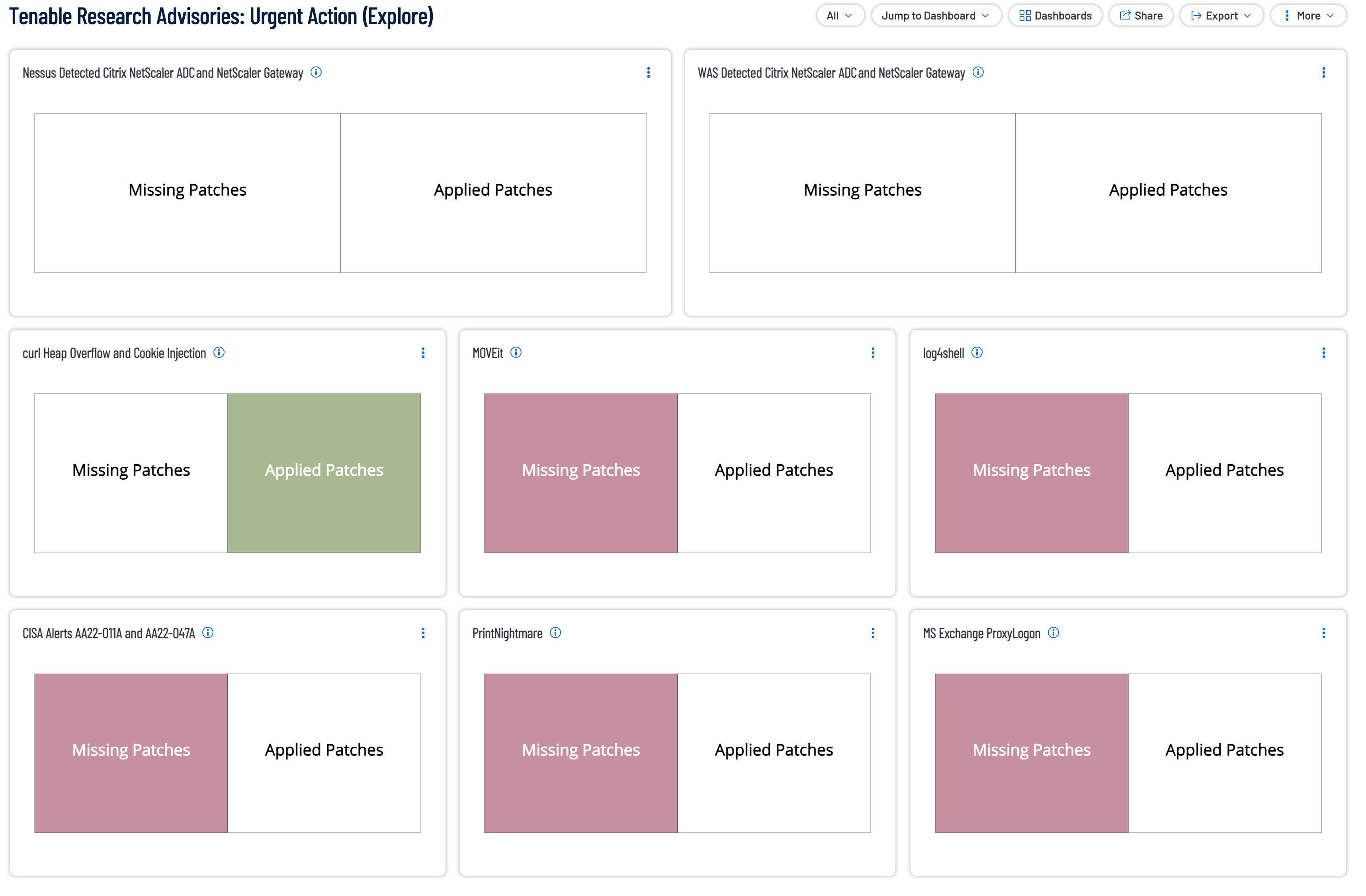
This dashboard contains indicator style widgets to highlight any vulnerabilities related to the Tenable Research Advisories where Tenable issues customer guidance that immediate remediation was of paramount importance to all affected organizations. Tenable recommends addressing missing patches as identified in the dashboard components.
The following widgets are included in this dashboard are:
Research Advisories - Citrix NetScaler ADC and NetScaler Gateway: In August 2023, Mandiant identified a zero-day exploitation impacting NetScaler ADC and NetScaler Gateway appliances. When NetScaler ADC or NetScaler Gateway is configured as a gateway (VPN virtual server, ICA Proxy, CVPN, RDP Proxy) or as an AAA virtual server, an unauthenticated attacker could exploit the device in order to hijack an existing authenticated session. Depending on the permissions of the account they have hijacked, this could allow the attacker to gain additional access within a target environment and collect other account credentials. Successful exploitation allows the attacker to bypass multi factor authentication (MFA) requirements.
Research Advisories - curl Heap Overflow and Cookie Injection: On October 3, an open-source developer and maintainer of curl, took to X (formerly Twitter) to announce that a new high severity CVE would be fixed in curl 8.4.0. The developer noted that the release would be ahead of schedule and released on October 11, indicating in a reply to the twitter thread that this is 'the worst security problem found in curl in a long time.'
Research Advisories - MOVEit: The CL0P Ransomware Group, also known as TA505, has exploited zero-day vulnerabilities across a series of file transfer solutions since December 2020. File transfer solutions often contain sensitive information from a variety of organizations. This stolen information is used to extort victims to pay ransom demands. In 2023, CL0P claimed credit for the exploitation of vulnerabilities in both Fortra’s GoAnywhere Managed File Transfer (MFT) and Progress Software’s MOVEit Transfer solutions.
Research Advisories - log4shell: This matrix alerts organizations to potential concerns regarding the Log4j vulnerability. Displayed are the vulnerabilities that are directly associated with the log4shell CVEs (CVE-2021-44228, CVE-2021-44832, CVE-2021-45046, CVE-2021-4104, and CVE-2021-45105) and Log4j installations.
Research Advisories - CISA Alerts AA22-011A and AA22-047A: On November 3rd, 2021, Cybersecurity and Infrastructure Security Agency (CISA) issued Binding Operational Directive (BOD) 22-01, and on Jan 11, 2022 CISA issued an alert (AA22-011A) warning of increased risk to U.S. critical infrastructure. A total of 18 CVEs can be associated with this alert. Hosts and Vulnerabilities identified and mitigated are displayed using the referenced CVE.
Research Advisories - PrintNightmare: On July 1, Microsoft released an advisory for CVE-2021-34527. This advisory was released in response to public reports about a proof-of-concept (PoC) exploit for CVE-2021-1675, a similar vulnerability in the Windows Print Spooler. To help clear up confusion about the vulnerability, Microsoft updated its advisory for CVE-2021-1675 to clarify that it is similar but distinct from CVE-2021-34527. On July 6, Microsoft updated its advisory to announce the availability of out-of-band patches for CVE-2021-34527, a critical vulnerability in its Windows Print Spooler that researchers are calling PrintNightmare. This remote code execution (RCE) vulnerability affects all versions of Microsoft Windows.
Research Advisories - MS Exchange ProxyLogon: On March 2, 2021 Microsoft released several critical security updates for zero-day Microsoft Exchange Server vulnerabilities, and reported that the exploits are actively being exploited by threat actors. Within a single week thousands of organizations world-wide have fallen victim. Tenable released several plugins for Exchange Server 2010, 2013, 2016 and 2019, which can be used to determine which Exchange Server systems are vulnerable in your environment.
Tenable One
Request a demo
The world’s leading AI-powered exposure management platform.
Thank You
Thank you for your interest in Tenable One.
A representative will be in touch soon.
Form ID: 7469
Form Name: one-eval
Form Class: c-form form-panel__global-form c-form--mkto js-mkto-no-css js-form-hanging-label c-form--hide-comments
Form Wrapper ID: one-eval-form-wrapper
Confirmation Class: one-eval-confirmform-modal
Simulate Success