Discover, prioritize, and remediate vulnerabilities, misconfigurations, identity,
and
data risks, across
multi-cloud environments.
-
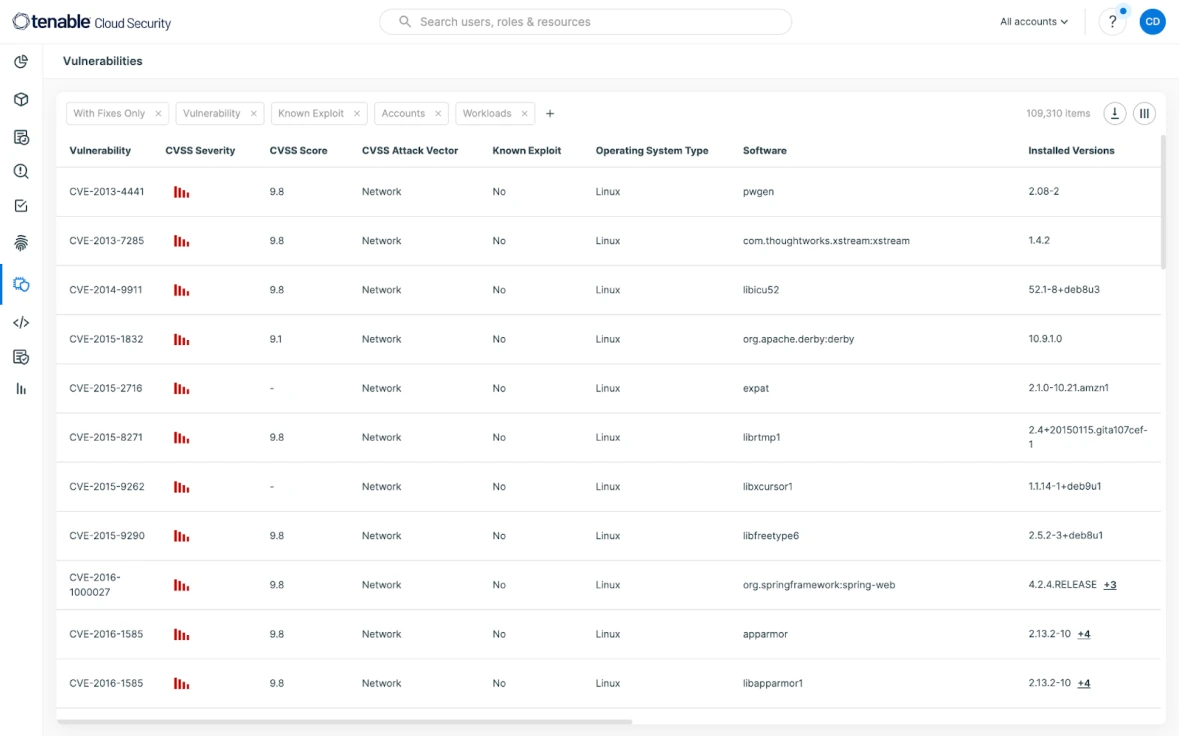
Cloud-Native Vulnerability Mgmt. Get prioritized visibility into every cloud resource
from development to runtime. -
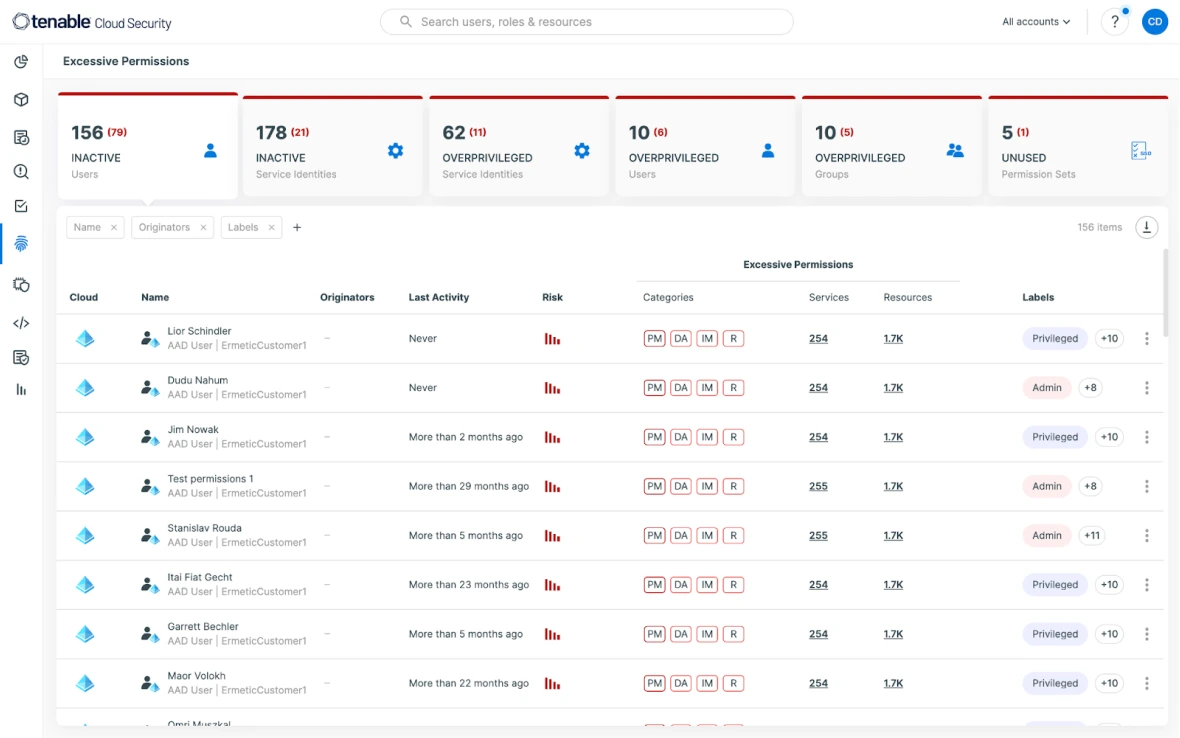
Enforce Least Privilege. Leverage the intuitive UI to attain the least privilege without disrupting productivity.
-
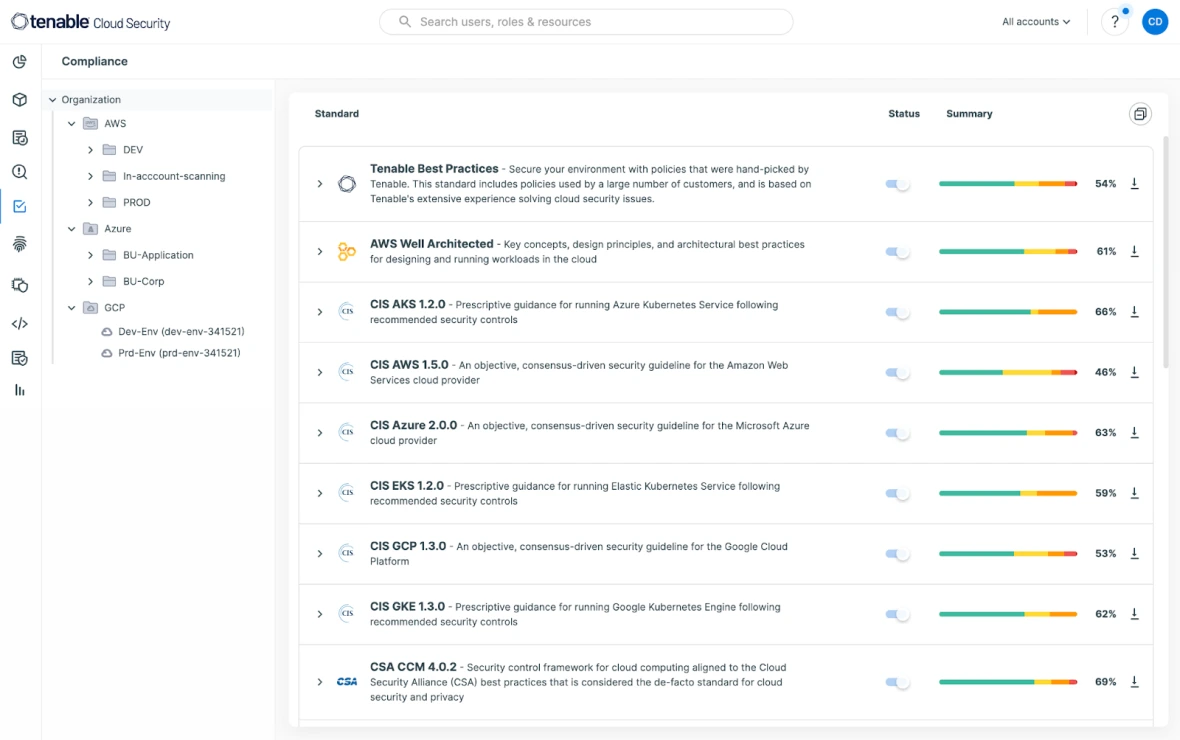
Automate Compliance. Eliminate audit fire drills. Verify and automatically
report on compliance frameworks.
Demandez une démo de Tenable Cloud Security
Une sécurité du cloud unifiée exceptionnelle vous attend !
We'll show you exactly how Tenable Cloud Security helps you deliver
multi-cloud asset discovery, prioritized risk assessments and
automated compliance/audit
reports.
Join 40,000+ organizations automating their cloud security with the leading independent provider

Une sécurité du cloud adaptée à vos besoins uniques
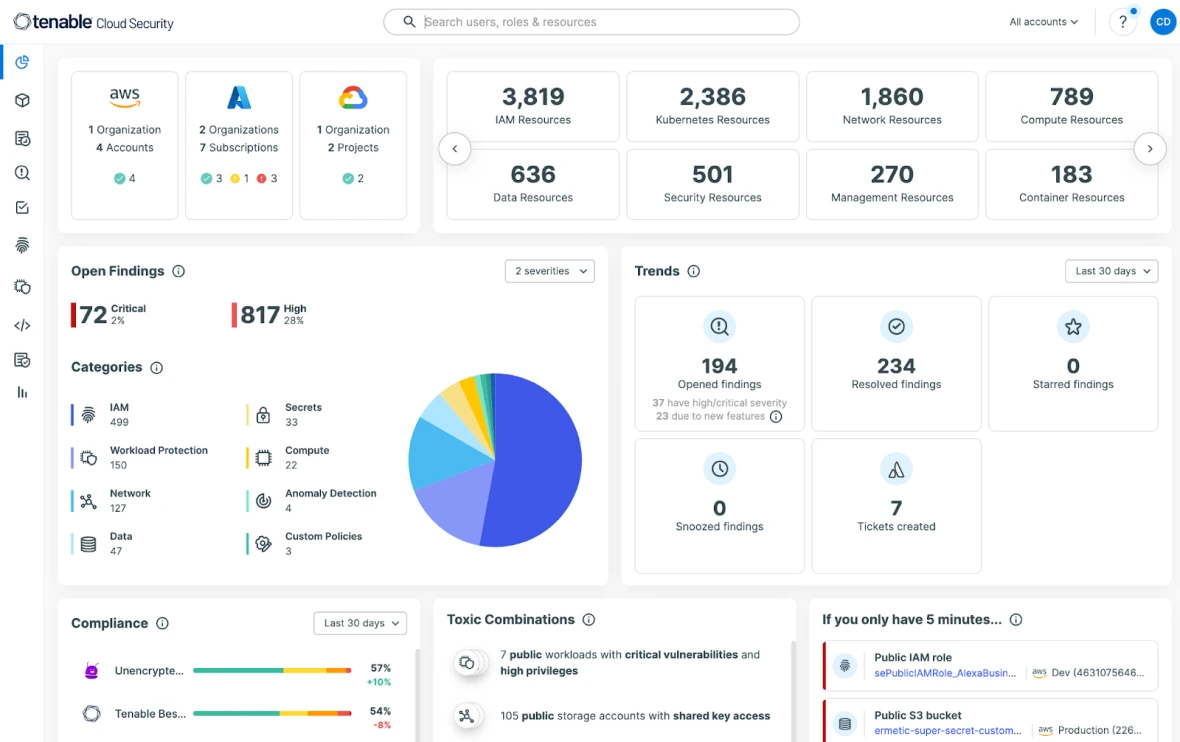
Get full visibility across AWS, Azure, GCP, and Oracle Cloud Infrastructure (OCI) with 100% agentless scanning. Continuously discover your cloud environment across infrastructure, workloads, identities, and data, powerfully visualizing all your cloud assets. Obtain a unified view that simplifies your team’s understanding of even the most complex issues.
Try for free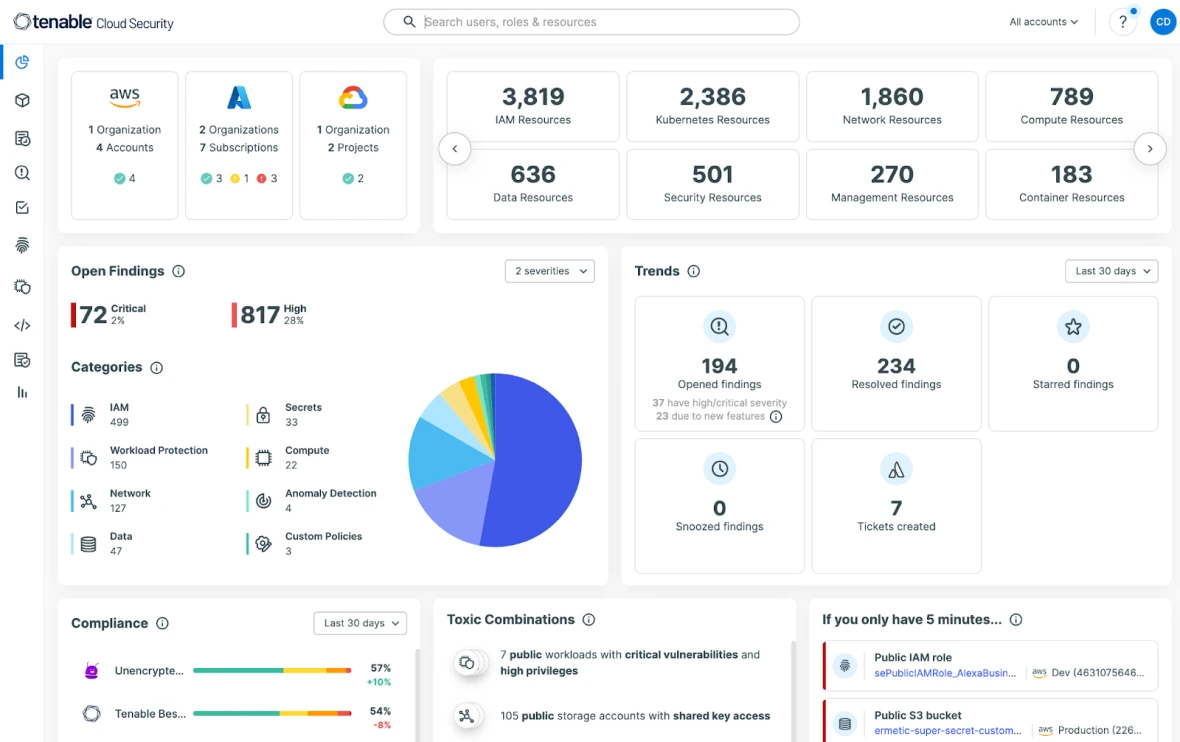
Supervisez le risque en réalisant l'examen et l'évaluation en continu des paramètres et des configurations d'environnement cloud. En mettant en correspondance les risques découverts avec les normes et les politiques de sécurité, vous pouvez atteindre et maintenir la conformité. Il est aussi possible de répondre facilement aux audits dans les environnements multicloud.Tirez parti des rapports intégrés pour plus de 20 frameworks, parmi lesquels SOC-2, GDPR, PCI DSS, HIPAA, ou NYDFS.
Try for free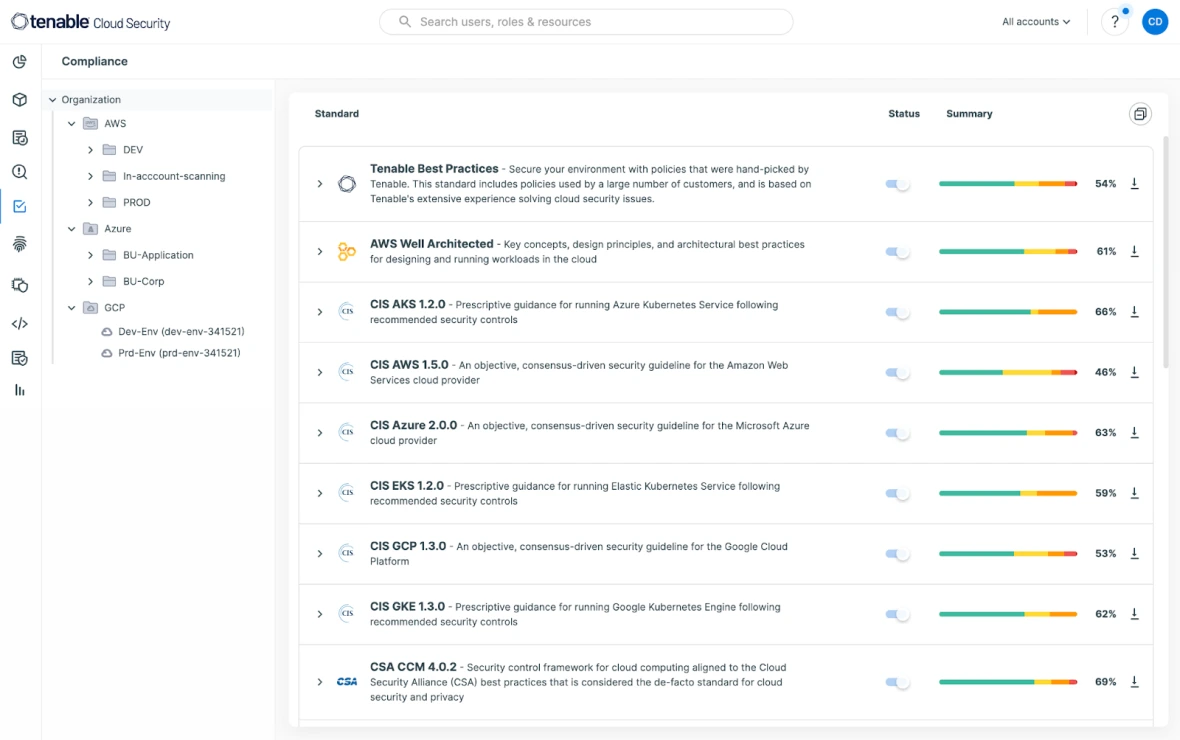
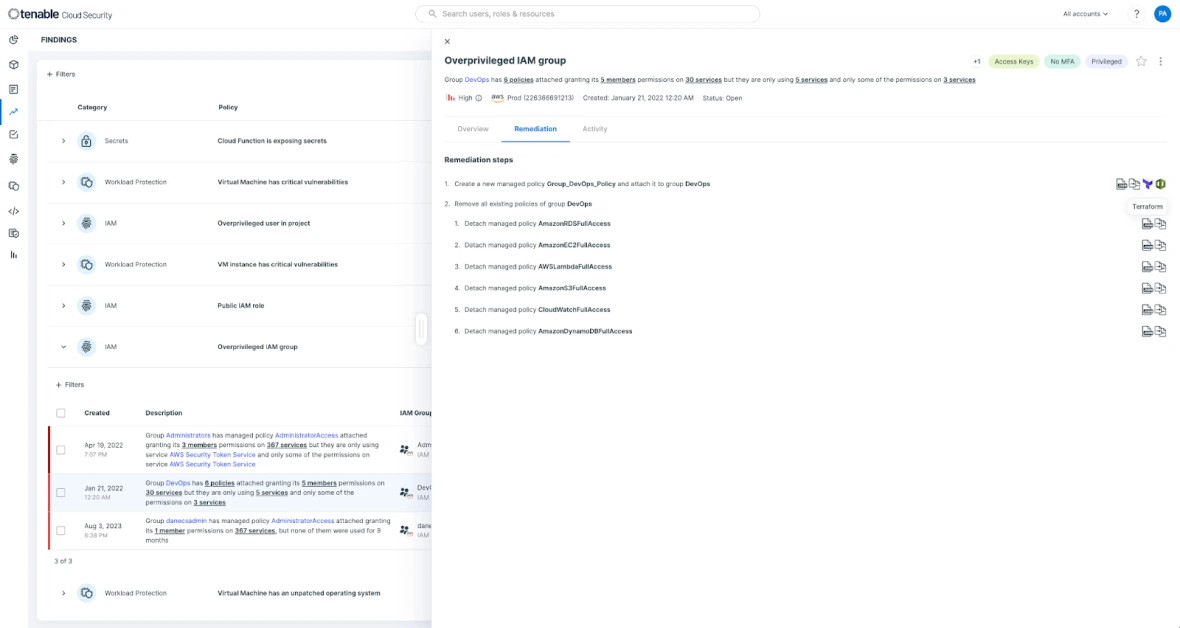
Tenable is a cloud security solution that allows you to focus on the risks that matter most. Tenable Cloud Security gives users deeply prioritized findings that empower Security and DevSecOps teams to automate threat detection and remediation efforts at scale. Mitigate and remediate risky privileges and faulty configurations using auto-generated and customizable policies by seamlessly integrating across ticketing, CI/CD pipelines, IaC, and other workflows.
Try for free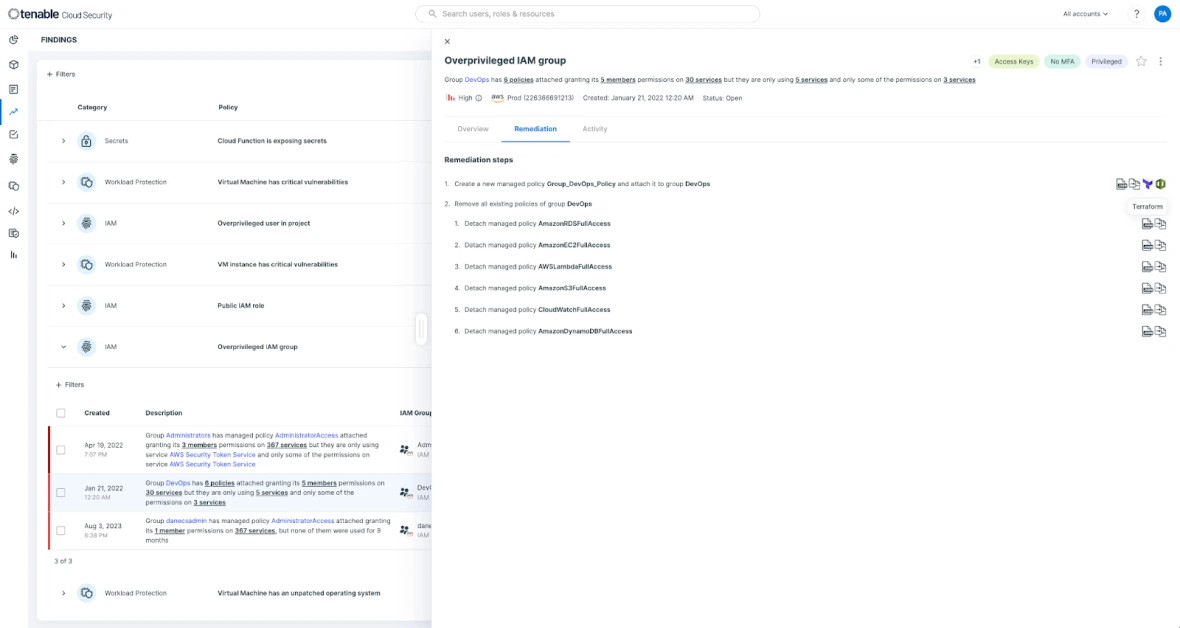
Identifiez les activités anormales et suspectes en évaluant en permanence les risques par rapport à des lignes de base comportementales. Analyze cloud provider logs and link cloud threats with underlying architecture to show the context associated with each risk quickly.
Try for free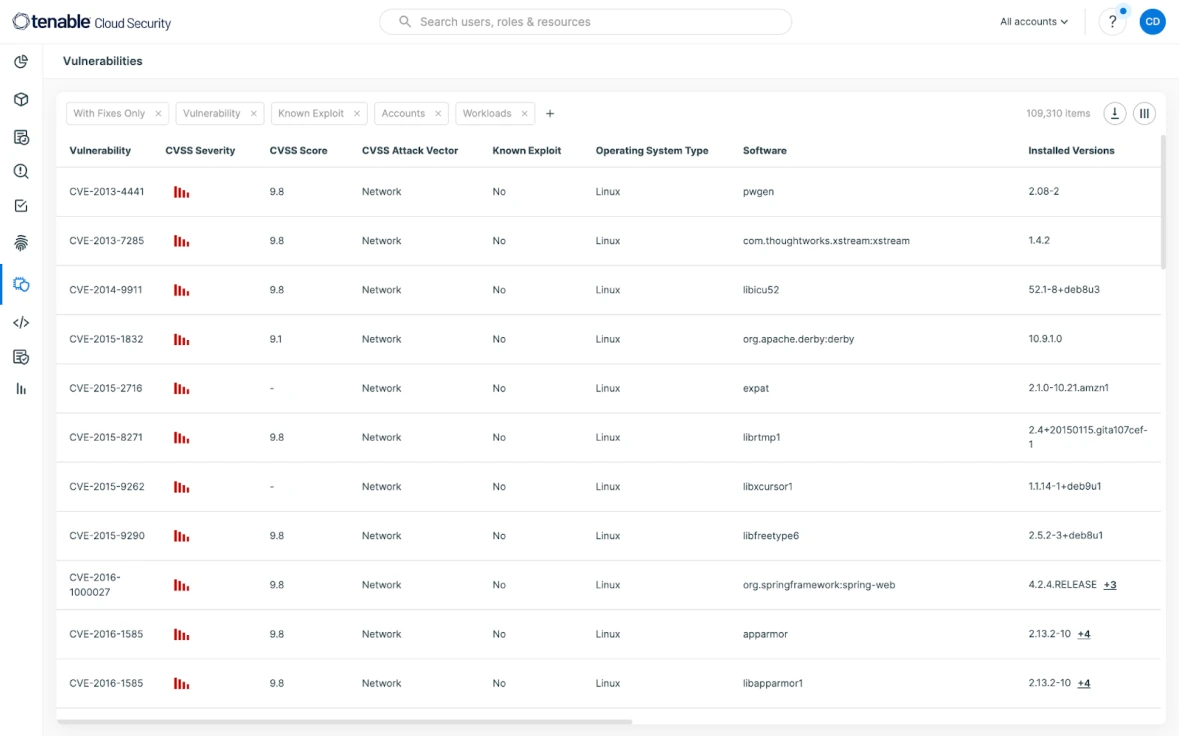
Build zero trust in your cloud security infrastructure. Minimisez les permissions excessives pour les services et les personnes, sans rien casser.Le chemin vers le moindre privilège commence par une image complète et précise de tous les droits. Continuously discover all entities and policies (including IAM, resource, permissions boundaries, and ACLs) in the environment and analyze the relationships to reveal the gap between desired enterprise policy and actual entitlements.
Try for free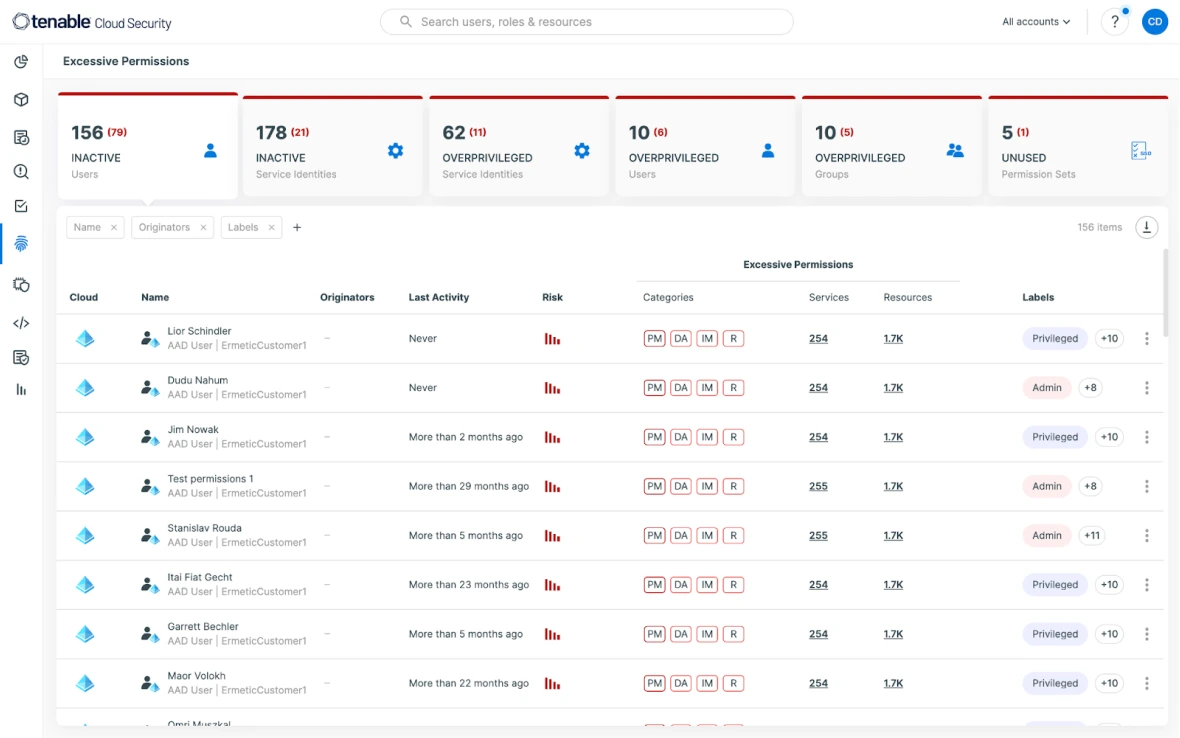




Lisez l'eBook pour en savoir plus sur :
- How to protect workloads and manage vulnerabilities
- Securing identities and entitlements and enforcing least privilege
- Ways to accelerate cloud detection and response
- How to assess and prioritize risk across cloud environments